Incident Overview: CVE-2026-22769
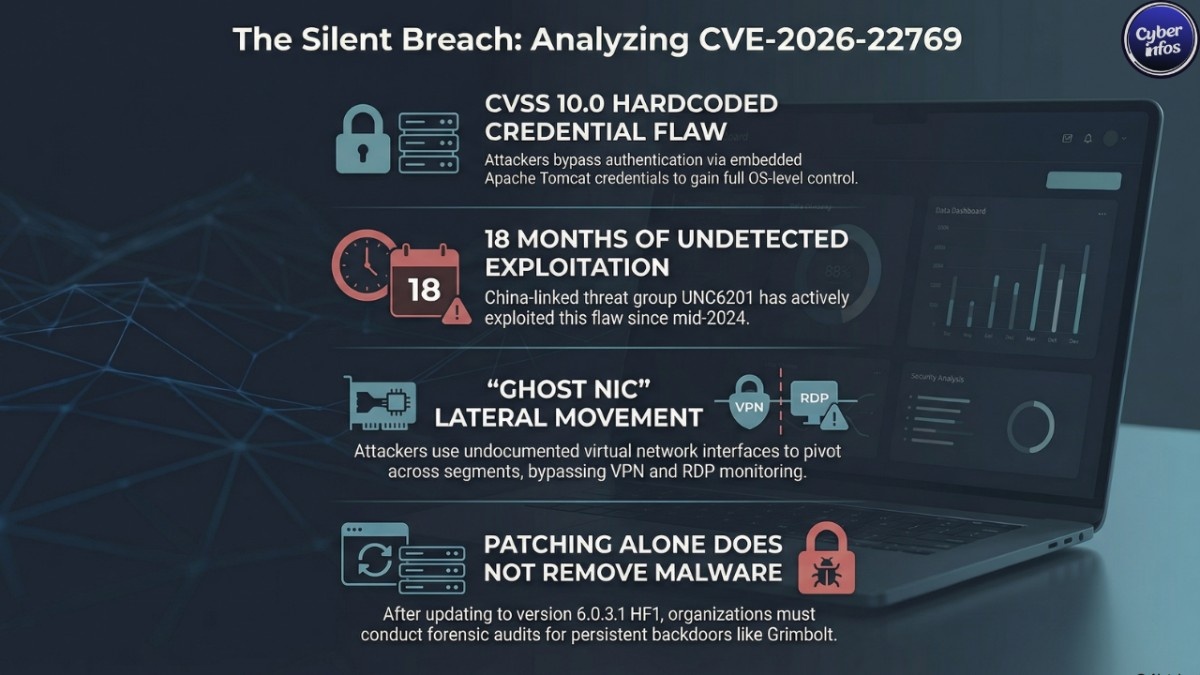
The vulnerability at the center of this campaign is a hardcoded credential flaw (CWE-798) embedded within the RecoverPoint appliance.
- Severity: CVSS 10.0 (Critical)
- Access Required: None (if interface is reachable)
- Impact: Unauthenticated login leading to full OS-level compromise
- Affected Versions: Prior to 6.0.3.1 HF1 and certain 5.3.x builds
The issue stems from static administrative credentials inherited from the appliance’s Apache Tomcat configuration. If attackers knew the embedded password, they could authenticate directly no phishing, no brute force, no privilege escalation required.
Dell addressed the issue in advisory DSA-2026-079 and strongly recommends upgrading immediately.
What Is Dell RecoverPoint for Virtual Machines?
Dell RecoverPoint for Virtual Machines integrates directly with:
- VMware vSphere
- VMware vCenter
It enables:
- Continuous VM replication
- Point-in-time recovery
- Cross-site disaster recovery
- Backup integrity management
Because RP4VM sits close to production workloads and often within management networks, compromise provides:
- Access to replicated VM data
- Visibility into infrastructure topology
- Potential tampering with backup integrity
- A pivot point into core VMware estates
Backup appliances are often trusted implicitly. They rarely run endpoint detection agents and may not feed detailed telemetry into SIEM platforms. That blind spot makes them appealing targets.
Who Is Behind the Exploitation?
The activity has been attributed to a China-linked threat cluster known as UNC6201, tracked by Mandiant and Google Threat Intelligence Group (GTIG).
The group has demonstrated a consistent operating model:
- Target infrastructure and edge appliances
- Avoid noisy intrusion methods
- Maintain long dwell times
- Continuously refine malware tooling
Researchers observed deployment of two primary backdoors: Brickstorm and the newer Grimbolt. In some environments, Brickstorm was replaced over time by Grimbolt, suggesting active maintenance of access rather than one-off exploitation.
How the Dell RecoverPoint Zero-Day Was Exploited
1. Initial Access via Tomcat Manager
Attackers authenticated to the embedded Apache Tomcat Manager interface using the hardcoded admin credentials. Because authentication was technically valid, this activity could blend into normal administrative traffic.
2. Root Access and Persistence
Once inside, attackers escalated privileges to root and modified legitimate startup scripts specifically convert_hosts.sh ensuring malware execution at boot via rc.local. This persistence mechanism leveraged existing system behavior rather than introducing obvious new services.
3. Malware Deployment
The following malware families were observed:
- Brickstorm: A Go-based backdoor targeting VMware infrastructure
- Grimbolt: A C# implant optimized for stealth and performance on resource-constrained appliances
- Slaystyle: Used for additional post-exploitation operations
Grimbolt appears engineered to reduce static detection signatures and improve runtime efficiency an evolution that reflects operational maturity.
4. “Ghost NIC” Lateral Movement
Investigators observed the creation of temporary or undocumented virtual network interfaces sometimes referred to as “Ghost NICs” on ESXi hosts. These allowed attackers to pivot across network segments without using traditional remote access pathways like VPN or RDP.
Who Is Most at Risk?
Organizations most at risk include:
- Enterprises running unpatched RP4VM versions
- Government and critical infrastructure operators
- Large VMware-based data centers
- Organizations exposing management interfaces externally
Even internally exposed appliances can present risk if attackers gain a foothold elsewhere in the network. Given the extended exploitation window, organizations should treat vulnerable deployments as potentially compromised.
Protection & Mitigation Steps
Upgrade Immediately
- Install version 6.0.3.1 HF1 or later
- Follow Dell’s upgrade path for 5.3.x environments
Patching prevents new exploitation but does not remove existing persistence mechanisms.
Assume Potential Compromise
- Review Tomcat Manager access logs
- Inspect startup scripts for modifications
- Search for unfamiliar binaries
- Audit ESXi hosts for undocumented NICs
Restrict Management Exposure
- Remove public access to management interfaces
- Limit access to dedicated management VLANs
- Enforce VPN and MFA for administrative access
Rotate and Audit Credentials
- Reset administrative credentials post-patch
- Review service accounts tied to VMware management
- Enable MFA where supported
Enhance Monitoring
- Forward RP4VM logs into SIEM
- Alert on startup script changes
- Monitor for unexpected virtual NIC creation
Strategic Takeaways
This Dell RecoverPoint zero-day vulnerability highlights a growing pattern: attackers are targeting infrastructure appliances that blend into enterprise environments. Backup platforms, hypervisors, storage systems, and management tools are increasingly attractive because they combine high privilege with low monitoring.
Security strategies that focus exclusively on endpoints leave dangerous blind spots. Virtualization and disaster recovery infrastructure must now be treated as Tier-1 monitored assets.
FAQ: Dell RecoverPoint Zero-Day Vulnerability
What is the Dell RecoverPoint zero-day vulnerability?
CVE-2026-22769 is a hardcoded credential flaw that allows unauthenticated attackers to gain root access to vulnerable RecoverPoint for Virtual Machines appliances.
How long was the vulnerability exploited?
Researchers assess that exploitation began in mid-2024 and continued for approximately 18 months before public disclosure.
Does patching remove malware?
No. Patching blocks new exploitation but does not automatically remove persistence mechanisms. A forensic review may be required.
Was ransomware involved?
Public reporting indicates espionage-focused activity rather than ransomware deployment.
Should backup appliances be internet-facing?
Best practice is to restrict management interfaces to isolated networks protected by strong authentication controls.
Final Thoughts
The Dell RecoverPoint zero-day vulnerability serves as a reminder that attackers increasingly target the systems organizations rely on for resilience. When backup platforms are compromised, the consequences extend beyond data access they affect trust, recovery capability, and operational continuity.
If your organization runs RecoverPoint, prioritize patching immediately. Then go further: review logs, audit persistence mechanisms, and validate that your disaster recovery platform is not quietly serving as an attacker foothold.