A newly disclosed n8n supply chain attack has revealed how threat actors abused community-maintained npm packages to steal sensitive OAuth credentials from developers and organizations, according to a report published this week by Endor Labs.
The attackers uploaded malicious packages to the npm registry that posed as legitimate n8n community nodes, including a fake Google Ads integration. Once installed, these packages captured OAuth tokens during normal workflow execution and transmitted them to attacker-controlled servers, researchers confirmed.
The incident highlights growing security risks associated with third-party integrations in workflow automation platforms increasingly used for business-critical operations.
How the Attack Was Discovered
According to Endor Labs, the malicious activity was identified during a supply chain investigation earlier this month. Researchers observed unusual outbound network traffic originating from n8n workflows that appeared otherwise legitimate.
“This campaign exploited workflow automation platforms that function as centralized credential vaults,” Endor Labs stated in its advisory. Unlike traditional npm malware that targets developer machines, the attackers focused on environments storing OAuth tokens and API keys for multiple SaaS services in one place.
The findings were publicly disclosed last week, and npm has since removed several of the identified packages.
Why n8n Became a High-Value Target
Security researchers say the n8n supply chain attack succeeded because of how the platform handles community nodes.
According to n8n’s official documentation, community nodes run with the same privileges as the core platform. This means they can:
- Read environment variables
- Access the file system
- Decrypt stored credentials
- Make outbound network requests
“Community nodes are not sandboxed or isolated,” Endor Labs researchers Kiran Raj and Henrik Plate explained. “A single malicious package can gain deep visibility into workflows and exfiltrate credentials without immediate detection.”
Because n8n often serves as a centralized automation hub, compromising one node can expose access to advertising platforms, payment processors, and customer data systems.
Malicious Packages Identified
Endor Labs confirmed at least eight npm packages were involved in the campaign. One of the most widely downloaded packages, n8n-nodes-hfgjf-irtuinvcm-lasdqewriit, masqueraded as a Google Ads node and recorded thousands of downloads before removal.
According to npm registry data reviewed by researchers, the malicious packages collectively reached tens of thousands of downloads, significantly increasing the potential impact.
The issue has been tracked under the security advisory GHSA-77g5-qpc3-x24r.
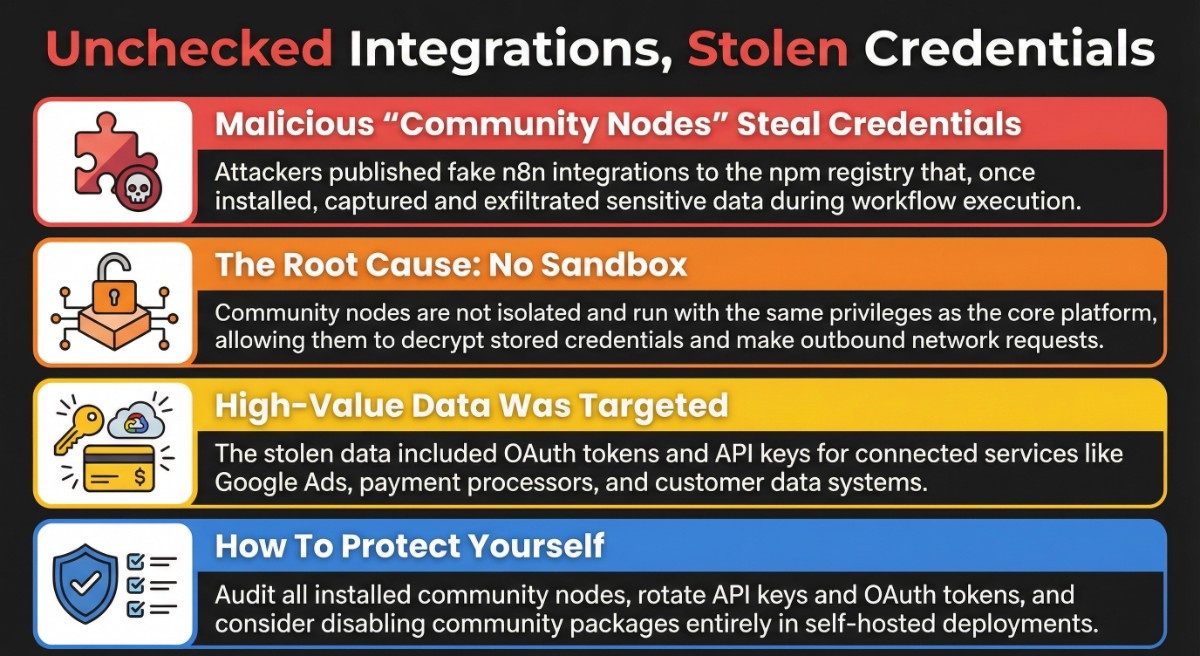
What Data Was Compromised
The attackers targeted OAuth credentials entered by users during node configuration. According to Endor Labs, the malicious code waited until workflows were executed, then decrypted stored tokens using n8n’s master key.
The stolen data included:
- Google Ads OAuth tokens
- API keys for connected services
- Credentials stored in n8n’s encrypted vault
Researchers warned that these credentials could allow attackers to manipulate advertising accounts, access financial services, or pivot into connected enterprise systems.
Current Status of the Incident
npm has removed the confirmed malicious packages from its registry. However, researchers say the threat may not be fully contained.
Endor Labs noted that some related packages remain available and that one suspicious update was published only hours before its report was released. “This suggests the campaign may still be active,” the company stated.
n8n has not reported a breach of its core infrastructure but has reiterated warnings about the risks of installing unverified community nodes.
What n8n Users Should Do Immediately
Security experts recommend the following actions for organizations using n8n:
- Audit all installed community nodes
- Remove unknown or unnecessary integrations
- Rotate OAuth tokens and API keys
- Monitor outbound traffic from n8n instances
- Use service accounts with minimal permissions
For self-hosted deployments, n8n advises disabling community packages entirely by setting:
N8N_COMMUNITY_PACKAGES_ENABLED=false
Industry Perspective on the n8n Supply Chain Attack
According to Endor Labs, this incident reflects a broader trend in supply chain attacks.
“Threat actors are moving up the stack,” the company stated. “Automation platforms, CI/CD tools, and orchestration systems now represent high-value targets because they aggregate credentials and control business processes.”
The campaign closely mirrors previous attacks targeting GitHub Actions workflows, indicating that attackers are systematically exploiting trusted automation ecosystems.
Official Statements
n8n has warned users that community nodes can execute arbitrary code on the host system and emphasized that they should be treated as untrusted software.
“Community packages inherit the same trust level as n8n itself,” the company stated in its security guidance. “Users are responsible for assessing the risk before installation.”
Endor Labs urged organizations to prioritize official integrations and implement stronger supply chain monitoring.
Frequently Asked Questions
Was n8n itself compromised?
No. According to researchers, the attack did not exploit a vulnerability in n8n’s core platform.
Who is most at risk?
Self-hosted users who enabled community nodes without strict review.
Is the threat ongoing?
Security researchers say follow-up activity is possible, and continued monitoring is advised.
Final Thoughts
The n8n supply chain attack demonstrates how trusted automation platforms have become prime targets for credential theft. As organizations rely more heavily on workflow automation, security teams must apply the same scrutiny to community integrations as they do to CI/CD pipelines and cloud infrastructure.
Cyber Infos will continue monitoring this developing situation and provide updates as new information becomes available.

