Incident Overview: What Is CVE-2026-1731?
CVE-2026-1731 is a pre-authentication remote code execution (RCE) vulnerability affecting:
- BeyondTrust Remote Support (RS) versions 25.3.1 and earlier
- BeyondTrust Privileged Remote Access (PRA) versions 22.1 through 24.3.4
- Legacy PRA versions prior to 22.1
The flaw stems from improper input validation that enables command injection through specially crafted WebSocket requests. An attacker can execute arbitrary operating system commands simply by interacting with an exposed internet-facing appliance.
According to reports from researchers and incident responders, exploitation activity began shortly after proof-of-concept (PoC) details became public. Within 24 hours of publication, internet-wide scanning was observed.
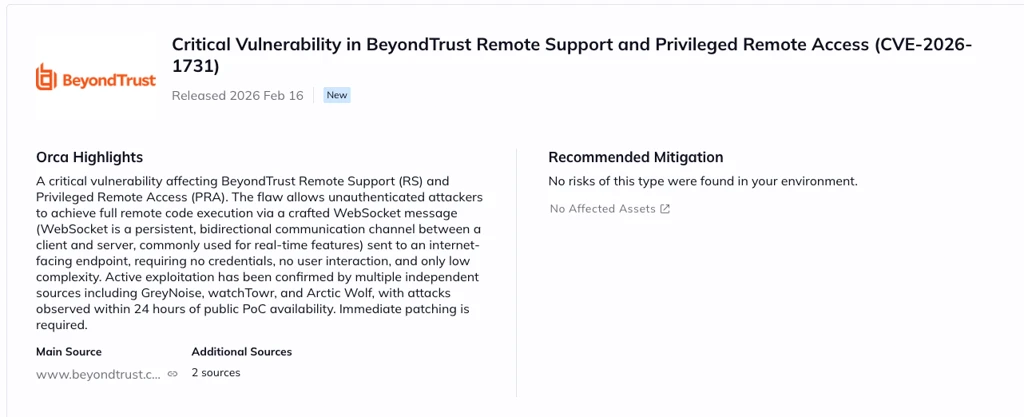
CISA formally added CVE-2026-1731 to its KEV catalog on February 13, 2026, signaling confirmed active exploitation and federal urgency.
How the CVE-2026-1731 Attack Works
The attack flow is technically straightforward almost alarmingly so.
Step 1: Reconnaissance
The attacker sends a GET request to:
/get_portal_info
This returns a configuration value (x-ns-company) required to establish a valid WebSocket session.
No authentication required.
Step 2: Malicious WebSocket Connection
Using that extracted value, the attacker connects to the /nw WebSocket endpoint and submits a crafted message containing a manipulated version string.
That string triggers command injection at the operating system level.
There are no credentials needed. No MFA prompts. No user clicks.
For security teams, that simplicity is the real danger. Once exploit code exists publicly and it does automation follows quickly.
Who Is at Risk?
Risk depends largely on deployment model.
SaaS Customers
BeyondTrust automatically patched hosted SaaS instances on February 2, 2026. If you’re fully cloud-hosted and received vendor confirmation, exposure is likely mitigated.
Self-Hosted and On-Premises Deployments
This is where the real exposure lies.
Security researchers have identified approximately 8,500 internet-exposed on-premises appliances. These systems remain vulnerable until administrators manually apply the appropriate patch or upgrade.
Organizations most at risk include:
- Enterprises using PRA for privileged vaulting
- Managed service providers (MSPs)
- Financial institutions with internal remote access gateways
- Healthcare providers using RS for support workflows
Because PRA often stores SSH keys, admin passwords, and session tokens, compromise may lead directly to domain-level access.
Post-Exploitation Activity Observed
Incident response teams have documented consistent attacker behavior after successful exploitation.
Observed techniques include:
- Deployment of SimpleHelp RMM, renamed and repurposed as a persistent backdoor
- Access to credential vaults containing passwords and SSH keys
- Lateral movement to internal systems
- Execution of
net userandnet groupfor privilege escalation - Creation of new administrative accounts
In other words, attackers are not just testing access they’re operationalizing it.
For organizations that exposed PRA externally before patching, compromise assessment should be considered mandatory.
Protection & Mitigation for CVE-2026-1731
If you haven’t patched yet, treat this as an emergency change window.
Immediate Actions
- Upgrade to RS 25.3.2+ or apply patch BT26-02-RS
- Upgrade PRA to 25.1.1+ or apply patch BT26-02-PRA
- Upgrade legacy PRA to a supported version before patching
If patching cannot occur immediately:
- Restrict access using IP allowlists or VPN enforcement
- Block or monitor WebSocket traffic to the
/nwendpoint at your WAF - Temporarily disable the web portal if exposure cannot be controlled
Detection & Threat Hunting
Security teams should:
- Monitor child processes spawned by the BeyondTrust service account
- Investigate unexpected executions of
curl,wget,bash, orsh - Review Windows logs for
net userandnet groupcommands - Check for renamed binaries in
C:\ProgramData\or Linux equivalents - Audit vault access logs for unusual retrieval activity
Assume breach if exposure occurred before remediation.
Official Commentary and Industry Response
The inclusion of CVE-2026-1731 in the CISA Known Exploited Vulnerabilities catalog significantly raises the urgency level for federal agencies and contractors.
Multiple security vendors have also issued detection guidance and threat intelligence updates, noting automated exploitation attempts.
The pattern mirrors previous high-impact remote access appliance vulnerabilities: once public exploit details appear, opportunistic and targeted actors move quickly.
Additional Safety Considerations
- Rotate all privileged credentials stored in PRA
- Revoke and reissue SSH keys if vault exposure is suspected
- Revalidate MFA enforcement for all admin workflows
- Review outbound connections from the appliance for suspicious C2 traffic
- Conduct a full forensic review if the system was internet-facing
For many organizations, BeyondTrust appliances sit at the intersection of identity, access, and infrastructure. Treating them as “just another appliance” underestimates their strategic importance.
FAQ: CVE-2026-1731
Is CVE-2026-1731 actively exploited?
Yes. Active exploitation has been confirmed, and CISA added it to the KEV catalog on February 13, 2026.
Does CVE-2026-1731 require authentication?
No. It is a pre-authentication RCE vulnerability, meaning attackers do not need credentials or user interaction.
Are SaaS customers vulnerable?
BeyondTrust automatically patched SaaS instances on February 2, 2026. Self-hosted deployments require manual updates.
What makes CVE-2026-1731 especially dangerous?
Because it affects privileged access infrastructure, successful exploitation may expose credential vaults, SSH keys, and session tokens allowing rapid lateral movement.
Should we assume compromise if exposed?
If your appliance was internet-facing and unpatched after disclosure, organizations should strongly consider conducting a compromise assessment.
Final Thoughts
CVE-2026-1731 is not simply another remote code execution vulnerability it targets the very systems designed to protect privileged access. The combination of pre-auth exploitation, public PoCs, and active scanning activity makes it a high-priority threat for enterprises.
Organizations running BeyondTrust Remote Support or Privileged Remote Access must patch immediately, restrict exposure, and assess for compromise if internet-facing systems were left unpatched.
With vulnerabilities like CVE-2026-1731, speed matters but so does thoroughness.