Cyber threats have just switched from being just an IT headache to a major national security risk – right up there with terrorism and economic espionage. The Trump Cybersecurity Executive Order 2026 is a big part of the US government’s plan to take on the global cybercrime problem, specifically the massive issue of ransomware, phishing junk and financial scams that are plaguing businesses and regular citizens.
The fact that cybercrime is costing the world economy trillions every year has got governments all over the globe getting their acts together to strengthen their defences and crack down on the international networks of cybercrime that are out there.
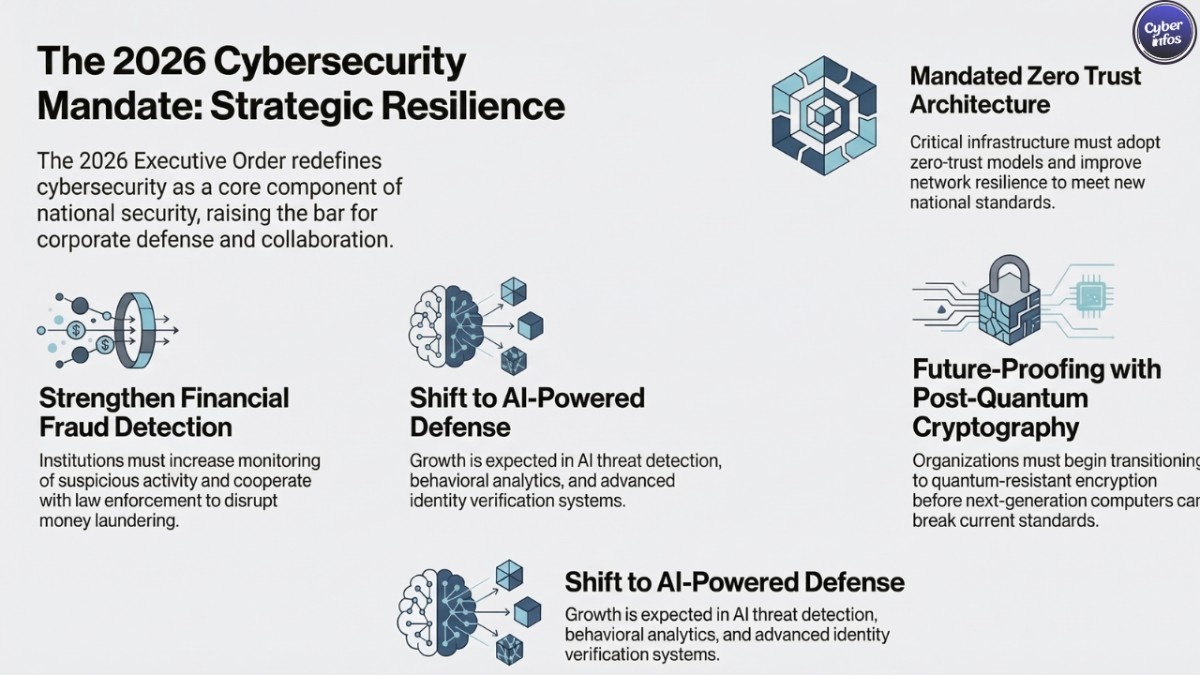
Under President Trump, the US is taking a harder line on cyber security, with a new strategy that’s all about making the government and big business work better together, properly protecting the key bits of our infrastructure and being at the forefront of new tech like AI & future-proof cryptography – it looks like the government is getting pretty serious about stopping cybercrime and stopping financial scams online.
What Is the Trump Cybersecurity Executive Order 2026?
The Trump Cybersecurity Executive Order 2026 is a federal directive designed to dismantle large-scale cybercrime networks operating across international borders. That’s not a small task. [PDF]
Many of today’s cybercrime operations function like multinational corporations distributed teams, infrastructure spread across several countries, and financial pipelines designed specifically to evade law enforcement.
The order focuses heavily on transnational criminal organizations (TCOs) responsible for cyber-enabled crimes including:
- Ransomware attacks
- Phishing campaigns
- Online fraud and financial scams
- Sextortion operations
- Identity theft networks
These criminal groups often operate across jurisdictions where legal cooperation is slow or inconsistent. That’s part of the reason they’ve thrived.
The executive order directs federal agencies to conduct a comprehensive review of available tools to combat cybercrime. Those tools include:
- Operational cybersecurity capabilities
- Intelligence gathering
- Diplomatic pressure
- Regulatory enforcement
- Financial tracking and asset seizure
Think of it less as a single policy change and more as a coordination order. The government wants every lever — technical, financial, and diplomatic aligned toward dismantling cybercrime infrastructure.
A key element is the creation of a specialized operational unit within the National Coordination Center (NCC). This unit will coordinate efforts across federal agencies while working closely with private cybersecurity firms that often detect these threats first.
And that collaboration piece matters. A lot. According to government estimates, cybercrime cost American victims over $12.5 billion in 2024 alone. That figure comes from reported incidents meaning the real number is almost certainly higher. Much higher.

The New U.S. Cyber Strategy
Alongside the executive order, the White House released a broader framework titled “President Trump’s Cyber Strategy for America.”
Interestingly, it’s far shorter than previous federal cybersecurity strategies, which often ran hundreds of pages and gathered digital dust shortly after publication. This one is leaner. More direct.
But it still outlines six major pillars shaping U.S. cyber policy.
1. Shaping Adversary Behavior
The strategy emphasizes influencing adversaries through both defensive and offensive cyber operations.
Rather than waiting for attacks and responding afterward, the government intends to disrupt threat actors before they strike.
That shift reflects a growing belief among policymakers: purely defensive cybersecurity doesn’t work when attackers operate globally and face minimal consequences.
2. Streamlining Cybersecurity Regulations
Ask any large company about cybersecurity compliance and you’ll hear the same complaint — overlapping regulations from multiple agencies.
Different reporting rules. Different frameworks. Different expectations.
The strategy proposes efforts to simplify and align cybersecurity compliance requirements, ideally reducing regulatory complexity while still maintaining strong security standards.
Whether that actually happens is another question. But the intent is there.
3. Modernizing Federal Cybersecurity
Federal networks are enormous. They’re also prime targets.
The government plans to modernize these systems using technologies such as:
- Artificial intelligence-based threat detection
- Zero trust architectures
- Advanced network monitoring
These upgrades aim to reduce vulnerabilities in federal infrastructure while improving the government’s ability to detect intrusions quickly. And frankly, that modernization has been overdue for years.
4. Protecting Critical Infrastructure
Critical infrastructure sectors energy, healthcare, transportation, finance are increasingly attractive targets for attackers.
Shutting down a hospital network or pipeline operator doesn’t just cause inconvenience. It creates real-world disruption.
The strategy prioritizes stronger protections for essential services, including deeper threat intelligence sharing between government agencies and private companies.
5. Maintaining Technological Leadership
The policy also stresses maintaining U.S. leadership in emerging technologies tied to cybersecurity.
This includes:
- Artificial intelligence security systems
- Quantum computing
- Post-quantum cryptography
These technologies will shape the next generation of cyber defense and the next generation of cyber attacks, for that matter.
6. Developing Cyber Talent
There’s a talent shortage in cybersecurity. Anyone working in the field already knows this.
The strategy calls for expanded cybersecurity education programs and partnerships between government, universities, and private industry to build the workforce pipeline.
Because tools matter. But people matter more.
A More Aggressive Cybersecurity Posture
One of the most notable elements of the new strategy is its focus on offensive cyber capabilities.
For years, cybersecurity policy leaned heavily toward defense: patch systems, monitor networks, respond to breaches. Important steps, sure. But not always enough.
The 2026 strategy leans more heavily into “defend forward” operations — a concept that involves disrupting attackers before they reach U.S. networks.
That might include infiltrating criminal infrastructure, dismantling malware command servers, or disrupting ransomware operations before they launch.
In other words: taking the fight to the attackers.
This approach isn’t entirely new. U.S. Cyber Command has used similar tactics before. But the policy language here signals broader support for that posture. And here’s the part businesses should pay attention to.
A more aggressive government cyber strategy often means closer collaboration with private-sector security firms. Threat intelligence sharing, joint investigations, coordinated responses all of it. Expect those partnerships to deepen.
Global Crackdown on Cybercrime Networks
Another major focus of the executive order is dismantling international scam centers.
If you’ve followed cybercrime reporting over the past few years, you’ve probably seen the images: warehouse-sized facilities packed with scammers running fraud operations at industrial scale.
These operations have grown rapidly, particularly in regions including:
- Southeast Asia
- Eastern Europe
- Parts of Africa
Inside those centers, organized groups run sophisticated scams targeting victims around the world.
Typical operations include:
- Cryptocurrency investment scams
- Romance scams
- Technical support fraud
- Phishing campaigns
- Sextortion schemes
And the scale can be staggering.
What This Means for Businesses
The Trump Cybersecurity Executive Order 2026 will likely ripple across multiple industries.
For businesses, the biggest change isn’t necessarily a single regulation. It’s the expectation that cybersecurity readiness and fraud prevention are now part of national security infrastructure. That raises the bar.
Organizations should expect stronger pressure to collaborate with authorities, report incidents quickly, and strengthen defenses against financial cybercrime.
Impact on Critical Infrastructure
Critical infrastructure operators energy companies, hospitals, transportation systems, financial networks will likely face higher cybersecurity expectations.
That could include requirements to:
- Improve network resilience
- Adopt zero trust architectures
- Increase threat monitoring
- Strengthen supply chain security
Impact on Financial Institutions
Financial institutions sit at the center of cybercrime investigations.
Most scams eventually rely on moving stolen money through legitimate financial systems.
Banks and financial platforms may face increased expectations around:
- Monitoring suspicious financial activity
- Detecting mule accounts used in fraud schemes
- Cooperating with law enforcement investigations
- Strengthening fraud detection systems
Impact on Technology Companies
Technology companies and cybersecurity vendors will play a central role in implementing the strategy.
Demand is expected to grow for tools such as:
- AI-powered threat detection
- Behavioral analytics
- Advanced identity verification systems
- Secure cloud architectures
Importance of Post-Quantum Cryptography
Another forward-looking element of the strategy involves post-quantum cryptography.
Here’s the concern.
Quantum computers, once fully developed, could theoretically break many encryption systems used today to protect sensitive data.
That includes financial transactions, government communications, and corporate secrets.
No one knows exactly when quantum systems capable of doing this will emerge. But security planners don’t want to wait.
The strategy encourages organizations to begin preparing for quantum-resistant encryption technologies well before those systems become a real threat.
Because switching global cryptography standards overnight simply isn’t possible.
How Businesses Should Prepare
Businesses don’t need to wait for new regulations to start adapting.
Several practical steps align closely with the priorities outlined in the strategy.
- Strengthen Fraud Prevention
- Improve Incident Response Plans
- Adopt Zero Trust Security
- Establish Vulnerability Disclosure Programs
The Future of Cybersecurity Policy
The Trump Cybersecurity Executive Order 2026 reflects a broader global shift. Governments are treating cyber threats as strategic national security issues, not just technical nuisances.
Frequently Asked Questions (FAQs)
1. What is the Trump Cybersecurity Executive Order 2026?
The Trump Cybersecurity Executive Order 2026 is a federal directive designed to combat global cybercrime networks, strengthen U.S. cybersecurity defenses, and increase cooperation between government agencies and private companies to prevent cyber attacks, fraud, and ransomware operations.
2. Why was the Cybersecurity Executive Order introduced?
The order was introduced in response to the rapidly increasing cost of cybercrime, which causes billions of dollars in losses each year. It aims to disrupt international cybercriminal networks, improve digital defense systems, and strengthen the security of critical infrastructure.
3. Which cyber threats does the executive order target?
The policy focuses on several major cyber threats including ransomware attacks, phishing campaigns, online fraud, identity theft networks, sextortion schemes, and large-scale scam operations run by transnational criminal organizations.
4. How does the order impact businesses?
Businesses may face stronger expectations for cybersecurity preparedness, faster incident reporting, improved fraud detection systems, and closer collaboration with law enforcement and government cybersecurity agencies.
5. What industries are most affected by the new cybersecurity strategy?
Critical infrastructure sectors such as healthcare, energy, finance, transportation, and technology companies are expected to be most affected because they play a key role in national security and digital infrastructure protection.
6. What is post-quantum cryptography and why is it important?
Post-quantum cryptography refers to encryption methods designed to remain secure even against powerful quantum computers. Governments and organizations are preparing for this transition because future quantum systems could potentially break many current encryption standards.
7. How can businesses prepare for stronger cybersecurity regulations?
Organizations can prepare by adopting zero trust security models, improving incident response plans, implementing stronger identity verification systems, monitoring financial fraud activity, and maintaining vulnerability disclosure programs.
8. Does the executive order encourage collaboration with private cybersecurity firms?
Yes. The strategy strongly emphasizes deeper collaboration between government agencies and private cybersecurity companies to improve threat intelligence sharing, detect cyber threats earlier, and coordinate responses to major cyber incidents.
Final Thoughts
The Trump Cybersecurity Executive Order 2026 marks a notable shift in how the United States approaches cybercrime and digital security.
The strategy focuses heavily on dismantling global cybercrime networks, strengthening cooperation between government and private industry, and investing in emerging technologies that will define the next era of cybersecurity. For businesses, the takeaway is straightforward.
Cybersecurity is no longer just an IT function sitting quietly in the corner of the organization. It has become a strategic business priority one that regulators, governments, and customers are paying very close attention to.
Organizations that invest in stronger security architectures, modern fraud prevention systems, and tested incident response capabilities will be far better positioned to navigate the next wave of cyber threats.
Because the real question isn’t whether cybercriminals will keep evolving. They will.
The real question is whether organizations will adapt fast enough or learn about the next attack the same way everyone else does. Through the headlines.

