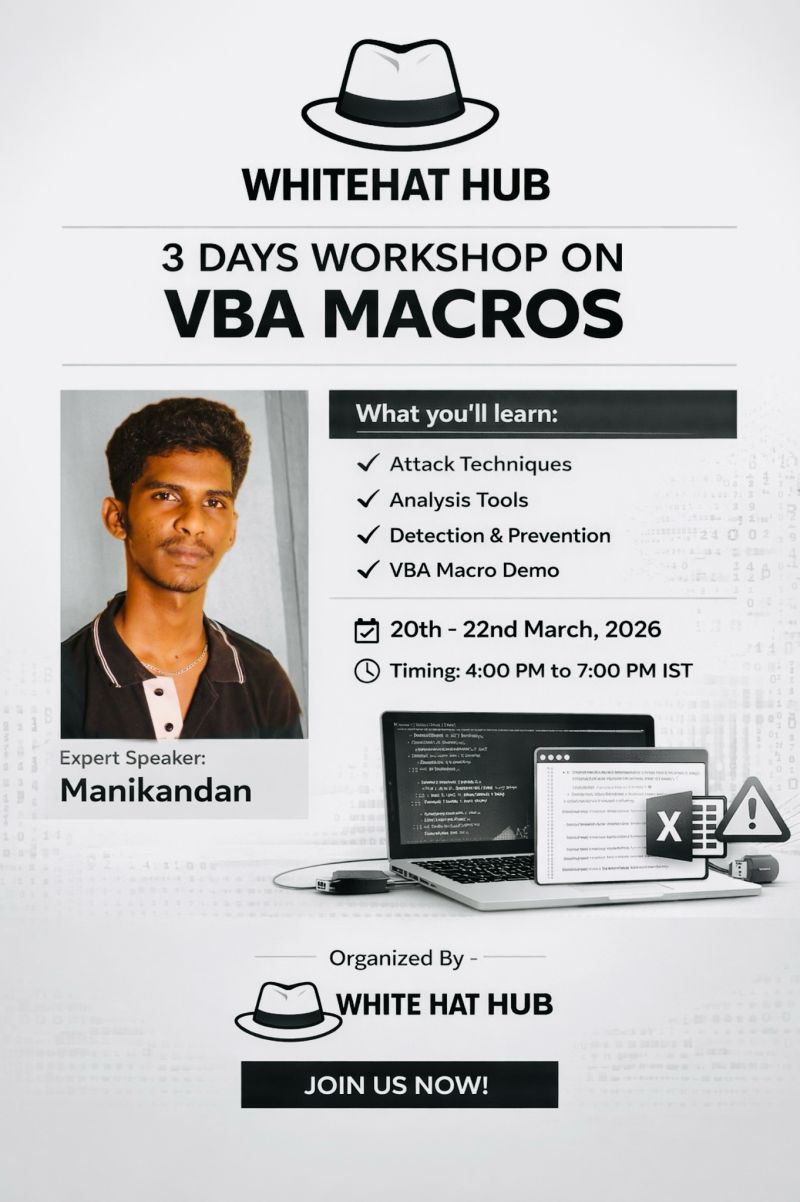
With macro-based malware continuing to dominate phishing and initial access attacks, WhiteHat Hub has announced a 3-day intensive workshop on VBA Macros security, aimed at equipping cybersecurity learners with practical, real-world skills.
The workshop will run from March 20 to March 22, 2026, between 4:00 PM and 7:00 PM IST, offering a structured learning experience focused on both offensive and defensive macro techniques.
📌 Why VBA Macros Remain a Critical Security Threat
Visual Basic for Applications (VBA) macros are widely abused by threat actors to deliver malicious payloads through seemingly legitimate documents like Excel and Word files.
Even in 2026, macro-based attacks are still a top entry vector in:
- Phishing campaigns
- Malware delivery chains
- Initial access operations
- Social engineering attacks
For SOC analysts and blue teams, understanding how VBA macros work is essential for effective detection and response.
🎯 What You Will Learn in This VBA Macros Workshop
This workshop is designed to provide hands-on exposure to macro-based threats. Key topics include:
🔹 Attack Techniques
- How attackers weaponize VBA macros
- Real-world phishing document analysis
- Payload execution methods
🔹 Analysis Tools & Techniques
- Static and dynamic analysis of macro code
- Identifying obfuscation techniques
- Extracting Indicators of Compromise (IOCs)
🔹 Detection & Prevention
- SOC-level detection strategies
- Email security and macro filtering
- Hardening endpoints against macro abuse
🔹 Live Demonstration
- Step-by-step VBA macro exploitation demo
- Real-world attack simulation
👨💻 Expert-Led Session by Manikandan
The workshop will be led by Manikandan, who will guide participants through practical cybersecurity scenarios, focusing on how macro-based threats are detected and mitigated in real-world environments.
🗓️ Workshop Details
- Event: VBA Macros Cybersecurity Workshop
- Duration: 3 Days
- Dates: March 20–22, 2026
- Time: 4:00 PM – 7:00 PM IST
- Organizer: WhiteHat Hub
- Language: Tamil
🚀 Who Should Attend?
This workshop is ideal for:
- SOC Analysts
- Cybersecurity students and beginners
- Malware analysts
- Ethical hacking enthusiasts
- Blue team professionals
🔗 Registration Link
Secure your spot here: Click here to Register
📈 Final Thoughts
As cyber threats evolve, attackers continue to rely on simple yet effective techniques like VBA macros to bypass defenses. Workshops like this play a crucial role in helping security professionals stay ahead by building hands-on detection and analysis skills.
For anyone serious about cybersecurity, this is a high-value, practical training opportunity worth attending.
This workshop announcement is based on information shared by WhiteHat Hub.