Seven confirmed breaches in seven days and not one of them started at the perimeter your team is watching.
That’s the defining pattern in this cybersecurity weekly report for March 23–29, 2026. Attackers bypassed firewalls entirely. They walked in through a compromised outsourced support vendor, a hijacked PyPI package account, and a personal Gmail belonging to the sitting director of the FBI. Your controls weren’t wrong they were aimed at the wrong door.
This week’s cyber attack news includes a tampered LiteLLM package reaching thousands of enterprise AI pipelines before anyone caught it and Medusa ransomware shutting down 35 healthcare clinics and suspending elective surgeries across Mississippi. That’s not a threat model. That’s last Tuesday.
This report delivers every confirmed incident, the five CISA KEV entries due April 3, active campaigns from APT28 and Storm-2561, and the critical vulnerabilities from March 2026 your team needs to act on before the window closes.
Major Incidents in this Cybersecurity Weekly Report
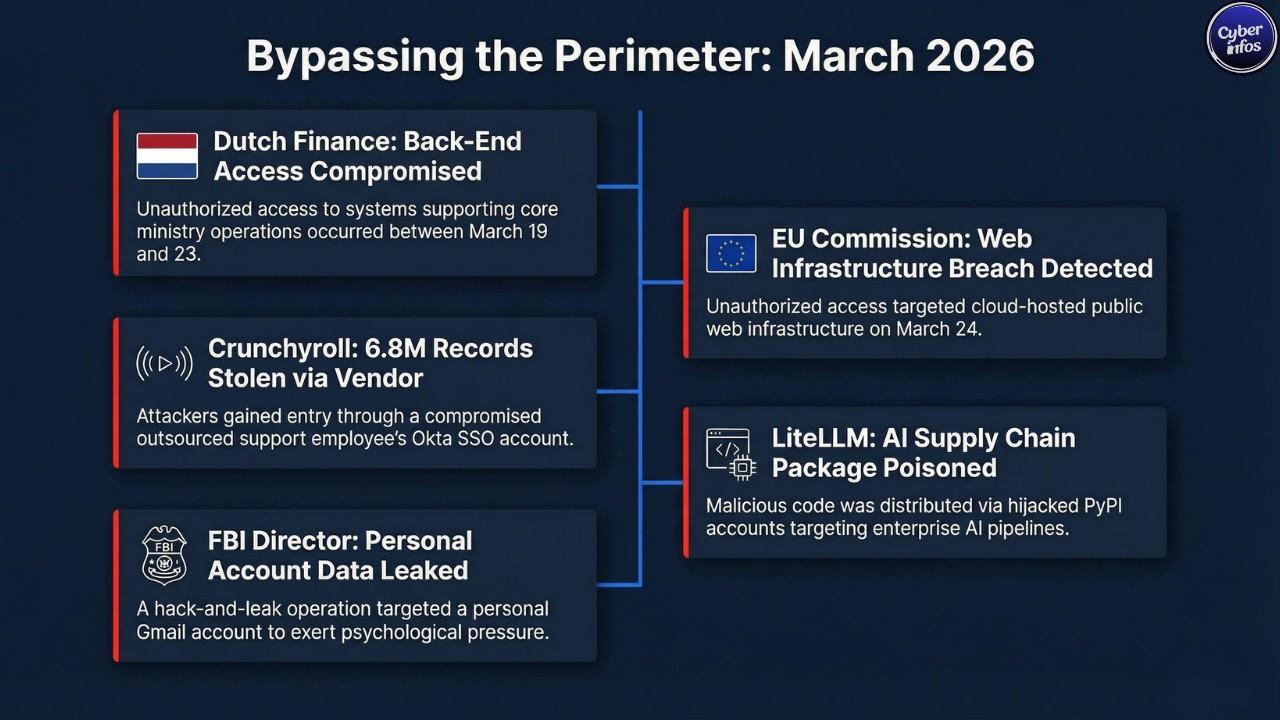
1. European Commission – Government / EU Institutional
- Organization name and industry: European Commission, executive body of the European Union
- Attack type: Unauthorized access targeting cloud-hosted public web infrastructure
- Data / Systems impacted: Potential data exposure from Europa web platform properties; internal Commission administrative systems were confirmed unaffected
- Response: The Commission detected the intrusion on March 24, notified the relevant authorities, and kicked off a forensic investigation with external support
- Business / Reputational Impact: No disruption to core EU administrative operations was reported. That said, a breach of official EU web properties carries real political weight especially right now, with EU-Russia and EU-China tensions as elevated as they are. Timing matters in incidents like this, and security communicators at the Commission will be managing the optics of this for weeks.
2. Dutch Ministry of Finance – Government / Financial Administration
- Organization name and industry: Netherlands Ministry of Finance
- Attack type: Unauthorized access to back-end ministry systems
- Data / Systems impacted: Systems supporting core ministry operations were accessed. Tax administration, customs, and public procurement services stayed fully operational throughout
- Response: Unauthorized access was first detected on March 19. Affected systems were isolated and blocked by March 23. The Hague issued a formal public statement confirming containment a notably transparent response compared to what we typically see from government entities
- Business / Reputational Impact: Operational disruption was limited. But the targeting of a national finance ministry’s back-end infrastructure is a reminder that government financial systems remain a persistent, high-value target for state-adjacent actors.
3. Crunchyroll / TELUS International – Media / Entertainment / Outsourced Services
- Organization name and industry: Crunchyroll (Japanese-owned anime streaming platform), breached through TELUS International, its outsourced support provider
- Attack type: Credential theft via a compromised Okta SSO account belonging to a TELUS International support employee
- Data / Systems impacted: Attackers claimed access to roughly 6.8 million user records and approximately 8 million support tickets. These figures come directly from the attackers and have not been independently verified treat them as unconfirmed until Crunchyroll publishes findings
- Response: Crunchyroll confirmed an active investigation with external cybersecurity specialists. Breach notifications have not yet been issued to affected users. TELUS Digital separately confirmed a cloud infrastructure breach tied to stolen credentials
- Business / Reputational Impact: This one should be a case study for every security leader who has outsourced customer support. One compromised vendor account with SSO access became the entry point to potentially millions of user records. The trust relationship between the platform and its support partner became the attack surface.
4. LiteLLM (BerriAI) – Open Source / AI Infrastructure
- Organization name and industry: LiteLLM, a widely deployed open-source Python library used in enterprise AI pipelines to route unified API calls across major LLM providers
- Attack type: Supply chain compromise via a hijacked PyPI maintainer account
- Data / Systems impacted: Malicious code was distributed under versions 1.82.7 and 1.82.8 on PyPI. These packages did not originate from the project’s official GitHub CI/CD pipeline. Users of official LiteLLM Proxy Docker images were reportedly unaffected due to hard-coded dependencies
- Response: BerriAI confirmed the incident quickly, removed the compromised packages from PyPI, rotated all maintainer credentials, paused new version releases, and engaged Google Mandiant for forensic investigation
- Business / Reputational Impact: LiteLLM sits deep inside enterprise AI development pipelines, and that is exactly why this matters so much. If your organization installed versions 1.82.7 or 1.82.8, treat the environment as compromised until proven otherwise and rotate every API key that the LiteLLM process could have touched.
5. Kash Patel (FBI Director) – U.S. Federal Government / Individual
- Organization name and industry: FBI Director Kash Patel – personal Gmail account compromised, not government systems
- Attack type: Account compromise and hack-and-leak operation
- Data / Systems impacted: Personal photographs and email excerpts were published publicly via Telegram and social media. The FBI confirmed the material was historical and contained no government or classified content
- Response: The FBI acknowledged the incident, made clear that official bureau systems were not involved, and coordinated with relevant authorities
- Business / Reputational Impact: Operationally, the damage was contained. Strategically, this was a visibility operation not an intelligence collection mission. Handala’s playbook is built around maximum public exposure and psychological pressure on high-profile targets. Compromising the personal account of a sitting FBI Director fits that playbook precisely.
New Vulnerabilities & Patches
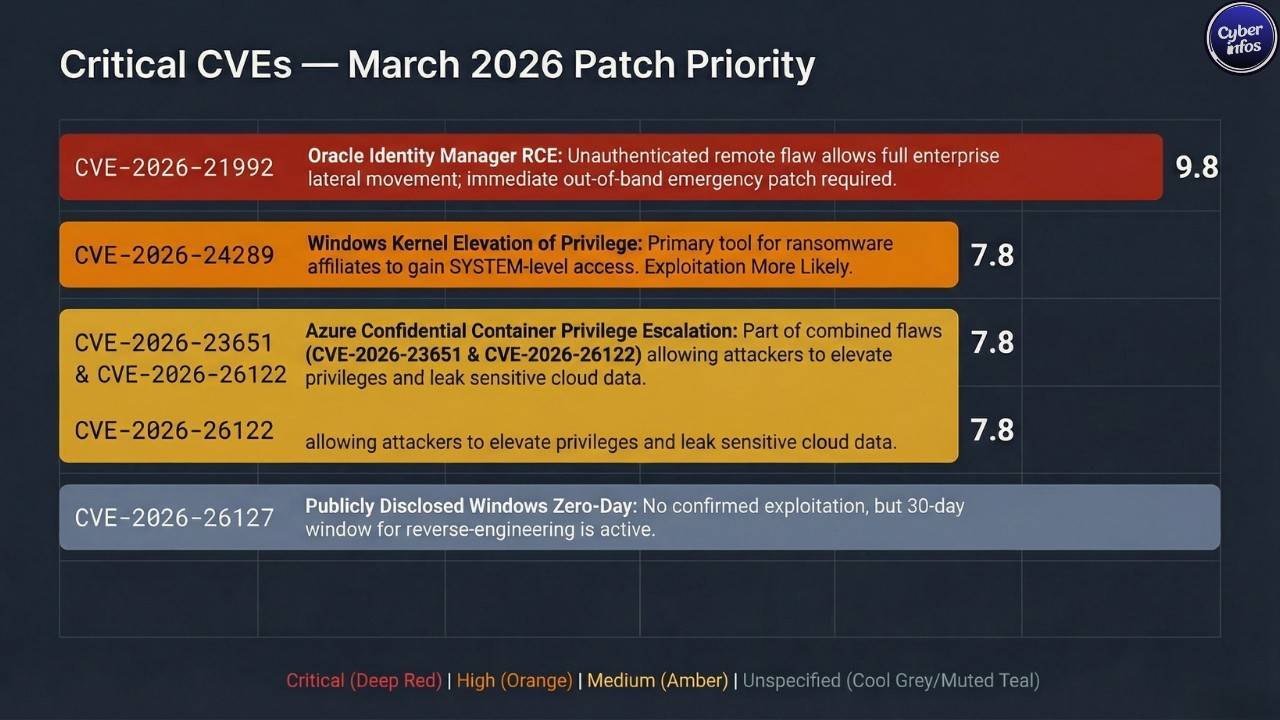
[CVE] CVE-2026-21992 | Oracle | Fusion Middleware – Identity Manager and Web Services Manager | CVSS: 9.8 | Exploited: No (as of March 22, 2026)
This one deserves your full attention. An unauthenticated remote attacker can exploit this flaw over HTTP to achieve remote code execution on Oracle Identity Manager and Oracle Web Services Manager. No authentication required. Low complexity.
Successful exploitation gives an attacker the ability to manipulate identity roles and security policies within OIM which is essentially a direct escalation path to everything else in the enterprise environment. Think lateral movement, privilege escalation, the whole chain.
[PATCH] Oracle issued a rare out-of-band emergency patch on March 19–20, outside its standard quarterly Critical Patch Update cycle. That alone tells you how serious Oracle considers this. Apply the patch to all OIM and OWSM instances immediately. There is no viable workaround; if you cannot patch right now, restrict network-level access to the OIM HTTP interface as a temporary measure and escalate the patch deployment.
[CVE] CVE-2026-23651 | Microsoft | Azure ACI Confidential Containers | CVSS: 6.7 | Exploited: No
A privilege escalation vulnerability in Microsoft Azure Confidential Containers. A local attacker with access to a confidential computing workload could use this to elevate privileges within that workload environment. Addressed in Microsoft’s March 2026 Patch Tuesday on March 10.
[PATCH] Apply the March 2026 Cumulative Update across all Azure ACI deployments. Review container privilege configurations and enforce least-privilege access models wherever confidential computing workloads are running.
[CVE] CVE-2026-26122 | Microsoft | Azure ACI Confidential Containers | CVSS: 6.5 | Exploited: No
Pairs with CVE-2026-23651 in the same environment. This is an information disclosure flaw that could expose sensitive data processed within protected confidential workloads. Both vulnerabilities were addressed in the same March Patch Tuesday bundle.
[PATCH] Deploy the March 2026 Patch Tuesday update. Prioritize environments where sensitive or regulated data is being processed inside Azure confidential computing infrastructure.
[CVE] CVE-2026-24289 | Microsoft | Windows Kernel | CVSS: 7.8 | Exploited: No – Exploitation More Likely
A Windows Kernel elevation of privilege flaw that lets a local authenticated attacker get to SYSTEM-level privileges. Microsoft flagged this as Exploitation More Likely their way of saying the technical bar to weaponization is low. In practical terms, this is exactly the kind of vulnerability ransomware affiliates reach for once they have a low-privilege foothold. It turns an initial access into a full compromise.
[PATCH] Prioritize this within your March 2026 Cumulative Update rollout, especially in environments with less-controlled endpoint access or active threat indicator detections.
[CVE] CVE-2026-26127 | Microsoft | Multiple Windows Products | CVSS: Unspecified | Exploited: No – Publicly Disclosed Zero-Day
One of two publicly disclosed zero-day vulnerabilities addressed in March Patch Tuesday. No confirmed active exploitation at release, but public disclosure is the trigger that starts the clock. Skilled threat actors can reverse-engineer patches and develop working exploits within days of a public zero-day disclosure. That window is already open.
[PATCH] Deploy March 2026 cumulative updates across all affected Windows environments immediately. Publicly disclosed zero-days remain elevated risk for at least 30 days post-disclosure, and we are in that window right now.
CISA KEV Context: CISA added five vulnerabilities to the Known Exploited Vulnerabilities catalog on March 20, 2026, with a remediation deadline of April 3, 2026 for all Federal Civilian Executive Branch agencies. The batch covered three Apple ecosystem flaws, a critical Craft CMS remote code execution vulnerability, and a Laravel Livewire code injection flaw with confirmed Iranian threat actor attribution. That last point is significant – a KEV entry with an explicit nation-state attribution attached to it is not a routine compliance checkbox.
Ransomware Activity
Medusa Ransomware – Healthcare and Municipal Government
Medusa is the dominant ransomware story of 2026, and this reporting week does nothing to change that. Operating a full ransomware-as-a-service model with a professionalized affiliate structure, the group continued to generate active incident response and regulatory activity around two of its biggest recent claims.
The University of Mississippi Medical Center, whose breach began February 19, was listed on Medusa’s dark web leak site on March 12. The group claims to have pulled more than one terabyte of patient health information and employee records and is demanding $800,000.
The breach forced the closure of 35 UMMC clinics across Mississippi, suspended elective surgeries and imaging appointments, and knocked out access to the Epic electronic health records system for nine days. Clinical staff reverted to handwritten records. Some patients were diverted to other facilities. This is what a real-world ransomware impact looks like on a healthcare system it is not a data problem, it is a patient care problem.
Medusa separately claimed an attack on Passaic County, New Jersey on March 17, demanding $800,000 and disrupting phone lines and IT systems serving approximately 600,000 residents. The group has now claimed more than 400 victims in 2026 alone. Its sustained expansion partly filling the operational vacuum left by law enforcement actions that dismantled rival RaaS operators in 2025 makes it the single most active ransomware threat to healthcare and public sector organizations right now.
Trio-Tech International – Semiconductor Services
Trio-Tech International filed an SEC disclosure on March 23 confirming that a ransomware attack hit its Singapore-based subsidiary on March 11, encrypting files within the local network. Incident response work remained ongoing at the time of filing. No ransom figure has been publicly disclosed. There is a lesson here for every CISO at a publicly traded company: an attack on a regional subsidiary still triggers parent-company disclosure obligations. The clock starts ticking whether the remediation team is ready or not.
Foster City – Municipal Government
Foster City, California confirmed a ransomware attack discovered in the early hours of March 21 that pushed officials to shut down key IT systems as an emergency containment measure. City administration, billing, and emergency communications systems were temporarily disrupted. No threat group had publicly claimed responsibility as of March 29, and no ransom figure has been disclosed.
Double extortion encrypting data while simultaneously exfiltrating it remains the standard operating procedure across every ransomware incident in this reporting week. No ransomware payments have been publicly confirmed.
Threat Intelligence
Storm-2561 – SEO Poisoning for Enterprise VPN Credential Theft
Microsoft published research on March 23 documenting an active campaign from Storm-2561, a financially motivated threat actor using search engine poisoning to harvest enterprise credentials at scale. The group is manipulating organic search results to surface spoofed download pages for legitimate enterprise VPN software.
Employees searching for VPN clients download trojanized installers that quietly deploy credential-stealing malware alongside or instead of the expected software. This campaign is particularly effective because it does not rely on phishing emails that security-aware employees might question. The delivery mechanism is organic search a channel employees trust implicitly.
[TTP] Search Engine Optimization Poisoning (ATT&CK ID: T1608.006) – Malicious download pages placed in organic search results to intercept users searching for legitimate enterprise software
[TTP] Spearphishing Link via Trojanized Installer (ATT&CK ID: T1566.002) – Credential stealers embedded within functionally convincing software installers
[IOC] Type: Domain | Value: Spoofed VPN vendor download domains surfaced via organic search manipulation | Associated Threat: Storm-2561
Handala Group – Iranian Hack-and-Leak Operation
Handala, attributed to Iran, claimed the Gmail compromise of FBI Director Kash Patel and published personal materials via Telegram during this reporting week. The FBI confirmed the breach and assessed the exposed material as non-governmental and historical. Handala does not operate like a traditional espionage group.
Their goal is not quiet intelligence collection it is loud, public pressure. Compromising the personal account of the sitting head of the FBI and broadcasting the contents across social media is a message, not a mission. Defenders protecting senior executive personal accounts need to understand that the boundary between personal and professional digital identity no longer exists as a meaningful security concept.
[TTP] Valid Accounts – Compromise of Personal/Consumer Accounts (ATT&CK ID: T1078.004)
APT28 – Continued European Espionage Campaign
APT28 (Fancy Bear, UAC-0001), the Russian GRU-linked advanced persistent threat group, continued its documented 2026 espionage campaign targeting European military, government, maritime, and transportation organizations. The campaign employs weaponized Microsoft Office documents, multi-stage loaders, and cloud-based command-and-control channels designed to blend into legitimate cloud traffic.
No new APT28 intrusions were specifically confirmed during the March 23–29 window, but the campaign remains active. European defense-sector and diplomatic organizations should treat this threat as ongoing, not resolved.
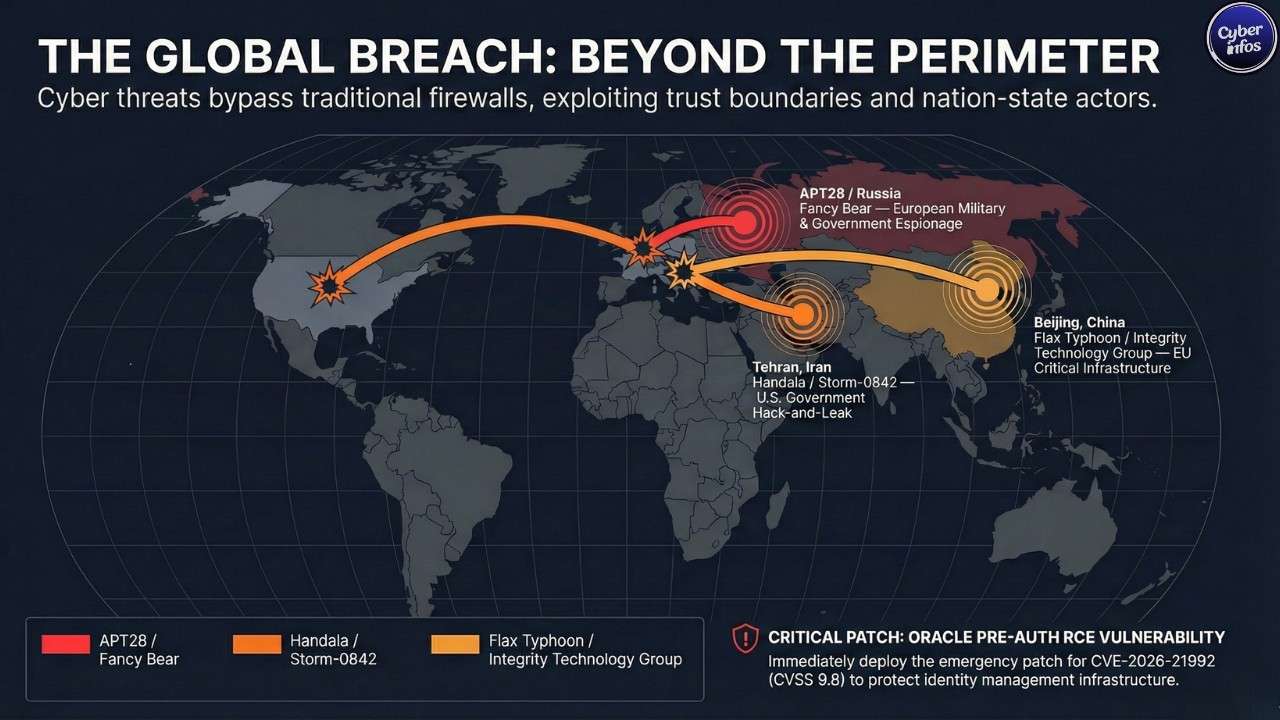
[TTP] Spearphishing Attachment — Office Document Exploit (ATT&CK ID: T1566.001)
[TTP] Command and Control via Cloud Services (ATT&CK ID: T1102.002)
[IOC] Type: File | Value: Malicious Office documents delivered via spearphishing to European defense and transport organizations | Associated Threat: APT28 / Fancy Bear
Industry News
EU Cyber Sanctions – Chinese and Iranian Entities (March 16, 2026)
The most consequential regulatory action of the reporting period came just before this week opened. On March 16, the Council of the European Union sanctioned three entities and two individuals for their roles in cyberattacks against EU member states and critical infrastructure.
The sanctioned parties are Integrity Technology Group (China), Anxun Information Technology (China), and Emennet Pasargad (Iran), alongside two co-founders of Integrity Technology Group Chen Cheng and Wu Haibo. Integrity Technology Group was specifically linked to the Flax Typhoon APT operation, which compromised more than 65,000 devices across six EU member states between 2022 and 2023.
What makes this significant is not just the sanctions themselves it is the approach. The EU is now doing what the U.S. has done for years: publicly attributing attacks to specific named private companies that form the operational backbone of state-sponsored cyber operations, and sanctioning them directly. That is a meaningfully different posture from blanket government-to-government statements, and it signals a maturing EU response framework.
Oracle Out-of-Band Emergency Patch – CVE-2026-21992 (March 20, 2026)
Oracle issues out-of-band emergency patches rarely their quarterly Critical Patch Update cycle is the standard cadence. When Oracle breaks that cycle for a pre-authentication remote code execution flaw in identity management infrastructure, the message is clear: do not wait.
Security vendors including Sophos and Arctic Wolf both published rapid response advisories within 48 hours of Oracle’s announcement, a coordination speed that reflects how seriously the vulnerability research community assessed the risk to enterprise environments.
CISA KEV Catalog – Five New Additions with April 3 Deadline (March 20, 2026)
CISA added five new entries to the Known Exploited Vulnerabilities catalog on March 20, all carrying an April 3, 2026 remediation deadline for Federal Civilian Executive Branch agencies. The Laravel Livewire code injection entry carried explicit Iranian threat actor attribution connecting it directly to active nation-state campaigns documented elsewhere in this cybersecurity weekly report.
Beyond federal agencies, cyber insurance carriers are increasingly auditing KEV patch compliance as a coverage condition. These additions carry commercial risk implications that reach well past the federal sector.
Europol Dark Web Enforcement
Europol confirmed this week that coordinated law enforcement operations have resulted in the shutdown of 373,000 dark web sites. U.S. authorities handed down sentences for facilitators connected to North Korean remote-worker infiltration schemes and a cross-border business email compromise operation.
Enforcement momentum across multiple jurisdictions is building but so is the adaptability of threat actors who simply reconstitute under new infrastructure after each takedown.
Tool Updates
LiteLLM – Supply Chain Incident and Recovery Status
LiteLLM is the most significant tool story in this cybersecurity weekly report, and for the wrong reasons. The widely used open-source Python library which provides a unified API layer across major LLM providers including OpenAI, Anthropic, Azure, and Google was at the center of a supply chain attack when malicious packages were uploaded to PyPI as versions 1.82.7 and 1.82.8 through a compromised maintainer account rather than the project’s official GitHub CI/CD pipeline.
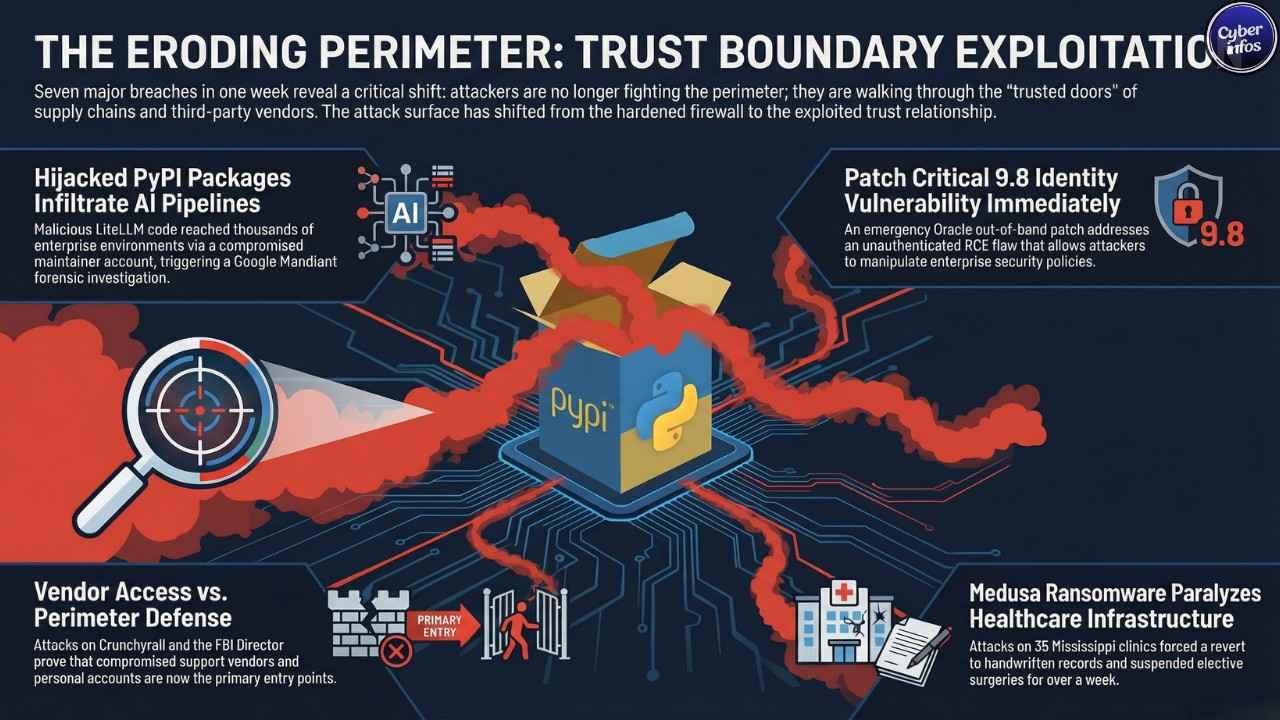
BerriAI moved quickly: malicious packages were removed from PyPI, all maintainer credentials were rotated, new version releases were paused, and Google Mandiant was engaged for forensic analysis. Users of the official LiteLLM Proxy Docker image were reportedly unaffected due to hard-coded dependencies that bypassed the compromised PyPI packages.
If your organization installs LiteLLM from PyPI and cannot confirm it avoided the affected versions isolate the environment now, rotate all API keys and credentials the LiteLLM process had access to, and audit LLM API call logs for anything unusual. The investigation is still open. Wait for a clean bill of health from BerriAI before restoring normal operations.
Microsoft March 2026 Cumulative Updates – Active Deployment Window
Microsoft’s March 2026 Patch Tuesday package addressing 83 CVEs across the Windows Kernel, Windows Hyper-V, Microsoft SQL Server, Windows Kerberos, the Windows Graphics Component, Windows App Installer, and Azure ACI Confidential Containers remains in active enterprise deployment this week.
Teams that have not yet completed rollout should prioritize the two publicly disclosed zero-days (CVE-2026-21262 and CVE-2026-26127) and the Exploitation More Likely Windows Kernel EoP vulnerability (CVE-2026-24289) before anything else.
Looking Ahead
Three developing situations deserve close attention as we move into the week of March 30 through April 5, 2026.
The LiteLLM supply chain investigation is still wide open. Google Mandiant’s engagement means BerriAI does not yet have a full picture of what the malicious packages were actually designed to do.
Additional findings confirming or ruling out credential exfiltration, backdoor implants, or tampering with other packages from the same compromised PyPI account are expected to emerge in the coming days. Treat this as an escalating, unresolved incident, not a closed one.
The April 3 CISA KEV remediation deadline is arriving fast. If your organization has not patched the five entries added on March 20 including the Craft CMS RCE and the Iranian-attributed Laravel Livewire code injection you are days away from federal non-compliance and active exploitation risk at the same time. Escalate patch validation to leadership before Monday morning.
The Crunchyroll breach investigation has an unconfirmed claim of 6.8 million affected users sitting unresolved. If that figure is validated, GDPR notification obligations, applicable U.S. state privacy law requirements, and the inevitable class action exposure will all accelerate simultaneously.
Watch for Crunchyroll to publish findings early next week. The regulatory and litigation calendar for this one is only just beginning.
Upcoming events: Microsoft’s next Patch Tuesday is April 14, 2026. BSides London 2026 and the SANS Cyber Threat Intelligence Summit are both scheduled for early April. Oracle’s quarterly Critical Patch Update for April is expected mid-month and given CVE-2026-21992, there is heightened interest in what additional Fusion Middleware disclosures that cycle may contain.
By the Numbers
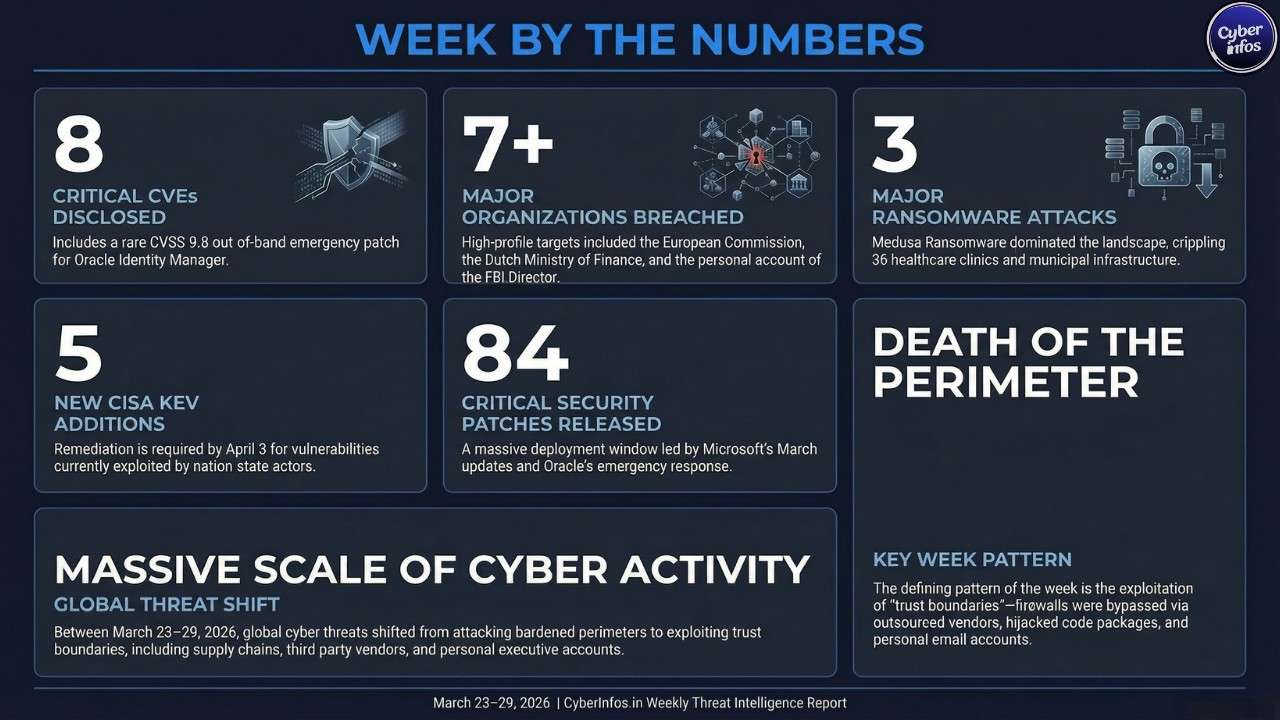
| STAT | VALUE | CONTEXT |
|---|---|---|
| Critical CVEs Disclosed | 8 | Microsoft March Patch Tuesday (8 Critical-rated CVEs across Azure ACI, Windows Kernel, Hyper-V); Oracle separately patched CVSS 9.8 CVE-2026-21992 out-of-band |
| Organizations Breached | 7+ | European Commission, Dutch Finance Ministry, Crunchyroll via TELUS, LiteLLM supply chain, Kash Patel personal account, Trio-Tech Singapore, Foster City CA |
| Ransomware Attacks Reported | 3 | Trio-Tech International (disclosed March 23), Foster City CA (discovered March 21), Medusa UMMC and Passaic County investigations ongoing 400+ Medusa victims in 2026 |
| New Malware Variants | 2 | Malicious LiteLLM PyPI packages versions 1.82.7 and 1.82.8 confirmed as supply chain threat via compromised maintainer account |
| CISA KEV Additions | 5 | Added March 20 Apple ecosystem (3 flaws), Craft CMS RCE, Laravel Livewire code injection with Iranian threat actor attribution; April 3 deadline |
| Patches Released | 84 | Microsoft (83 CVEs via March 10 Patch Tuesday) plus Oracle out-of-band emergency patch for CVE-2026-21992 on March 20 |
| EU Cyber Sanctions Imposed | 5 | Three entities and two individuals sanctioned March 16 in connection with Flax Typhoon and Iranian cyber operations against EU member states |
Final Thoughts
This week didn’t produce one defining breach. It produced seven — and every single one exploited a relationship your organization trusts rather than a system it guards.
That’s the shift that matters most in March 2026. The perimeter is no longer where attacks begin. They begin in your support vendor’s SSO portal, your developer’s PyPI dependency list, your executive’s personal inbox. The attack surface has moved, and for many organizations, the security model hasn’t followed it yet.
Three actions cannot wait past this week. Patch Oracle CVE-2026-21992 immediately a CVSS 9.8 unauthenticated RCE in identity management infrastructure has no grace period. Verify your five CISA KEV entries are remediated before the April 3 deadline. And if your organization runs LiteLLM in any AI pipeline, treat the environment as unresolved until Google Mandiant closes its investigation and BerriAI issues a clean confirmation.
The Crunchyroll investigation, the LiteLLM forensics, and the Foster City ransomware attribution are all still open. Next week’s cybersecurity weekly report will carry the follow-up on each.
The attackers are already moving. The only question is whether your response is moving faster.
Stay ahead of every threat.
Follow CyberInfos.in for weekly threat intelligence, CVE analysis, and incident reporting published every Monday morning.


 Disclaimer: This report is compiled from publicly available threat intelligence sources for educational and awareness purposes. IOCs and CVE details should be independently verified against CISA KEV, NVD, and vendor advisories before operational use.
Disclaimer: This report is compiled from publicly available threat intelligence sources for educational and awareness purposes. IOCs and CVE details should be independently verified against CISA KEV, NVD, and vendor advisories before operational use.