Picture this: An attacker got into your network in January. It is now July. They have read executive emails, mapped your Active Directory, harvested credentials from three privileged accounts, staged a 40GB exfiltration package on a cloud drive, and are two steps away from deploying ransomware. Your SOC dashboard is clean. No critical alerts. No anomalies flagged.This is not a red team scenario. It is the Data Breach Detection time 2026
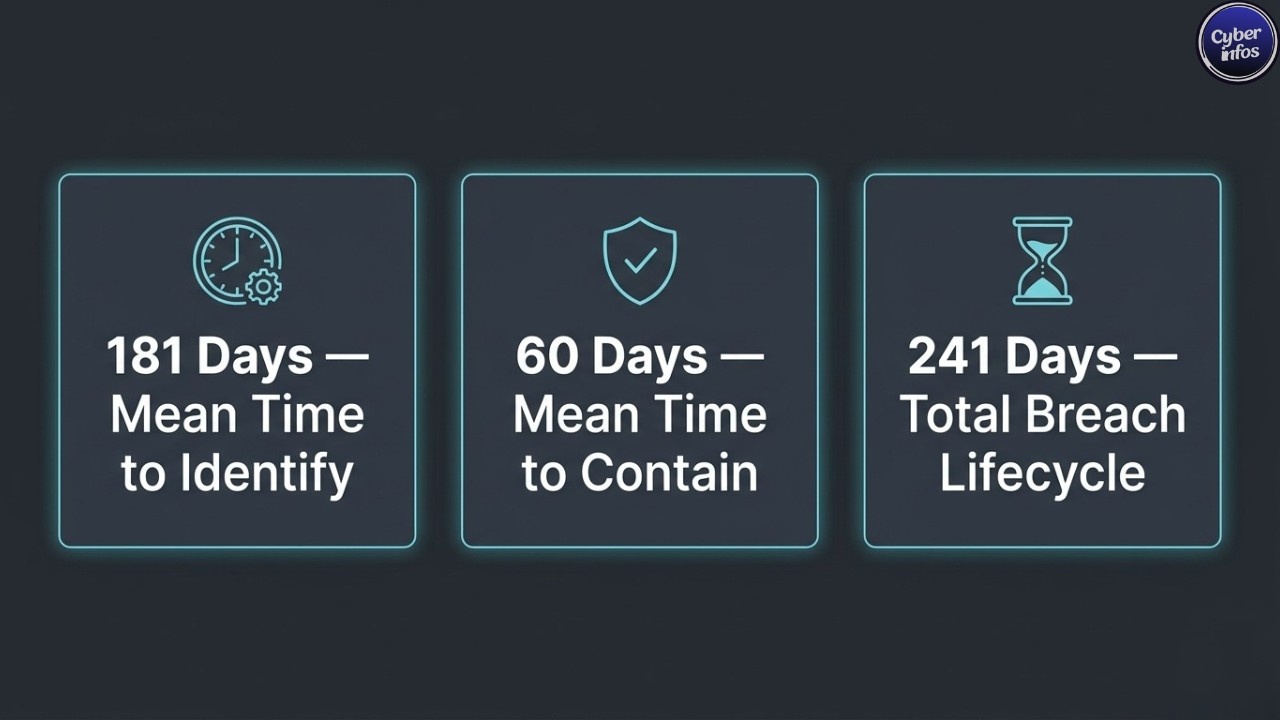
The single most important question in enterprise security right now is not whether you will be breached it is how long a breach will go undetected before your team finds it. According to the IBM Cost of a Data Breach Report 2025, the mean time to identify a breach is 181 days, with an additional 60 days to contain it. That puts the total breach lifecycle at 241 days roughly eight months from initial intrusion to full eviction.
This guide breaks down the latest breach discovery statistics for 2026, explains why attackers stay hidden for so long, and gives security teams a prioritised action plan to reduce dwell time with numbers to back every recommendation.
Average Dwell Time Data Breach: What the Numbers Actually Mean
Before getting into the statistics, two terms need to be separated. Most breach reports use them interchangeably, but they measure different problems.
Mean Time to Identify a Breach (MTTI) also called dwell time is the number of days an attacker remains inside your environment before anyone notices. This is the dangerous window. While the average dwell time data breach clock runs, attackers move laterally, escalate privileges, harvest credentials, and prepare for the main event. A sophisticated threat actor spends most of this period doing slow, deliberate reconnaissance learning the environment well enough to cause maximum damage when they act.
Mean Time to Contain (MTTC) is the time from discovery to full eviction. The breach is known but the attacker is not yet out. Incident responders are working to scope the compromise, revoke access, and close entry points. Containment is often harder than detection because by the time a breach is confirmed, the attacker has typically established multiple persistence mechanisms across several systems.
Total breach lifecycle = MTTI + MTTC. In 2025, that combined figure was 241 days more than eight months from the moment an attacker got in to the moment they were fully expelled. Understanding this distinction is essential for breach detection and containment planning: detecting fast is only half the problem. Containing fast is the other half.
Breach Discovery Statistics 2026: The Critical Benchmarks
Here are the numbers security teams need to know heading into 2026, drawn from IBM, Verizon, and Mandiant research.
| Metric | 2024 | 2025 | Change |
|---|---|---|---|
| Mean Time to Identify (MTTI) | 194 days | 181 days | ↓ 13 days |
| Mean Time to Contain (MTTC) | 64 days | 60 days | ↓ 4 days |
| Total breach lifecycle | 258 days | 241 days | ↓ 17 days |
| Lifecycle with XDR deployed | ~270 days | 249 days | ↓ improvement |
| Lifecycle without XDR | ~310 days | 304 days | Marginal change |
| Credential breach lifecycle | 328 days | 292 days | ↓ 36 days |
| Median dwell time (Mandiant) | ~10 days | ~10 days | Stable |
Sources: IBM Cost of a Data Breach 2025, Verizon DBIR 2025, Mandiant M-Trends 2025
The 10-Year Trend: How Breach Detection Time Has Changed
The data breach detection time has been declining since 2016, but the pace of improvement is uneven.
| Year | Avg. Lifecycle (Days) |
|---|---|
| 2016 | 314 |
| 2018 | 297 |
| 2020 | 280 |
| 2021 | 287 |
| 2022 | 277 |
| 2023 | 277 |
| 2024 | 258 |
| 2025 | 241 |
The 2021 spike is not a blip. It tracks directly with the post-COVID shift to hybrid environments, which created visibility gaps that attackers immediately exploited. The acceleration from 2022 onward correlates with broader XDR adoption and early AI-powered behavioural analytics deployment in security operations.

The 108-day reduction attributable to AI and automation is the single biggest improvement driver in the dataset. Organisations with high AI deployment in their security operations cut the total breach lifecycle by more than three months compared to those with no AI and contained breaches 80 days faster.
The problem is that adoption is not uniform. Many organisations, particularly mid-market and those in OT-heavy environments, are still running SIEM configurations from five years ago, with rule sets last updated during a compliance audit. For them, the trend line looks nothing like the IBM average. How long a breach stays undetected in those environments can far exceed 241 days.
Breach Detection Time by Attack Vector: Where Attackers Hide Best
The most practically useful cut of detection time data is by attack vector. Different entry methods have very different detection profiles, and this shapes where investment should go.
| Attack Vector | Time to Identify | Time to Contain | Total Lifecycle |
|---|---|---|---|
| Supply chain / third-party | ~194 days | ~73 days | ~267 days |
| Malicious insider | ~200 days | ~60 days | ~260 days |
| Stolen / compromised credentials | ~186 days | ~60 days | ~246 days |
| Phishing | ~175 days | ~65 days | ~240 days |
| Human error / accidental exposure | ~153 days | ~60 days | ~213 days |
Supply chain attacks take the longest to detect because attackers enter through trusted software or vendor channels bypassing perimeter controls entirely. From the moment the compromised component is active in the environment, it looks like a legitimate update or a normal vendor connection. There is no alert because there is no perimeter anomaly. Detection requires monitoring behaviour after trust is established, which is exactly where most organisations have the weakest coverage.
Credential-based attacks come close behind. A threat actor with valid credentials is, to a SIEM, a legitimate user. They authenticate at normal times, access expected systems, and perform actions that individually look unremarkable. The only way to catch them is behavioural impossible travel, unusual access volumes, off-hours database queries, lateral movement between accounts that do not normally interact. Rule-based systems catch almost none of this.
The 292-day average lifecycle for credential-based breaches is the number that matters most here. Nearly ten months from compromise to containment. MFA, PAM, and identity threat detection are directly tied to how long attackers retain access after stealing credentials and the breach detection and containment gap for credential attacks is the widest of any vector in the dataset.
Breach Detection Time by Industry: The Sectors Falling Behind
The gap between the fastest and slowest industries is wider than most organisations expect. Healthcare and manufacturing are not slightly behind financial services they are operating in a fundamentally different detection environment.
| Industry | Est. Detection Time | Primary Driver |
|---|---|---|
| Healthcare | 279 days | Legacy systems, fragmented IT, HIPAA complexity |
| Manufacturing | 265 days | OT/ICS with limited network visibility |
| Energy / Utilities | 258 days | Critical infrastructure, sparse monitoring |
| Education | 245 days | Underfunded security teams, open networks |
| Retail | 230 days | High attack surface, seasonal staff turnover |
| Financial Services | 218 days | Regulatory pressure, higher security investment |
| Technology | 204 days | In-house expertise, faster tooling deployment |
Sources: IBM Cost of a Data Breach 2025, SQ Magazine
Healthcare’s 279-day average is not just a statistic it represents a sector being deliberately targeted because attackers know detection will be slow. Electronic health records sell for more than credit card data on dark web markets, and the average hospital network combines legacy clinical systems, modern cloud applications, connected medical devices, and third-party vendor access into a monitoring nightmare.
Manufacturing’s problem is primarily OT/ICS visibility. Industrial control systems often run protocols that do not integrate with standard SIEM platforms, creating detection blind spots that ransomware groups exploit deliberately. Financial services performs better largely because regulators forced the investment and that lesson transfers directly to every other sector.
Q1 2026 recorded 486 breach events across transportation, retail, insurance, and education. The US logged 3,322 data breaches in 2025 a 4% year-over-year increase. Breach volume is not declining. The only variable your security team controls is how long attackers spend in your environment before you find them.
Regional Detection Gaps: Where India Stands in 2026
Detection speed varies significantly by geography, driven by differences in regulatory maturity, threat intelligence sharing, and security tooling adoption.
| Region | Avg. Detection Time (Approx.) |
|---|---|
| United States | 180–200 days |
| United Kingdom | 185–210 days |
| European Union | 190–215 days |
| Middle East | 210–240 days |
| India / South Asia | 220–255 days |
| APAC (Broader) | 205–235 days |
| Latin America | 230–260 days |
Sources: IBM Regional Data 2025, DeepStrike Regional Breakdown
India’s data breach detection time runs 20 to 30 days above the global average. The gap comes from limited XDR and MDR adoption in SMEs, lower penetration of advanced detection tooling outside large enterprises, and a smaller pool of certified incident responders relative to the attack surface being defended.
This matters now more than before. India’s Digital Personal Data Protection (DPDP) Act places breach notification requirements on organisations requirements that assume detection has already happened within a reasonable window. An organisation sitting at 240-plus days of average dwell time is functionally unable to meet those obligations, not because of compliance failure, but because the breach was never found in time to report. Reducing mean time to identify breaches is no longer just a security objective for Indian organisations it is becoming a compliance requirement.
How Breaches Are Actually Discovered in 2025–2026
The method of discovery matters as much as the timing. It directly determines how much damage has accumulated and what the financial outcome will be.
Internal security teams identify approximately 50% of breaches. Speed depends entirely on whether the organisation has a functioning SIEM, XDR, or MDR solution with active monitoring and tuned alert rules. This 50% figure is the one to benchmark against if your team is not finding most of its own breaches, the detection process has a structural gap.
External parties law enforcement, journalists, customers, and breach notification services account for roughly 41% of all breach discoveries in 2025. Nearly half of all breaches are found by someone outside the victimised organisation. When external disclosure happens, costs rise sharply: regulatory penalties compound, and the organisation failed publicly to detect its own breach. The 41% figure in breach discovery statistics 2026 is one of the most consistently alarming numbers in the dataset.
Ransomware notifications are attacker-disclosed. The ransom note is the breach notification. By the time it appears, encryption is complete, exfiltration is complete, and the attacker’s objectives are finished. Detection at this point is damage assessment, not detection.
AI-augmented detection is where the positive story is. Organisations with fully deployed AI security tools cut the breach lifecycle by 108 days finding breaches weeks faster than the unassisted average. Behavioural anomaly detection is finding what rule-based systems miss by design, and the gap between AI-assisted and unassisted detection speed is widening each year.
Why Breaches Stay Undetected for Months
Understanding why detection fails is a prerequisite for fixing it. There are five root causes that account for most of the 181-day average.
Attackers blend into normal traffic. Once inside with valid credentials, sophisticated threat actors operate during business hours, access expected systems, and avoid triggering known signatures. They are not running exploit kits — they are reading email, copying files, and mapping network shares. Rule-based SIEM cannot distinguish a legitimate user from a threat actor using stolen credentials without strong behavioural baselines.
Alert fatigue defeats analyst capacity. SOC teams receive thousands of alerts daily, the majority of which are false positives. Research shows analysts investigate fewer than 50% of security alerts in a given workday. The real indicators of compromise are in that uninvestigated queue. Reducing average dwell time data breach metrics starts with giving analysts alerts worth investigating.
Lateral movement is deliberately slow. Professional threat actors move through networks over weeks, deliberately staying below detection thresholds. One new connection per day. One new account enumerated per week. This slow-and-low approach extends dwell time far beyond what most detection rules are configured to catch.
Hybrid and cloud environments create visibility gaps. With workloads spread across on-premises infrastructure, cloud platforms, and SaaS applications, many organisations have monitoring that stops at the perimeter. Public cloud misconfigurations exposed 88 million records in Q1 2025 alone many of those exposure windows were open for extended periods with no alert generated.
Third-party access is outside the monitoring perimeter. When an attacker enters through compromised vendor software or a legitimate vendor account, the initial access point is typically not monitored at all. The supply chain is not a solved problem the SolarWinds and MOVEit patterns have been repeated in modified forms across dozens of incidents since. Third-party risk is a detection gap most organisations have not closed.
SIEM vs. XDR vs. MDR: Which Detects Breaches Fastest?
Security teams evaluating detection tooling need a clear, honest comparison of what each approach delivers.
| Detection Tool | Avg. Detection Speed | Key Advantage | Best Fit |
|---|---|---|---|
| Traditional SIEM | Weeks to months | Log aggregation, compliance reporting | Enterprises with large in-house SOC |
| EDR (Endpoint Detection) | Hours to days | Deep endpoint visibility | Orgs with strong endpoint coverage |
| XDR (Extended Detection) | Hours to days | Cross-layer correlation across endpoint, network, cloud | Mid-to-large enterprises |
| MDR (Managed Detection) | Minutes to hours | 24/7 expert monitoring without in-house SOC | SMBs and orgs scaling security operations |
| AI-native platforms | Minutes | Continuous behavioural baseline, anomaly detection | Orgs targeting fastest possible MTTI |
| Manual / No tooling | Months to never | — | Organisations at highest breach risk |
The XDR number tells the clearest story: organisations using XDR ran a 249-day breach lifecycle versus 304 days without it a 55-day improvement from one tooling decision. The breach detection and containment improvement from XDR comes from cross-layer correlation: catching attacker behaviour that spans endpoint, network, and cloud simultaneously, rather than investigating each in isolation.
The MDR case is starker. Best-performing MDR providers have demonstrated detection times under 35 minutes. Compared to IBM’s 181-day average mean time to identify a breach, that gap represents an entirely different threat posture. For organisations without an in-house SOC which describes most organisations under 2,000 employees MDR is the fastest practical route to competitive detection speed.
The honest assessment of traditional SIEM without behavioural analytics: it is a compliance tool that was never designed to catch sophisticated attackers using legitimate credentials and slow lateral movement. It catches known-bad signatures. Modern attackers do not look like known-bad signatures.
How to Reduce Breach Detection Time: A Prioritised Framework

These steps are sequenced by impact-to-effort ratio. Each maps to a measurable reduction in dwell time based on the data above.
1. Integrate Threat Intelligence Into Your Detection Stack
Organisations using threat intelligence identify threats 28 days faster on average than those relying solely on internal telemetry. If you know what indicators of compromise are active in the current threat landscape, your detection rules can look for them specifically rather than waiting to discover them through behavioural drift. Integrate feeds from VirusTotal, AlienVault OTX, or commercial sources into your SIEM or XDR. At maturity, automate ingestion and matching in real time.
2. Move From Rule-Based to Behavioural Detection
If your SIEM is still running primarily signature-based rules without UEBA or AI-driven behavioural analytics, this is your highest-return upgrade. The average dwell time data breach for organisations using AI-heavy detection drops by 108 days. The use case is catching credential abuse, insider threats, and living-off-the-land techniques that do not match any known signature. Plan for a 4–6 week baselining period before alerts become reliably actionable.
3. Enforce Least Privilege and Deploy PAM
Credential breaches take 292 days to resolve. The breach detection and containment window for credential attacks is long because valid credentials look legitimate by definition. Implement Privileged Access Management for all administrator and service accounts. Set specific alerts for impossible travel, off-hours privileged access, mass data access events, and account enumeration the behavioural signatures of credential abuse that default SIEM configurations rarely include.
4. Run Proactive Threat Hunts
Proactive threat hunting consistently surfaces attackers who have already evaded automated detection. Waiting for alerts means waiting for the attacker to trigger a known signature. Experienced attackers do not. Hunt specifically for unusual scheduled tasks, lateral movement through pass-the-hash or pass-the-ticket, WMI and PowerShell abuse, connections to newly registered domains, and accounts accessing data outside their normal scope. Even quarterly hunts significantly reduce how long a breach goes undetected.
5. Build and Test Incident Response Playbooks
Faster detection is wasted if containment is improvised. Organisations with tested IR playbooks contain breaches significantly faster than those who figure out the process during an active incident. Build playbooks for ransomware, credential compromise, cloud misconfiguration exposure, and supply chain incident. Run tabletop exercises at least twice per year. The first real incident is not the time to discover who has authority to isolate a domain controller.
6. Continuously Audit and Monitor Third-Party Access
Supply chain attacks produce the longest breach lifecycles because the entry point is outside your environment. Map every third party with network or system access. Enforce MFA on all vendor accounts without exception. Monitor third-party user behaviour through your SIEM with the same alerting profile applied to internal privileged accounts. Review access grants quarterly and revoke anything no longer operationally required.
7. Aggressively Tune Alert Rules to Cut False Positives
An analyst reviewing 5,000 alerts per day investigates fewer than half. Every false positive that reaches the queue consumes capacity that should go toward real incidents. Work with your SIEM or XDR vendor to achieve a false positive rate below 5% for high-priority alerts. Suppress noisy, low-value rules. Build context into alerts so analysts triage faster. The goal is not fewer alerts it is a higher percentage of alerts worth investigating.
Frequently Asked Questions
1. What is the average data breach detection time 2026?
According to IBM’s Cost of a Data Breach Report 2025, the mean time to identify a breach is 181 days. Including containment, the full breach lifecycle averages 241 days a nine-year low, though still nearly eight months from intrusion to resolution.
2. How long does a breach go undetected on average?
The IBM average is 181 days. Mandiant’s 2025 median for targeted intrusions is approximately 10 days faster-moving attackers are compressing timelines. For organisations without modern detection tooling, how long a breach stays undetected can exceed 300 days.
3. Which industries have the worst breach detection times?
Healthcare (279 days), manufacturing (265 days), and energy/utilities (258 days) consistently rank slowest. The drivers are legacy infrastructure, OT/ICS visibility gaps, and limited security investment.
4. How do breach discovery statistics compare between AI and non-AI organisations?
Organisations with fully deployed AI and automation reduce the breach lifecycle by 108 days and contain breaches 80 days faster. The breach discovery statistics 2026 are clear: AI deployment is the single biggest lever for cutting dwell time.
5. What percentage of breaches are found by external parties?
Approximately 41% are discovered by external parties law enforcement, journalists, or third parties rather than the victimised organisation’s own security team.
6. What is the best tool for breach detection and containment?
MDR providers offer the fastest detection times in practice under 35 minutes for best-in-class deployments. XDR provides strong cross-layer correlation and cuts the breach lifecycle by 55 days versus no XDR. For breach detection and containment, the combination of XDR with 24/7 MDR coverage is the highest-performing deployment model for organisations without a mature in-house SOC.
Key Takeaways
The 241-day average breach lifecycle is the best on record. It is also eight months of attacker access at the mean and considerably worse for organisations in healthcare, manufacturing, or those still running manual detection.
The organisations closing that gap share three traits. They have deployed AI-augmented detection and UEBA not just rule-based SIEM. They run proactive threat hunts instead of waiting for alerts. And they treat third-party access as part of their own attack surface, with the same monitoring coverage applied to vendor accounts as to internal privileged users.
Data breach detection time 2026 is not fixed. It is a direct output of investment decisions. The breach discovery statistics tell you exactly which decisions move the needle most and by how many days. The window of undetected attacker access is yours to close.
Sources: IBM Cost of a Data Breach Report 2025 | Verizon DBIR 2025 | Mandiant M-Trends 2025 | BitSight Q1 2026 Breach Report | DeepStrike Regional Breach Analysis 2025 | Statista Breach Lifecycle Data

