
Major Incidents – Cybersecurity Weekly Report
Drift Protocol: Governance Takeover and $285M DeFi Theft
Solana-based derivatives exchange Drift Protocol is still dealing with the fallout from an exploit that drained an estimated $280–$285 million from its vaults in one of 2026’s largest DeFi hacks to date. Investigations show the attackers didn’t exploit a traditional smart-contract bug but instead abused governance-layer weaknesses and pre-signed durable nonce transactions to seize Security Council privileges, then rapidly move funds out of protocol control.
The attack took minutes to execute but followed roughly six months of careful social engineering, conference networking, and “partner” outreach attributed with medium-to-high confidence to North Korean cluster UNC4736 (AppleJeus/Citrine Sleet). Drift has paused key functions, is working with law enforcement, and has seen its token price and TVL sharply reduced while options for fund recovery and potential remediation are explored.
European Commission Cloud Breach via Trivy Supply Chain
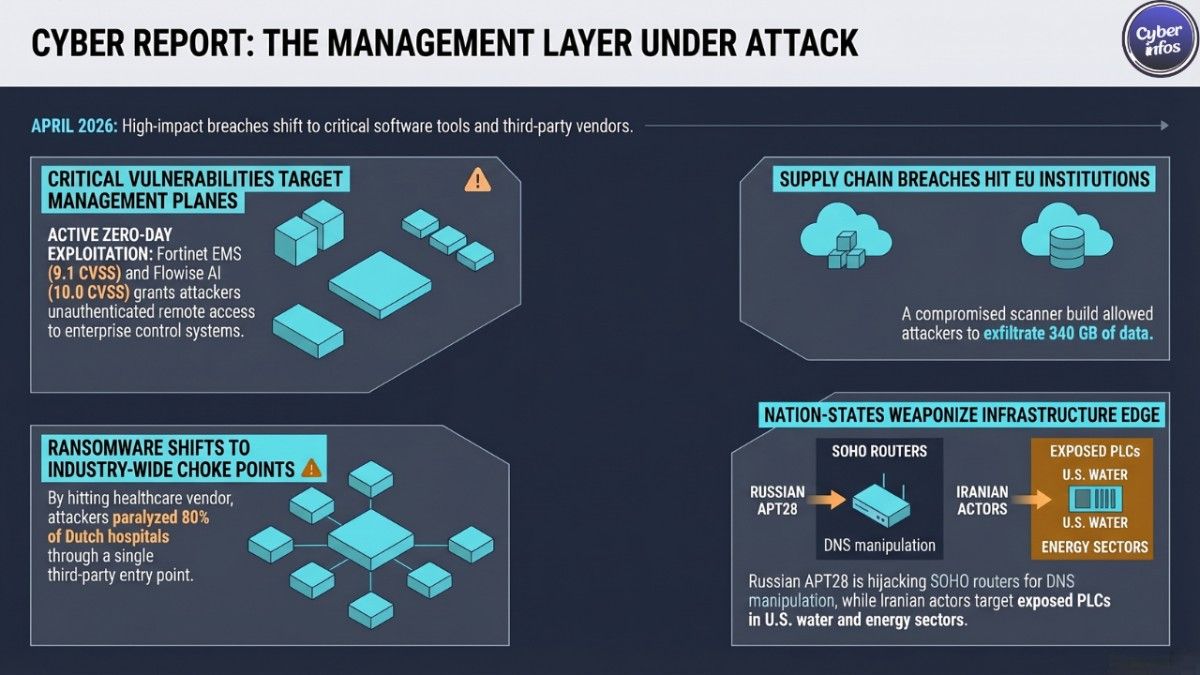
CERT-EU confirmed that attackers leveraged the earlier compromise of Aqua Security’s Trivy scanner to breach the European Commission’s Europa.eu AWS environment. A malicious Trivy build, tied to the TeamPCP campaign, captured an AWS API key with significant permissions, which the threat actor then used to create new access keys, conduct cloud reconnaissance, and exfiltrate about 340 GB of data (91.7 GB compressed) from Commission cloud accounts.
The exposed data set reportedly spans personal information, email content and metadata, internal documents, and records for at least 71 organizations, including 42 Commission “clients” and 29 other EU entities. ShinyHunters later published the archive on its leak site, turning a tooling compromise into a multi-institution data breach. The Commission says there is no evidence of further lateral movement but continues its incident response and regulatory obligations.
Cyberattack on Patriot Regional 911 Systems
In Massachusetts, the Patriot Regional Emergency Communications Center which provides public safety dispatch services for towns including Pepperell, Ashby, Dunstable, Groton, and Townsend announced that a cyberattack had disrupted operations. While 9-1-1 emergency calling remained available, non-emergency and business phone systems, as well as some town networks, were affected, forcing workarounds and manual processes.
Local officials brought in incident-response providers, state agencies, and law enforcement, but have not yet made public the intrusion vector, malware family, or responsible threat actor. Residents were asked to reserve 9-1-1 for genuine emergencies while restoration work continues.
Northern Ireland School Network Attack
The Education Authority in Northern Ireland disclosed a cyberattack against the C2K education IT platform, a shared infrastructure that underpins email, online learning, and administrative services across schools in the region. Detection around April 3 prompted a network-wide password reset, which temporarily blocked thousands of pupils and staff from key services just ahead of examination season.
The EA and contracted provider Capita have not yet confirmed whether personal data was accessed or exfiltrated, but they have notified the U.K. Information Commissioner’s Office and described the event as a serious intrusion now under police investigation. In practice, restoring access has meant extra site visits from IT staff and some teaching time lost to account recovery and testing.
ChipSoft Ransomware: EHR Platform Outages in the Netherlands and Belgium
Dutch healthcare software vendor ChipSoft, best known for its HiX electronic health-record suite used by roughly 80 percent of hospitals in the Netherlands, confirmed a ransomware attack that forced it to take systems offline. As part of containment, ChipSoft shut down its website and key portals, including HiX Mobile, Zorgportaal, and Zorgplatform, prompting Dutch healthcare CERT Z-CERT to advise customers to disconnect from the vendor while the incident is contained.
At least eleven Dutch hospitals and several Belgian institutions temporarily suspended patient portals, resorting to manual processes and assisted access to maintain care delivery. The company has acknowledged a possible “data incident” but has not yet clarified the scope of any data theft or named a responsible group.
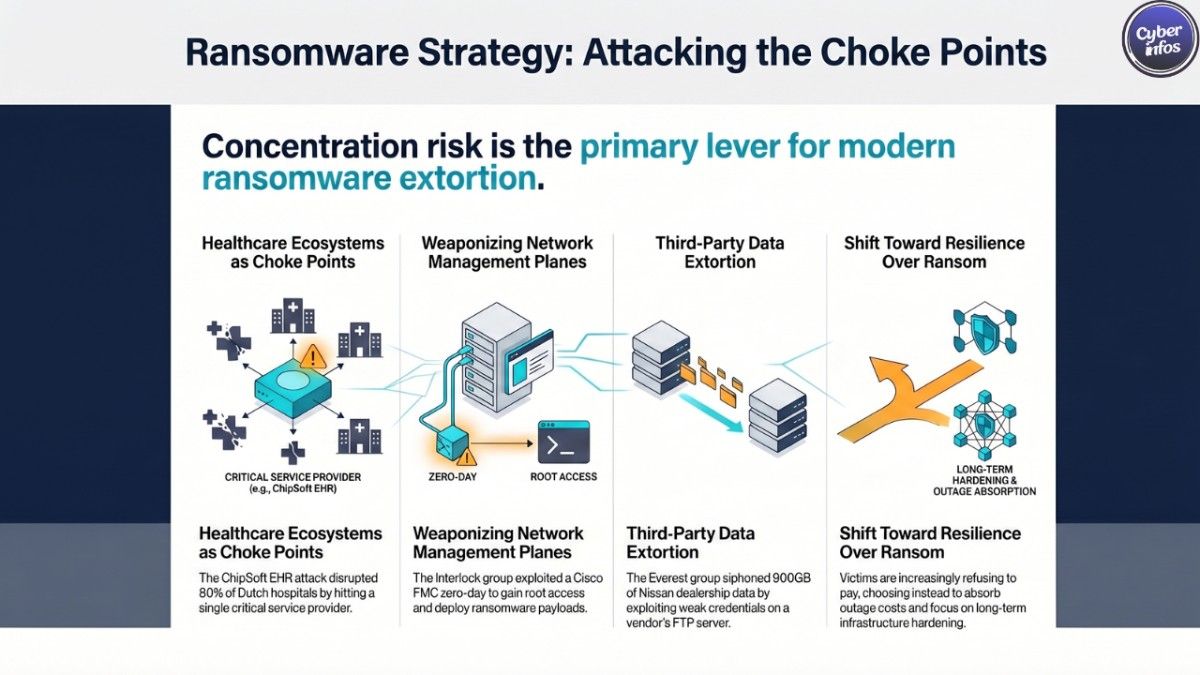
Nissan and Everest: Vendor Breach, Ongoing Extortion
Everest, a data-extortion-focused ransomware group, continued to publicize its claimed theft of around 900–910 GB of data linked to Nissan and Infiniti dealerships through a compromised vendor file-transfer environment. The group says the archive contains years of customer records, loan documents, dealership operational data, and employee information, allegedly siphoned from GCSSD Apps FTP servers that had weak, long-standing credentials and lacked MFA.
Nissan maintains that its own core systems were not breached and frames the issue as a third-party incident, but Everest has already posted data samples and negotiation logs after failed extortion attempts.
ANALYST INSIGHT: Across these incidents, the common threads are shared platforms cloud scanners, education networks, healthcare EHRs, dealer file-transfer systems and the governance or access layers around them. Teams treating platform and vendor ecosystems as part of their own attack surface will recover faster than those focusing only on traditional “internal vs external” boundaries.
New Vulnerabilities & Patches – Cybersecurity Weekly Report
[CVE] CVE-2026-35616 | Fortinet | FortiClient Enterprise Management Server (EMS) | CVSS: 9.1 | Exploited: Yes
CVE-2026-35616 is a high-severity improper access control flaw in Fortinet’s FortiClient EMS that allows unauthenticated remote attackers to execute arbitrary code or commands via crafted API requests, effectively bypassing authentication and authorization on the management server. Researchers and national CERTs report that attackers began exploiting the bug as a zero-day around late March, taking advantage of EMS instances exposed to the internet as an easy pre-auth foothold into enterprise environments.
Fortinet has released emergency hotfixes and integrated the fix into FortiClient EMS 7.4.7, while CISA has added the issue to the KEV catalog, requiring U.S. federal agencies to remediate on tight timelines. Organizations should patch immediately, remove direct internet exposure where possible, and run compromise assessments on any previously exposed instances.
[CVE] CVE-2025-59528 | Flowise | Flowise AI Agent Builder | CVSS: 10.0 | Exploited: Yes
CVE-2025-59528 is a maximum-severity remote code-execution vulnerability in Flowise, a popular open-source platform for building AI agents and workflows. The issue stems from insecure handling of JavaScript inside the Custom MCP node, allowing attackers to inject arbitrary code via configuration and achieve RCE on the underlying host.
Security researchers estimate that thousands of internet-exposed Flowise instances have been vulnerable, and exploitation has been ongoing for more than six months, with attackers using compromised nodes to run commands, drop payloads, and pivot deeper into networks. Flowise maintainers have shipped fixes from version 3.0.6 onward; admins should upgrade to the latest 3.1.x release, restrict external access to admin interfaces, rotate credentials, and review logs for suspicious MCP configurations or outbound connections.
[CVE] CVE-2026-34621 | Adobe | Acrobat / Acrobat Reader | CVSS: 8.6 | Exploited: Yes
Adobe pushed an out-of-band security update on April 11 for Acrobat and Acrobat Reader to address CVE-2026-34621, a prototype-pollution bug that can be abused via malicious PDFs to run arbitrary code with the user’s privileges. The flaw allows attackers to manipulate JavaScript object prototypes and chain that to privileged Acrobat APIs, and has reportedly been exploited in the wild since at least late 2025. Updated builds such as Acrobat/Reader DC 26.001.21411 and new Acrobat 2024 versions are now available for Windows and macOS, and organizations should prioritize rollout while treating unexpected PDF attachments as high-risk until coverage is verified.
[CVE] CVE-2026-5281 | Google | Chrome / Dawn (WebGPU) | CVSS: 8.8 | Exploited: Yes
CVE-2026-5281 is a use-after-free vulnerability in Dawn, the WebGPU component used by Chrome and other Chromium-based browsers. A crafted page can exploit the bug to gain code execution in the context of the browser process, especially when chained with sandbox-escape techniques. Google fixed the issue in Chrome 146.0.7680.178/177, and CISA added the CVE to the KEV catalog based on evidence of active exploitation, making browser patching a high-priority task for enterprises. Security teams should verify that managed endpoints are updated, block outdated builds, and consider limiting WebGPU where not needed.
Ivanti EPMM Zero-Days Remain High Priority
Earlier in the year, Ivanti disclosed CVE-2026-1281 and CVE-2026-1340, unauthenticated code-injection flaws in Endpoint Manager Mobile that allow RCE via crafted HTTP requests. Patches landed in late January, but exploitation as a zero-day and subsequent KEV listings make unpatched EPMM servers a continuing risk, particularly in environments that also depend on Fortinet EMS and Flowise.
PRIORITY ACTION: Use this week to identify every internet-facing management or AI-orchestration system FortiClient EMS, Ivanti EPMM, Flowise, browser fleets, and Acrobat/Reader deployments then combine rapid patching with exposure reduction and targeted threat hunting for each of the actively exploited CVEs.
Ransomware Activity – Cybersecurity Weekly Report
Healthcare Under Pressure: ChipSoft
The ChipSoft attack illustrated once again how ransomware operators are targeting healthcare “choke points” rather than individual hospitals. By hitting a vendor that provides core EHR services for most Dutch hospitals and some Belgian institutions, the attackers forced multiple organizations into portal shutdowns and manual workflows, even if their own networks weren’t encrypted. The group behind the intrusion has not yet been publicly named, but the operational impact delayed access to records, heavier administrative load, and heightened patient-safety concerns is clear. Full article
Everest’s Long-Running Nissan Extortion
Everest continued to rely on reputational pressure in its dispute with Nissan and an associated North American vendor, republishing claims that it holds around 900–910 GB of sensitive dealership data and highlighting the age and weakness of the FTP credentials allegedly used. Nissan continues to emphasize that its own corporate infrastructure was not directly compromised, but the visibility of leaked samples and negotiation logs keeps the brand under scrutiny and may increase legal and compliance risk around dealership data handling. Full article
Interlock Ransomware Weaponizes Cisco FMC Zero-Day
The Interlock ransomware group is actively exploiting CVE-2026-20131, a CVSS 10.0 unauthenticated RCE in Cisco Secure Firewall Management Center, to gain root access and deploy ransomware payloads. Telemetry suggests exploitation began roughly a month before Cisco publicly disclosed and patched the bug, and opportunistic scanning continues against any FMC or Cisco Security Cloud Control instances left exposed. Interlock’s willingness to burn a zero-day against high-value infrastructure reinforces how network-management planes have become prime ransomware targets. Full article
Payment and Enforcement Trends
Reporting across the public sector and healthcare indicates that more victims are choosing not to pay, instead absorbing outage costs, working with regulators, and strengthening resilience. Law-enforcement and cloud-provider partnerships continue to pressure established groups by disrupting infrastructure and exposing operations, but the gap is often filled by smaller, agile crews who rapidly pivot to new zero-days and third-party environments. Full article
ANALYST TAKEAWAY: Ransomware actors are paying close attention to concentration risk high-usage vendors and critical management planes knowing that a single successful intrusion can generate broad downstream impact and strong pressure on victims, even when core networks remain intact.

Threat Intelligence
APT28: DNS Hijacking at the Edge
Fresh analysis of Russian state-linked group APT28 shows an ongoing campaign against SOHO routers, especially TP-Link and MikroTik devices running outdated firmware. Once compromised, the routers are reconfigured to use attacker-controlled DNS servers, allowing adversary-in-the-middle attacks against Outlook and other services while traffic otherwise appears normal. This edge-focused strategy targets home and small office users connected into enterprise environments, bypassing traditional perimeter defenses.
Iranian Campaigns Against U.S. OT and PLCs
A joint U.S. government advisory details how Iranian-aligned actors, including clusters linked to the IRGC and CyberAv3ngers, have been compromising internet-exposed PLCs and OT devices used across water, energy, and local-government sectors. In several cases, the threat actors manipulated engineering project files, HMI screens, and control logic on Rockwell/Allen-Bradley devices, causing disruption and forcing operators into manual modes with real financial impact. Scans suggest thousands of similar devices remain reachable from the internet, many without strong authentication or monitoring.
UNC6783: Social Engineering the Help Desk
On the financially motivated side, UNC6783 is using well-crafted social-engineering calls and messages to internal help desks and BPOs to obtain password resets and MFA changes for high-value accounts. Once they control these accounts, the group performs data theft and extortion, often without deploying traditional malware or encryptors, which can make detection more challenging.
Key TTPs
- [TTP] Adversary-in-the-Middle (ATT&CK ID: T1557) – APT28’s campaign demonstrates router-level DNS hijacking to intercept traffic to services like Outlook and harvest credentials and tokens while keeping victim workflows intact.
- [TTP] Phishing (ATT&CK ID: T1566) – UNC6783 and other groups continue to rely on convincing social-engineering lures and phone-based phishing to bypass technical defenses by manipulating human processes around identity and access.
- [TTP] Exploit Public-Facing Application (ATT&CK ID: T1190) – Interlock’s exploitation of Cisco FMC, combined with broad scanning for Flowise and Fortinet EMS instances, exemplifies widespread abuse of exposed management planes and AI-adjacent services.
Notable IOCs
- [IOC] IP | 5.226.137.151 – Malicious DNS server used in APT28 router-level hijacking operations.
- [IOC] IP | 185.237.166.224 – VPS infrastructure hosting attacker-controlled DNS for APT28 campaigns.
- [IOC] Domain | autodiscover-s.outlook[.]com – Legitimate Outlook hostname abused in APT28 redirection flows; monitor for resolution to unexpected IP ranges.
- [IOC] CVE | CVE-2026-20131 – Cisco Secure FMC RCE used by Interlock; any unpatched, internet-exposed FMC should be considered high-risk.
Attribution Snapshot
APT28 (Forest Blizzard), attributed to Russia’s GRU unit 26165, is leaning heavily on router and DNS infrastructure for stealthy credentials theft. Iranian-aligned operators are doubling down on OT disruption across U.S. critical infrastructure. UNC4736, a DPRK-linked financial theft unit, is expanding from exchange and wallet attacks into governance-layer compromises of DeFi platforms such as Drift.
Industry News
U.S. Advisory on Iranian Targeting of Critical Infrastructure
U.S. agencies issued a joint advisory warning that Iranian government-aligned actors are actively targeting OT systems in water, wastewater, energy, and government sectors, with some activity already causing disruptions and financial losses. The guidance stresses removing PLCs and other OT controllers from direct internet exposure, tightening remote access pathways, and monitoring engineering workstations for suspicious activity.
APT28 Router Guidance from NCSC
The U.K. NCSC released an advisory on APT28’s exploitation of SOHO routers to support DNS hijacking operations, including details on targeted TP-Link models, malicious IP ranges, and abused Outlook domains. The document includes practical advice on upgrading firmware, hardening router configurations, and monitoring for unauthorized changes to DNS and DHCP settings, underscoring that home and small office gear has become part of the national attack surface.
CISA KEV Updates
CISA extended its Known Exploited Vulnerabilities catalog with Fortinet’s CVE-2026-35616 in FortiClient EMS and Ivanti EPMM CVE-2026-1340, both confirmed as exploited in the wild, on top of the already listed Chrome Dawn bug CVE-2026-5281. The additions highlight a consistent pattern: threat actors are going after management servers, MDM platforms, and browsers that sit in front of large user populations and device fleets.
MITRE ATT&CK v19 Coming April 28
MITRE ATT&CK v19, scheduled for April 28, will split the existing Defense Evasion tactic into two new tactics—Stealth and Impair Defenses sharpening how different behaviors are categorized.
Funding Signals for AI-Driven Security
Recent funding rounds show strong investor interest in AI-driven detection and response platforms, as well as tools for secure coding and autonomous testing.
STRATEGIC NOTE: Regulators, frameworks, and funding flows are converging on the same themes exploited management-plane flaws, AI-driven security, and supply-chain risk.

Tool Updates
Metasploit Adds Modern Exploits and Stability
Metasploit Pro 5.0.0‑2026040201 shipped with new exploit modules for recent vulnerabilities, including RCEs in Eclipse Che, FreeScout, AVideo Encoder, FreePBX filestore, and Barracuda ESG, along with a generic HTTP OS command‑execution module and persistence options via UserInitMprLogonScript. A separate update roundup highlights performance improvements to MSFVenom payload generation and new modules for Cisco Catalyst SD‑WAN and osTicket, ensuring the framework keeps pace with the vulnerabilities currently being weaponized. For red teams and security testers, these changes make it easier to reproduce real‑world attack paths in controlled environments.
AI-Focused Security and Testing Frameworks
GitHub Security Lab’s Taskflow Agent continues to gain traction as an AI‑powered framework for automated vulnerability discovery, with recent commentary emphasizing its ability to spot authentication bypasses, IDORs, and token leaks in complex codebases. Combined with the week’s focus on Flowise and Trivy‑related threats, this points toward a future where AI‑assisted tools are used both to build and to break modern software, making strong governance around those tools critical.
ATT&CK v19 Preparation for SOCs
ATT&CK v19’s shift from Defense Evasion to separate Stealth and Impair Defenses tactics will require updates in SIEM and SOAR content that rely on tactic‑level tagging. Teams should start by inventorying detections mapped to TA0005 and T1562, then planning how to remap them once the new matrix goes live so visibility and reporting remain consistent.
PRACTICAL TIP: Use this period to refresh both offensive (Metasploit modules) and defensive (ATT&CK mappings, AI‑based testing like Taskflow) tooling around the exact technologies Fortinet, Ivanti, Flowise, Trivy that attackers are actively probing today.
Looking Ahead
Three Trends to Watch First, expect continued exploitation of exposed management‑plane services FortiClient EMS, Ivanti EPMM, Cisco FMC, and AI platforms such as Flowise especially as more proof‑of‑concept code appears and patching lags in large environments. Second, Iranian OT campaigns are unlikely to slow down, and may expand to additional sectors or geographies if geopolitical tensions remain high, making basic hygiene on PLCs and engineering workstations an urgent priority. Third, supply‑chain compromises aimed at security and AI tooling Trivy today, another DevSecOps component tomorrow will remain attractive as long as they offer “one‑to‑many” access into high‑value environments.

