Enterprise breaches dont happen overnight, as a dramatic one-off event. In fact, according to recent incident response reports, attackers often linger inside corporate networks undetected for more than 200 days before anyone even starts to suspect something is amiss. Metasploit Pro 5.0.0 by the time security teams do figure it out, the bad guys have had months to quietly get their foot in the door – moving sideways, escalating their privileges & getting themselves all cozy with the network architecture.
Its this very reason why our offensive security tools need to stay one step ahead of the attackers at an incredible pace. Metasploit Pro 5.0.0 reflects this change, released by Rapid7 on the 12th of march 2026. The latest update adds more tools for the attackers, in particular, new exploitation modules, better AD CS attack capabilities, more flexible authentication options & collaboration features that are designed with modern red team operations in mind.
But this update isnt just about new bells & whistles. Its the sign that penetration testing tools are finally catching up with the real world timelines of attacks as they happen. In the following article, we’ll take a closer look at whats changed in Metasploit Pro 5.0.0 & explain in simple terms why its all a big deal for both security teams & penetration testers.
What’s New in Metasploit Pro 5.0.0?
The Metasploit Pro 5.0.0 release introduces several notable updates across the penetration testing workflow.
Rapid7 added four new modules, expanded AD CS exploitation capabilities, redesigned parts of the interface, and introduced enterprise-grade authentication.
In practical terms, that means security teams now have stronger tooling for:
- Reconnaissance
- Exploitation
- Attack simulation
- Multi-operator collaboration
- Enterprise deployment
Some of these improvements are subtle. Others could reshape how red team engagements unfold inside large enterprise environments. Let’s start with the new modules because a few of them are particularly interesting.
Four Powerful New Modules
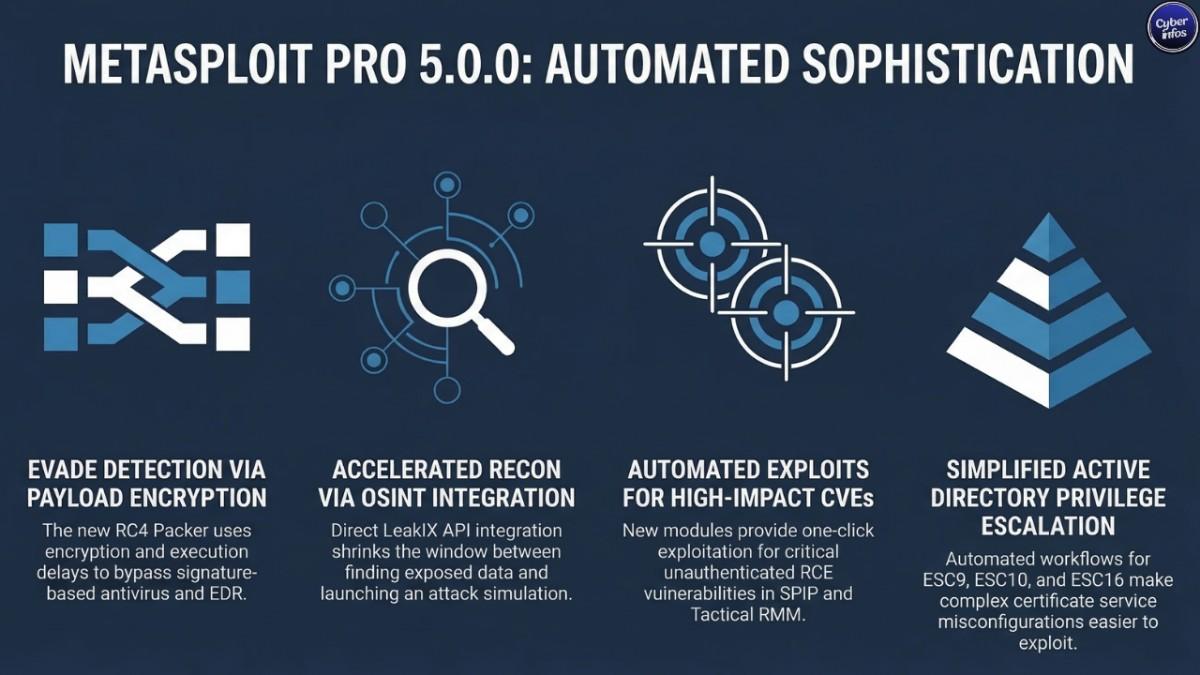
RC4 Packer Evasion Module – evasion/linux/x64/rc4_packer
One of the more intriguing additions in Metasploit Pro 5.0.0 is the RC4 packer evasion module, designed to make payload delivery harder for security tools to detect.
The module encrypts Linux x64 payloads using RC4 encryption. It can also introduce an execution delay using a nanosleep-based mechanism before decrypting and running the payload.
Why does that matter?
Because many antivirus and endpoint detection systems still lean heavily on signature-based detection. Change the payload structure encrypt it, delay execution, mimic normal system behavior and detection rates often drop.
In practical terms, a payload that might normally get flagged immediately could slip through long enough to execute.
For red teams, the module allows more realistic simulation of stealth techniques used by advanced attackers.
For blue teams, it exposes a persistent weakness.
Signature-only defenses are struggling to keep up. Testing against evasion techniques like this is no longer optional even if many organizations still treat it that way.
LeakIX OSINT Recon Module – auxiliary/gather/leakix_search
Reconnaissance rarely gets the spotlight. Yet it’s where many successful intrusions actually begin.
The new LeakIX OSINT reconnaissance module integrates directly with the LeakIX API, allowing Metasploit users to search for exposed services, leaked credentials, and publicly accessible databases that have already been indexed across the internet.
Instead of jumping between multiple OSINT platforms, penetration testers can now pull that intelligence directly inside the Metasploit environment.
That might sound like a convenience feature. But it reflects a broader shift. Modern penetration testing frameworks are increasingly merging open-source intelligence with exploitation tooling, shrinking the time between discovery and attack simulation.
And here’s the part defenders sometimes forget. Attackers have been using these exact data sources for years.
CVE-2025-71243 – SPIP Saisies PHP Code Injection
Another addition introduces support for exploiting CVE-2025-71243, a vulnerability affecting the SPIP content management system.
SPIP is widely used across public institutions and organizations in Europe. The flaw resides in the Saisies plugin, where improper input handling allows attackers to inject malicious PHP code.
What makes this vulnerability particularly dangerous is that exploitation does not require authentication.
Once an exploit module lands inside a framework like Metasploit Pro 5.0.0, the barrier to entry drops dramatically. Attackers no longer need to build proof-of-concept code themselves.
They simply run the module. Security teams have seen this pattern repeatedly: once a vulnerability receives Metasploit support, exploitation activity tends to spike soon after.
Organizations running SPIP should treat CVE-2025-71243 as a priority patching issue. History suggests attackers certainly will.
CVE-2025-69516 – Tactical RMM Jinja2 SSTI Remote Code Execution
The fourth module targets CVE-2025-69516, affecting Tactical RMM, an open-source remote monitoring and management platform.
The vulnerability stems from a Jinja2 Server-Side Template Injection (SSTI) flaw that allows authenticated users to execute arbitrary code on the server.
On paper, authentication requirements can make a vulnerability look less urgent. But think about what RMM platforms actually control.
These systems often maintain administrative access across dozens sometimes hundreds of endpoints. If an attacker obtains valid credentials through phishing, password reuse, or credential stuffing, this vulnerability could provide a foothold across managed infrastructure.
In other words, one compromised account could cascade into a network-wide breach. Organizations using Tactical RMM should update to version 1.4.0 or later as quickly as possible.
Expanded AD CS Exploitation: ESC9, ESC10, and ESC16
One of the most significant improvements in Metasploit Pro 5.0.0 is the expansion of AD CS exploitation workflows.
Active Directory Certificate Services vulnerabilities became a major topic in enterprise security after SpecterOps published its influential Certified Pre-Owned research.
Many organizations deploy certificate services without fully understanding the security risks involved. Misconfigurations in certificate templates or CA settings can allow attackers to escalate privileges inside Active Directory sometimes all the way to domain administrator.
And those misconfigurations are surprisingly common.
Metasploit now supports additional exploitation scenarios, including:
- ESC9 – Missing certificate template security extensions
- ESC10 – Weak certificate mappings enabling privilege escalation
- ESC16 – Disabled CA security extensions enabling impersonation attacks
What’s striking here is how accessible these attack paths have become.
Techniques that once required manual scripting and deep AD CS knowledge can now be demonstrated through automated Metasploit Pro workflows. That dramatically lowers the barrier for penetration testers — and for attackers experimenting with the same techniques.
For many organizations, auditing AD CS configurations has suddenly moved up the priority list.
Major Enhancements in Metasploit Pro 5.0.0
New modules tend to grab headlines. But some of the platform improvements in Metasploit Pro 5.0.0 may have an even bigger operational impact.
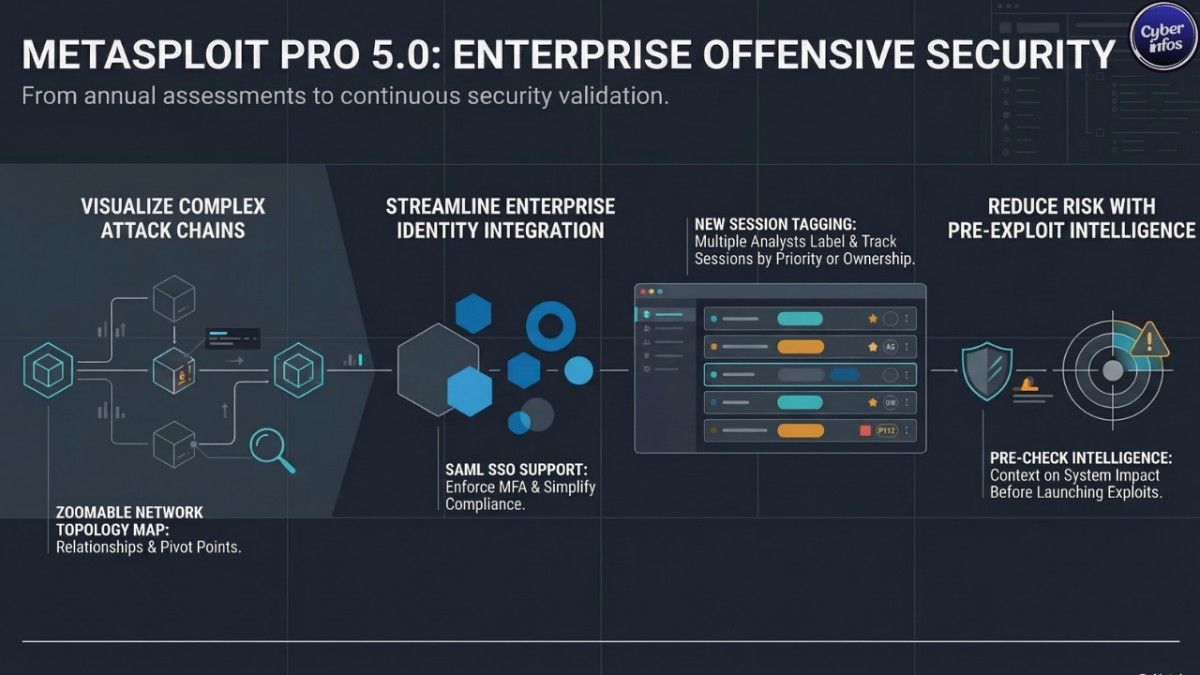
Redesigned UI and Network Topology Visualization
The updated interface introduces a new network topology visualization system.
Security analysts can now navigate environments through a zoomable network map that displays relationships between compromised systems, pivot points, and attack paths.
During large enterprise engagements where dozens or even hundreds of hosts might be involved — tracking these connections can quickly become messy.
Visualization changes that dynamic. Instead of scrolling through lists of sessions and hosts, analysts can see the attack chain unfold visually across the network.
And that clarity matters more than people think. When engagements get complex, situational awareness becomes everything.
SAML Single Sign-On Support
Enterprise deployments often require centralized authentication.
With Metasploit Pro 5.0.0, organizations can now enable SAML Single Sign-On, integrating the platform with identity providers such as:
- Okta
- Azure Active Directory
- Ping Identity
- Google Workspace
This allows teams to enforce existing multi-factor authentication policies and eliminates the need for separate credentials tied to penetration testing infrastructure.
For organizations operating under compliance frameworks like SOC 2 or ISO 27001, this change could make Metasploit easier to deploy internally.
It’s not the flashiest feature in the release. But it may quietly remove one of the biggest friction points for enterprise adoption.
Session Tagging for Team Engagements
Large red team operations rarely involve a single analyst.
The new session tagging feature allows operators to label active sessions with identifiers such as environment type, priority level, or analyst ownership.
At first glance, it feels minor. But anyone who has worked on a multi-operator engagement knows how quickly things can spiral into chaos when dozens of sessions are active simultaneously.
Small workflow improvements like this can dramatically reduce confusion. And sometimes, avoiding confusion is half the battle.
Vulnerability Pre-Check Intelligence
Metasploit Pro 5.0.0 also introduces vulnerability pre-check intelligence, providing operators with additional context before launching exploit modules.
This allows analysts to better understand potential system impact before triggering an exploit attempt.
That matters more than it sounds. Real-world penetration tests often run against production systems, not lab environments. Accidentally crashing a server or interrupting business operations is the last thing most testers want to do.
Pre-exploitation insight helps reduce that risk.
The Bigger Picture: Continuous Security Validation
The most interesting aspect of Metasploit Pro 5.0.0 isn’t any single feature. It’s what those features collectively signal.
For years, penetration testing followed a predictable rhythm: conduct an annual assessment, produce a report, patch vulnerabilities, and repeat the cycle the following year. But attackers don’t follow annual schedules.
New vulnerabilities surface every week. Public exploit code often appears within days of disclosure. Automated scanners constantly sweep the internet looking for exposed services.
Security teams have started responding by shifting toward continuous security validation regularly simulating attacks instead of waiting for the next yearly engagement.
Tools like Metasploit are evolving to support that model. And frankly, they have to.
Frequently Asked Questions (FAQ)
What is Metasploit Pro 5.0.0?
Metasploit Pro 5.0.0 is the latest version of Rapid7’s commercial penetration testing platform. It builds on the Metasploit Framework by adding enterprise capabilities such as automated exploitation workflows, collaboration features for red team tools, reporting, and integrations designed for professional penetration testing teams.
What new features are included in Metasploit Pro 5.0.0?
The Metasploit Pro 5.0.0 release introduces four new modules, expanded AD CS exploitation support, improved network topology visualization, session tagging for team operations, vulnerability pre-check intelligence, and SAML Single Sign-On integration for enterprise environments.
Why is AD CS exploitation important in Metasploit Pro 5.0.0?
Active Directory Certificate Services (AD CS) misconfigurations have become a common privilege escalation path in enterprise networks. Metasploit Pro 5.0.0 now supports exploitation techniques related to ESC9, ESC10, and ESC16 scenarios, allowing penetration testing teams to simulate attacks that abuse certificate-based authentication in Active Directory environments.
What vulnerabilities are supported in the new Metasploit Pro modules?
The release includes modules targeting vulnerabilities such as CVE-2025-71243 affecting the SPIP Saisies plugin and CVE-2025-69516 impacting Tactical RMM through a Jinja2 Server-Side Template Injection (SSTI). These modules allow security professionals to test whether their environments are vulnerable to real-world exploitation techniques.
How does the RC4 packer module help with penetration testing?
The RC4 packer evasion module encrypts Linux x64 payloads using RC4 encryption and introduces execution delays through nanosleep mechanisms. This helps simulate how advanced attackers evade antivirus and endpoint detection systems during real-world attacks.
What is the LeakIX module used for in Metasploit Pro 5.0.0?
The LeakIX reconnaissance module integrates with the LeakIX API to identify exposed services, leaked credentials, and publicly accessible databases indexed across the internet. This allows penetration testers to gather open-source intelligence directly within the Metasploit workflow.
Does Metasploit Pro 5.0.0 support enterprise authentication?
Yes. Metasploit Pro 5.0.0 introduces SAML Single Sign-On support, allowing organizations to integrate the platform with identity providers such as Okta, Azure Active Directory, Ping Identity, and Google Workspace.
How does Metasploit Pro support red team collaboration?
The platform now includes session tagging and improved network visualization features that help multiple analysts track compromised systems, pivot points, and attack paths during complex red team engagements.
Why is Metasploit important for security teams?
Metasploit is widely used for penetration testing and security validation because it allows organizations to simulate real attack techniques safely. By testing systems with the same methods used by threat actors, defenders can identify weaknesses before attackers exploit them.
Where can security professionals download Metasploit Pro?
Metasploit Pro can be obtained directly from Rapid7’s official website. Organizations typically access it through enterprise licensing, while the open-source Metasploit Framework remains freely available for security research and penetration testing.
Final Thoughts
With Metasploit Pro 5.0.0, Rapid7 has delivered one of the more meaningful updates the platform has seen in recent years.
The combination of new exploit modules, expanded AD CS exploitation capabilities, improved evasion techniques, and enterprise authentication support makes the framework more practical for modern penetration testing and red team tools workflows.
But there’s a broader takeaway here. The techniques appearing inside Metasploit aren’t theoretical exercises. They reflect attack methods already being used by real threat actors in active campaigns.
So the real question for defenders isn’t whether these techniques exist. It’s whether their security controls can detect them.
Because if your environment can’t catch these attack simulations today, odds are it won’t catch the real attack tomorrow either. And by the time you discover that gap, the attackers will already be inside.