A dramatic escalation in cyber operations is unfolding alongside the military conflict between the United States, Israel, and Iran.
Within hours of the February 28, 2026 airstrikes codenamed Operation Epic Fury by the U.S. and Operation Roaring Lion by Israel cybersecurity researchers began tracking a surge in Iran cyber attacks 2026 and retaliatory hacktivist activity spreading across the Middle East. The speed of the response is striking.
According to threat intelligence from Radware and multiple cybersecurity firms, hacktivist groups mobilized almost immediately, launching coordinated distributed denial-of-service (DDoS) campaigns against government infrastructure, telecommunications providers, and financial institutions. In just a matter of days, 149 DDoS attack claims targeted 110 organizations across 16 countries, a sharp reminder that geopolitical conflicts now spill into cyberspace almost instantly.
What’s notable here isn’t just the volume of attacks it’s how quickly loosely organized digital groups can mobilize once a geopolitical trigger occurs.
The attacks reflect a broader pattern in Middle East hacktivist attacks, where politically motivated groups increasingly use cyber disruption as a form of digital retaliation. Researchers also warn that state-aligned actors linked to the Islamic Revolutionary Guard Corps (IRGC) could expand operations toward energy infrastructure and cloud environments if tensions continue to escalate.
In other words, what began as military escalation may rapidly evolve into a sustained cyber conflict.
This article breaks down what happened, how these cyber attacks work, who is most at risk, and what organizations should be doing right now as the cyber front of the conflict intensifies.
What Happened: Hacktivist Campaign After Epic Fury
The cyber escalation began almost immediately after U.S. and Israeli forces launched coordinated strikes against Iranian military and nuclear infrastructure on February 28, 2026.
Within nine hours of the strikes, hacktivist groups aligned with pro-Iranian or pro-Palestinian causes began targeting organizations across the Middle East using DDoS attacks and hack-and-leak campaigns.
Nine hours. That’s barely enough time for many organizations to issue internal security alerts yet it was enough for attackers to organize and begin coordinated operations.
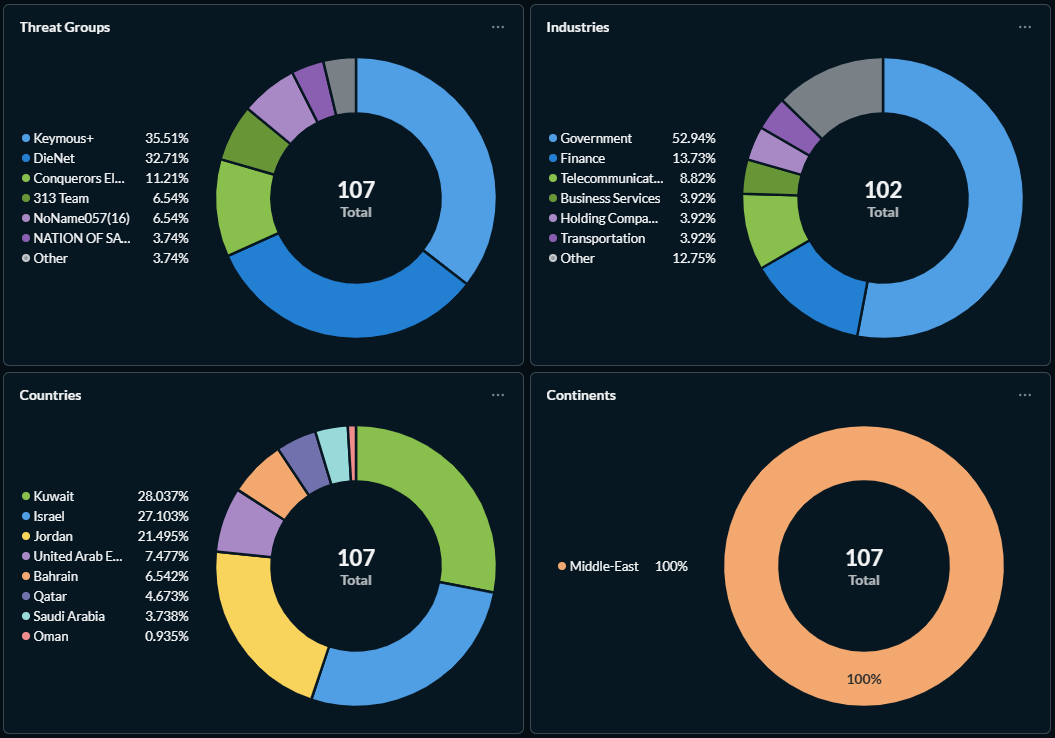
Threat intelligence data shows:
- 149 hacktivist DDoS attack claims
- 110 organizations targeted
- 16 countries affected
- 12 different hacktivist groups involved
Two groups Keymous+ and DieNet accounted for nearly 70% of all attack activity during the first days of the campaign. (Radware)
Other groups involved included:
- NoName057(16)
- Nation of Saviors (NOS)
- Conquerors Electronic Army
- Handala Hack
- Dark Storm Team
- Cyber Islamic Resistance
- Sylhet Gang
- FAD Team
- Evil Markhors
Researchers attribute the first confirmed attack to Hider Nex (Tunisian Maskers Cyber Force), a pro-Palestinian hacktivist group known for combining DDoS operations with stolen-data leaks designed to amplify political messaging.
Geographically, the attacks concentrated heavily in the Middle East. Kuwait, Israel, and Jordan accounted for more than 76% of attack claims, while Europe represented roughly 22.8% of global activity.
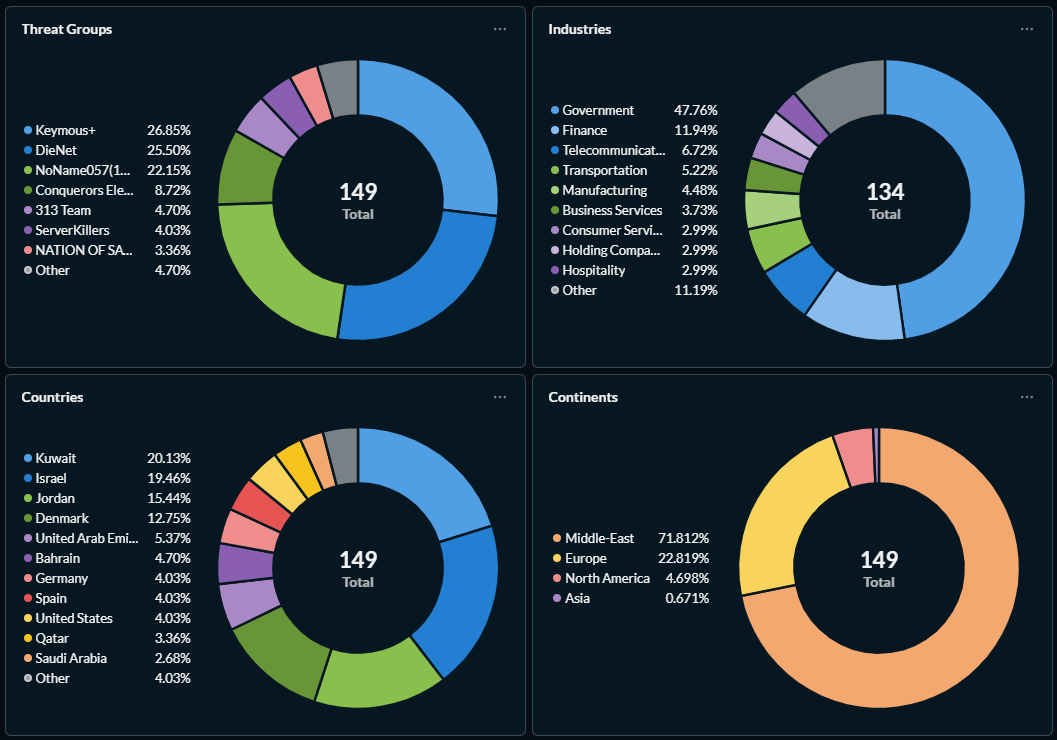
Nearly 48% of targeted organizations were government entities, followed by financial services and telecommunications providers. And that distribution matters.
Government services going offline even briefly creates political pressure. That’s often the real objective behind hacktivist campaigns.
How Iran cyber attacks 2026 Works
Most of the activity observed so far involves distributed denial-of-service (DDoS) attacks, a technique designed to overwhelm servers and make websites or online services unavailable.
Think of a DDoS attack as a deliberate traffic jam on a digital highway.
Instead of legitimate users visiting a website, attackers control thousands or sometimes millions of compromised computers known as botnets. These machines simultaneously send massive volumes of requests to a target system. The result is predictable.
Server resources such as bandwidth, CPU power, and memory get consumed almost instantly. When systems can’t handle the load, legitimate users are locked out.
In practical terms, a government portal or banking login page simply stops working. Hacktivist groups typically rely on several types of DDoS techniques:
1. Volumetric Attacks
Massive data floods designed to saturate internet bandwidth and overwhelm network capacity.
2. Application-Layer Attacks
More targeted assaults aimed at specific web services such as login portals or APIs. These attacks often require less traffic but can be surprisingly disruptive.
3. Amplification Attacks
These exploit misconfigured internet servers such as DNS or NTP systems to multiply attack traffic and increase the impact. But the bigger story is how attackers combine multiple tactics.
In the current conflict, threat actors have paired DDoS campaigns with data leaks, website defacement, and phishing operations, creating a broader information warfare strategy designed to embarrass and destabilize targets.
Researchers also observed a malicious replica of Israel’s RedAlert mobile application circulating in SMS phishing campaigns. Victims who install the fake application unknowingly deploy surveillance malware disguised as emergency updates.
And yes those kinds of attacks work far more often than many organizations are comfortable admitting.
Who Is at Risk in Iran cyber attacks 2026 ?
The risk extends well beyond the immediate conflict zone.
According to cybersecurity firms including SentinelOne and Unit 42, organizations operating in the following sectors face elevated risk levels:
1. Government and Public Infrastructure
Nearly half of all attacks observed so far targeted government agencies.
2. Energy and Critical Infrastructure
Iranian cyber actors have historically focused on oil, gas, and power systems industries where disruption can ripple across entire economies.
3. Financial Services
Banks and payment systems remain attractive targets because outages generate immediate public attention.
4. Telecommunications and Cloud Services
Disrupting these platforms can amplify the impact of cyber attacks across multiple sectors simultaneously.
Countries most heavily targeted include:
- Israel
- Kuwait
- Jordan
- Saudi Arabia
- United Arab Emirates
- Several European nations
But analysts warn that U.S. and Western organizations could quickly become secondary targets as the conflict evolves. (The Wall Street Journal)
And that’s where things get complicated.
Many multinational companies operate infrastructure or cloud services that support organizations in the Middle East. That creates indirect exposure even if the company itself isn’t politically involved.
Expert Analysis: Why This Matters
Cybersecurity experts view the current wave of attacks as a classic example of asymmetric cyber warfare.
Iran has historically used cyber operations to retaliate against militarily stronger adversaries without triggering full-scale war. The strategy allows pressure to be applied without crossing traditional military red lines.
The current escalation fits that pattern almost perfectly.
According to cybersecurity researchers, Iran-aligned actors frequently combine espionage, disruption, and psychological operations to pressure adversaries and influence political narratives. (Unit 42)
Cynthia Kaiser, former Deputy Assistant Director of the FBI’s Cyber Division and now SVP at Halcyon, warns that Tehran often tolerates independent cybercriminal groups targeting Western organizations. Why?
Because it provides plausible deniability. These actors can launch ransomware campaigns, leak stolen data, or conduct disruptive attacks that align with national interests while the government officially maintains distance.
Hacktivist mobilization adds another layer of complexity. Online communities sympathetic to political causes can coordinate attacks rapidly, dramatically increasing cyber activity during geopolitical crises.
We’ve seen similar patterns before:
- The Russia-Ukraine war
- The 2023 Israel-Hamas conflict
- The 2024 Red Sea shipping crisis
Each conflict triggered waves of politically motivated cyber activity.
The uncomfortable truth is that cyber warfare is no longer an occasional side effect of geopolitical conflict. It’s becoming a standard feature.
What You Should Do Right Now
Organizations especially those connected to the Middle East, Israel, or U.S. interests should take defensive steps immediately.
Waiting until an attack begins is rarely effective.
1. Strengthen DDoS Protection
Deploy cloud-based DDoS mitigation services or traffic-scrubbing solutions capable of absorbing large traffic spikes.
2. Monitor Threat Intelligence Feeds
Threat indicators evolve quickly during geopolitical conflicts. Security teams should regularly update detection rules and indicators of compromise.
3. Reduce External Attack Surface
Identify unnecessary internet-exposed services, misconfigured APIs, and forgotten infrastructure that attackers could target.
4. Segment IT and OT Networks
Operational technology systems controlling industrial infrastructure should remain isolated from corporate IT networks.
5. Train Employees on Phishing
Conflict-themed phishing campaigns frequently accompany cyber conflicts.
6. Secure Mobile Applications
Employees should be warned about sideloaded applications or malicious APK files disguised as emergency alerts or government updates.
Security agencies such as the U.K. National Cyber Security Centre and CISA also recommend maintaining continuous monitoring and incident response readiness during periods of geopolitical instability.
Because once cyber campaigns begin, they rarely remain limited to a single region.
Timeline of Events
January 2026
Tensions escalate after nuclear negotiations between the United States and Iran collapse.
February 28, 2026
U.S. and Israeli forces launch coordinated strikes under Operation Epic Fury / Roaring Lion.
February 28, 2026 (within hours)
Hacktivist groups begin launching DDoS campaigns targeting Middle Eastern infrastructure.
March 1–2, 2026
More than 100 organizations across multiple countries report disruptions.
March 3–4, 2026
Cybersecurity researchers confirm 149 hacktivist attack claims across 16 countries.
Final Thoughts
The surge in Iran cyber attacks 2026 shows how modern geopolitical conflicts increasingly unfold across both physical and digital battlefields.
Hacktivist groups, state-aligned actors, and cybercriminal proxies are exploiting global tensions to launch disruptive attacks against government systems and critical infrastructure.
Many of the current incidents involve relatively unsophisticated DDoS campaigns. But that may not last.
More destructive tools such as wiper malware, ransomware operations, or infrastructure-targeting attacks could easily follow if tensions escalate further. And that’s the uncomfortable reality for organizations worldwide.
Geopolitical events can translate into cyber risk almost overnight. The real question isn’t whether cyber spillover will happen it’s whether organizations will recognize the warning signs early enough to respond.
Because by the time disruptions make headlines, attackers are usually already several steps ahead.

