In early 2026, the FBI began quietly investigating what it described as “suspicious activity” inside one of its internal systems used to manage surveillance and wiretap warrants. At first, it sounded like routine incident response something federal networks deal with more often than most people realize.
But within days, multiple outlets confirmed something more serious. An FBI surveillance management network essentially the database used to track court-approved wiretaps and foreign intelligence surveillance warrants had been breached. This is not just another FBI cybersecurity breach.
When the system that tracks who is legally being wiretapped becomes the target of hackers, the consequences ripple far beyond IT security. National security. Civil liberties. Public trust in federal surveillance powers. All of it suddenly sits under a microscope.
And that’s the uncomfortable reality behind the FBI wiretap breach 2026 story.
Quick overview: What happened?
Here’s what public reporting and official statements confirm so far:
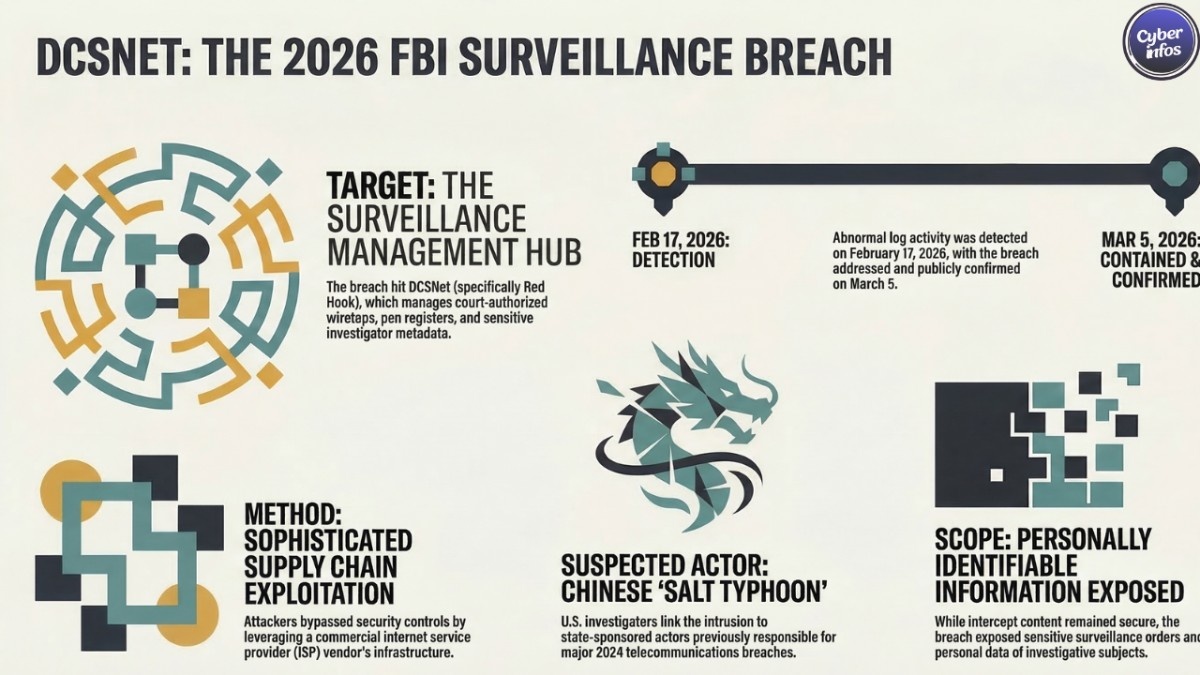
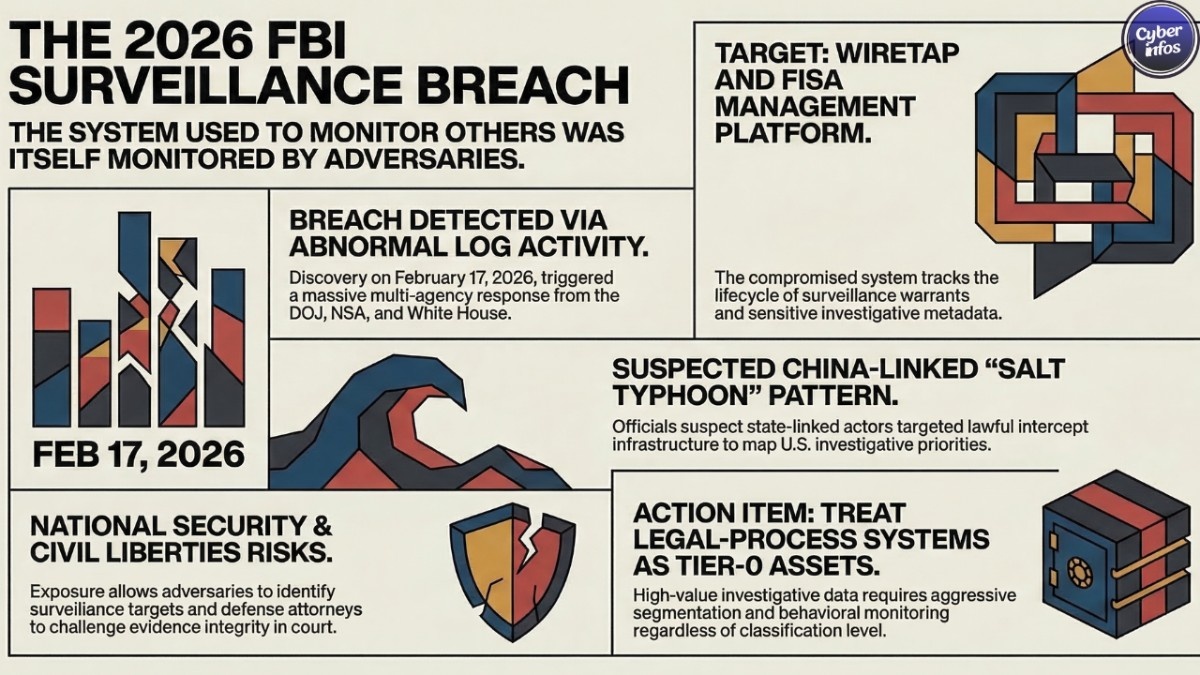
- The FBI detected abnormal activity on an internal network on February 17, 2026, triggering a cyber investigation.
- The affected environment reportedly supports management of court-ordered wiretaps and foreign intelligence surveillance warrants.
- The FBI has confirmed suspicious activity affecting systems tied to surveillance and wiretap management but has not released technical details.
- U.S. officials reportedly suspect a China-linked threat actor, though no formal attribution has been announced.
Think about what that actually means.
The infrastructure used to manage surveillance the system that determines who is being monitored under legal authority may itself have been monitored. And yes, that irony hasn’t gone unnoticed in the cybersecurity community.
Timeline of the FBI wiretap breach 2026
February 17, 2026 – Suspicious activity detected
According to congressional notifications and reporting summaries, investigators first spotted unusual log activity on February 17, 2026 tied to an internal FBI network system.
That discovery triggered an internal investigation and quickly escalated into a broader federal response involving the Department of Justice, the White House, and national security agencies.
One detail stands out here: abnormal logs were the first clue. Which means the attackers may have already been inside the system before anyone noticed.
Early March 2026 – Public disclosure begins
By early March, reporting from CNN, BleepingComputer, and The Register began connecting the suspicious activity to a digital platform used to manage surveillance and wiretap warrants.
The FBI publicly acknowledged the incident, confirming “suspicious activity” within its network.
Officials said the issue had been identified and addressed, but declined to explain:
- how attackers gained access
- how long they remained inside
- what data, if any, was accessed
That silence is typical during federal investigations. But it also leaves a lot of unanswered questions the kind security analysts will be digging into for months.
March 6 – 7, 2026 – Suspected China link reported
In early March, Reuters and several other outlets reported that U.S. officials suspect hackers linked to the Chinese government targeted the FBI system.
The environment reportedly sits on an unclassified FBI network but contains communications-related data tied to domestic surveillance orders.
At the time of writing, there is still no official attribution or public technical advisory from CISA or the FBI. Which means defenders are watching closely for indicators that may never fully surface publicly.
What system was actually hacked?
Internal surveillance and wiretap management platform
Multiple investigative reports describe the same target: a system used by the FBI to manage court-authorized surveillance activities.
That includes both traditional wiretaps and warrants issued under the Foreign Intelligence Surveillance Act (FISA).
According to reporting from CSO Online and others, the platform helps agents and analysts:
- Track the lifecycle of wiretap and FISA warrants
- Manage returns from legal process such as pen register or trap-and-trace data
- Coordinate surveillance operations across FBI field offices and partner agencies
Here’s the key point: the system is reportedly unclassified. But that label can be misleading.
Unclassified does not mean harmless. In many cases it simply means the information doesn’t meet formal classification thresholds even if the operational sensitivity is extremely high. That’s exactly the case here.
Data likely stored in the system
Based on congressional notifications and media summaries, the affected system likely contains several categories of sensitive information:
- Returns from legal process such as pen register or trap-and-trace metadata
- Personally identifiable information on individuals under investigation
- Information tied to domestic surveillance orders and directives
Security analysts believe the system may also contain:
- Lists of surveillance targets
- Warrant metadata such as case IDs and authorization dates
- Operational notes tied to investigative workflows
Even partial access to this data would be enormously valuable to a foreign intelligence service.
Because it doesn’t just reveal information about targets. It reveals how the FBI conducts investigations.
Why this FBI surveillance system hack is so serious
National security and operational damage
If attackers gained access to or exfiltrated data from the surveillance warrant system, the implications are significant.
An adversary could potentially:
- Identify individuals currently under surveillance
- Infer FBI investigative priorities
- Map relationships between federal investigations and partner agencies
- Reverse-engineer U.S. lawful intercept capabilities
That kind of intelligence can help foreign adversaries protect their own assets and evade future investigations.
This is the type of breach intelligence services dream about.
Civil liberties and legal risks
There’s another side to this story and it has nothing to do with espionage.
Because the compromised system touches court-authorized surveillance, the breach raises difficult legal questions.
Civil liberties advocates and defense attorneys are already asking:
- Were sealed warrant details accessed?
- Could surveillance evidence be challenged in court?
- Was sensitive communications data exposed outside legal channels?
If the integrity of surveillance records is questioned, it could affect active or past criminal cases.
And that’s the part many organizations underestimate when legal infrastructure gets compromised. This is not just a cybersecurity failure. It can become a courtroom problem.
Who is behind the FBI cybersecurity breach?
Early suspicion: China-linked hackers
Initial reporting from Reuters and other outlets points toward hackers linked to the Chinese government.
Officials reportedly believe the attack targeted an unclassified FBI system containing communications-related investigative data.
The FBI has not confirmed attribution, and Chinese officials have not publicly commented on the allegations.
That ambiguity is typical in nation-state investigations. But the broader strategic context makes the suspicion hard to ignore.
Strategic context: Salt Typhoon and lawful intercept campaigns
The FBI wiretap breach 2026 does not exist in isolation. Between 2023 and 2024, U.S. officials exposed a Chinese state-linked threat cluster known as Salt Typhoon, which compromised multiple telecom providers.
Those intrusions targeted lawful intercept infrastructure the same systems telecoms use to comply with legal surveillance orders.
According to public reports, those operations exposed:
- Call detail records and communications metadata
- Lawful intercept data streams
- Traffic linked to political and government targets
Notice the pattern. Instead of hacking individual devices, attackers are increasingly targeting the infrastructure that manages surveillance itself.
And that shift has huge implications for both intelligence and privacy.
How the breach was detected and contained
Detection via abnormal logging and vendor path
Reports citing internal notifications say investigators detected the breach after abnormal log entries appeared on February 17, 2026.
Early analysis suggests attackers may have used a commercial ISP or third-party connectivity provider as a pathway into FBI systems.
If confirmed, that would align with a pattern seen across multiple advanced persistent threat campaigns.
Rather than attacking hardened government networks directly, attackers compromise:
- ISPs
- telecom providers
- managed service providers
Then quietly pivot into higher-value environments. It’s a technique that works disturbingly well.
Inter-agency response
Public statements suggest the breach triggered a coordinated federal response.
Agencies reportedly involved include:
- FBI cyber incident response teams
- The Department of Justice
- The National Security Agency
- The Cybersecurity and Infrastructure Security Agency
- The White House national security staff
The FBI says it has identified and addressed the suspicious activity. But details remain scarce.
Were systems rebuilt? Segmented? Re-architected under a zero-trust model? For now, that part of the story remains behind classified doors.
What this means for defenders and CISOs
Government systems are not magically secure
One takeaway from the FBI wiretap breach 2026 should be obvious but it’s still widely misunderstood.
Government systems are not immune to compromise. Even infrastructure tied to surveillance warrants can be breached.
Security labels such as “law-enforcement sensitive” or “national security” offer no technical protection by themselves. And yet many organizations still treat those labels as if they do.
Zero trust for surveillance and legal-process systems
Security leaders reviewing this incident are highlighting several practical lessons:
- Treat surveillance and legal-process systems as Tier-0 assets
- Do not assume “unclassified” means low risk
- Harden third-party connectivity paths aggressively
More broadly, organizations handling legal process or investigative workflows should consider implementing:
- aggressive network segmentation
- hardware-backed MFA for privileged access
- behavioral monitoring for sensitive record access
- long-retention logging capable of detecting stealth intrusions
Because attackers increasingly target legal-process infrastructure itself. Not just the data flowing through it. And that trend isn’t slowing down.
FAQ: FBI wiretap system tapped by hackers
What is the FBI wiretap breach 2026?
The FBI wiretap breach 2026 refers to a cyber incident discovered in February 2026 affecting internal systems used to manage surveillance and wiretap warrants.
Was the FBI surveillance system hacked for sure?
The FBI confirmed suspicious activity affecting systems tied to surveillance and wiretap management. Multiple media outlets describe the incident as a breach of a surveillance-management platform.
What data might be at risk?
The affected system reportedly stores surveillance data returns, personally identifiable information tied to investigations, and warrant-related metadata. Security analysts believe the platform may also contain operational notes and surveillance target lists.
Who is suspected of carrying out this FBI cybersecurity breach?
U.S. officials suspect hackers linked to China, though no official attribution has been publicly announced.
How serious is this compared to other government breaches?
Unlike previous FBI incidents involving email systems or local networks, this breach touches infrastructure tied directly to lawful surveillance operations.
That raises both national-security concerns and civil-liberties questions a rare combination that ensures the investigation will face intense scrutiny.

