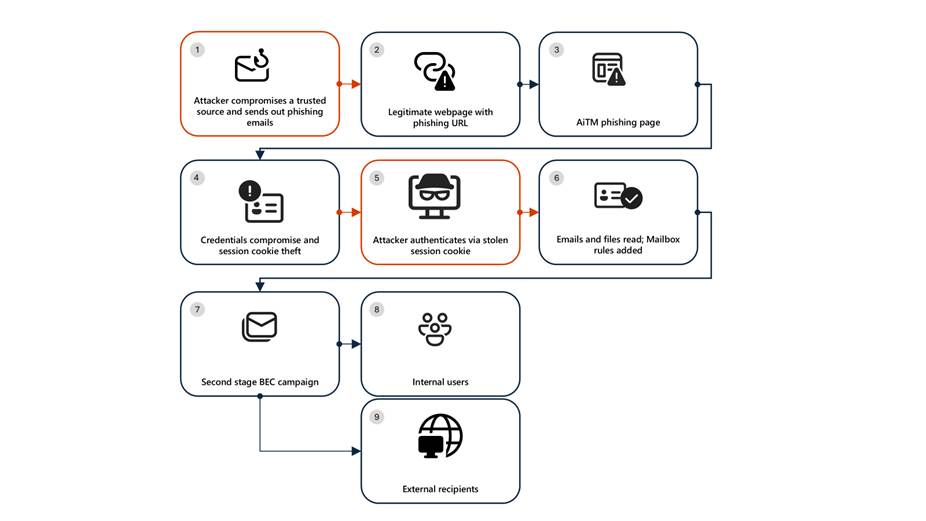
A recently uncovered AiTM phishing campaign shows how modern cyberattacks are increasingly designed to look and feel like routine business activity. According to researchers at Microsoft, threat actors deliberately abused familiar collaboration tools to gain access, remain unnoticed, and eventually turn compromised accounts into launchpads for large-scale fraud.
By misusing Microsoft SharePoint, attackers blended seamlessly into everyday workflows—making it extremely difficult for employees to tell the difference between legitimate work and a malicious operation.
Why This AiTM Phishing Campaign Worked So Well
This adversary-in-the-middle phishing attack did not rely on obvious red flags. Instead, it took advantage of habits employees have built over years of working in cloud environments.
People expect to:
- Receive SharePoint links
- Log into Microsoft 365 multiple times a day
- Collaborate with vendors and external partners
Attackers leaned into this familiarity. Victims were sent convincing emails containing SharePoint file links that appeared completely normal. When users clicked and logged in, the attackers quietly intercepted authenticated sessions using session cookie theft attacks, effectively pulling off MFA bypass phishing without the victim ever realizing something went wrong. From the user’s point of view, the document simply failed to load or appeared to open normally, while the attacker walked away with full access.
Trusted Vendor Email Compromise: Lowering Defenses Instantly
The campaign began with a trusted vendor email compromise, which made the initial phishing emails even more convincing. Messages came from real partner accounts, referenced genuine business processes, and included realistic context.
This is where Microsoft SharePoint abuse proved especially powerful. A SharePoint phishing attack does not feel like phishing at all it feels like work. Because SharePoint and OneDrive links are so common, they often bypass both automated security filters and human skepticism.
Once attackers gained access, they were inside Microsoft 365 environments with no malware, no exploit, and no immediate warning signs.
Staying Invisible with Inbox Rule Abuse
Rather than acting quickly and noisily, attackers focused on staying hidden. They used inbox rule abuse attacks to quietly clean up any signs of compromise deleting incoming messages, marking emails as read, and filtering out security alerts.
Victims continued their day-to-day work completely unaware. Meanwhile, attackers observed email conversations, learned communication patterns, and waited for the right moment to act. This slow, patient approach is becoming standard in identity-based cyberattacks, where stealth is more valuable than speed.
From Account Takeover to Business Email Compromise (BEC)
Once trust was fully established, the operation escalated into a widespread business email compromise (BEC) attack but at a much larger scale. In some cases, attackers sent more than 600 phishing emails from a single compromised account.
These were not generic messages. They were pulled from real email threads, making them highly believable. This is what makes a Microsoft 365 phishing campaign so dangerous: attackers are not guessing they are continuing real conversations.
When recipients questioned legitimacy, attackers responded directly from compromised accounts, reassured them, and then deleted the conversation to erase any trace. This level of interaction allowed the enterprise phishing campaign to spread quietly across organizations and partners.
Why the Energy Sector Was a Prime Target
Microsoft Defender analysts found that many victims were part of energy sector cyberattacks, a space where collaboration with vendors and contractors is constant. These trusted relationships gave attackers an ideal environment to move laterally from one organization to another.
Once a single account was compromised, existing trust did the rest. No exploits were needed—only access, patience, and social engineering.
The Hard Truth: Password Resets Are Not Enough
One of the most important lessons from this campaign is that password resets alone do not stop AiTM attacks. Because attackers steal active sessions, they can remain logged in even after credentials are changed. Some even went further by modifying MFA settings to maintain access.
Effective remediation requires revoking sessions, removing malicious inbox rules, and auditing identity settings in Azure Active Directory (Microsoft Entra ID).
Detection, Defense, and Reality Check
Microsoft recommends layered identity defenses supported by Microsoft Defender XDR, including conditional access policies, continuous access evaluation, and active monitoring for suspicious sign-ins and mailbox changes insights drawn directly from Microsoft Defender threat research. These controls are no longer optional. They are essential.
Indicators of Compromise
Security teams should immediately investigate authentication activity tied to the following attacker infrastructure:
- 178.130.46.8
- 193.36.221.10
Any related sign-ins should be treated as high-risk.
Final Thoughts
This AiTM phishing campaign highlights a simple but uncomfortable reality: today’s most effective attacks look ordinary. By turning trusted platforms like SharePoint into attack vectors, threat actors are exploiting not just technology, but routine human behavior.
As cloud-based phishing attacks continue to grow, organizations must move beyond assuming that familiar tools are safe by default. Continuous identity monitoring, rapid session revocation, and user awareness are now critical not just for preventing breaches, but for noticing when one is already underway.

