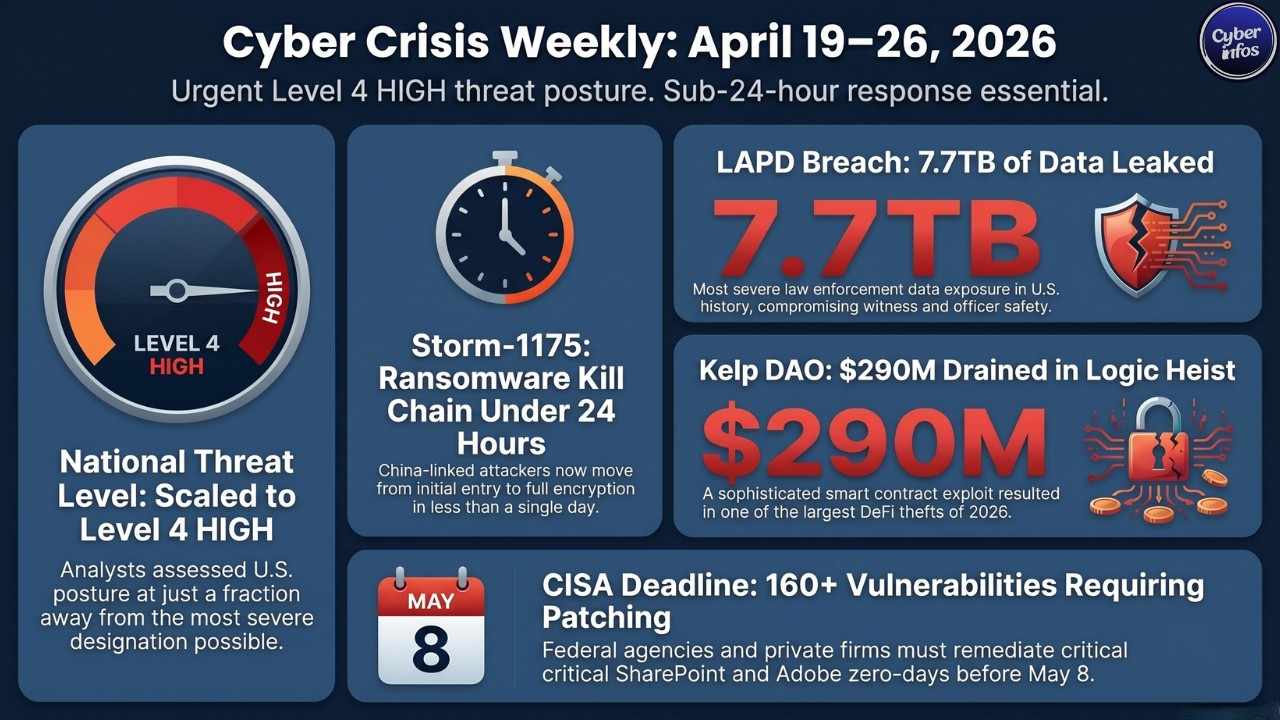
This week in cybersecurity April 19 to 26, 2026 was one of the busiest and most alarming stretches we have seen all year. Three major storylines dominated the threat landscape and each one carries serious implications for how organizations think about security in the months ahead.
First, a staggering 7.7 terabytes of sensitive law enforcement data leaked from the Los Angeles Police Department, exposing everything from officer personnel files to witness identities. Second, CISA went into overdrive, adding more than a dozen vulnerabilities to its Known Exploited Vulnerabilities catalog across two separate updates with federal agencies handed a hard May 8 deadline to patch. Third, ransomware groups showed no signs of slowing down, with the China-linked Storm-1175 group demonstrating a terrifying sub-24-hour kill chain that leaves defenders almost no time to react.
Underneath all of this, a $290 million DeFi heist, a poisoned npm package, and 108 malicious Chrome extensions reminded every security team that attackers are coming from every direction at once. MalwCon threat analysts assessed the U.S. threat posture at Level 4 HIGH this week just a fraction away from the most severe designation possible.
Major Incidents in Cybersecurity Weekly Report
1. Los Angeles Police Department – Government / Law Enforcement
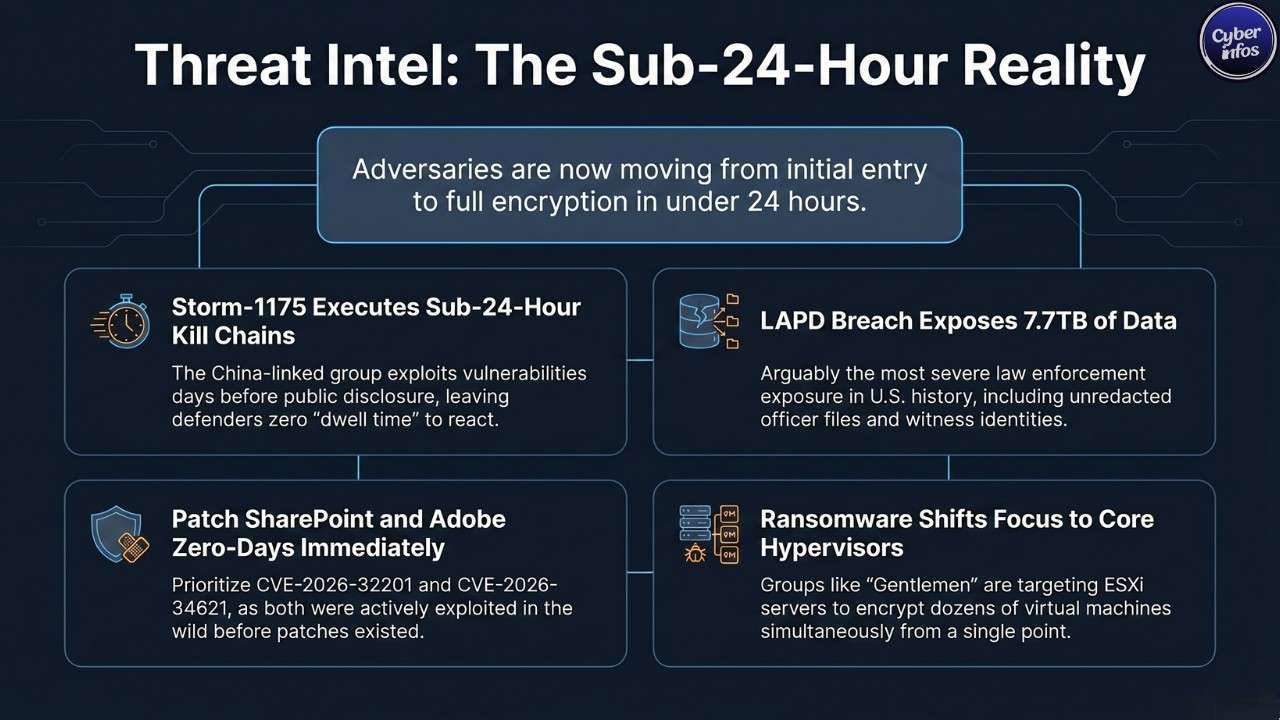
The LAPD breach is the kind of incident that keeps CISOs awake at night. Hackers broke into the Los Angeles Police Department and the L.A. City Attorney’s office and walked away with 7.7 terabytes of data making this arguably the most severe law enforcement data exposure in U.S. history. The stolen files were not generic records. They included unredacted officer personnel files, Internal Affairs investigation documents, active criminal case materials, witness statements, and protected medical information. Every one of those categories carries strict confidentiality obligations under California law.
By the time the breach was discovered, the data had already been distributed across online forums. The LAPD confirmed it has launched an active investigation, but no threat actor has been formally named. Beyond the legal and regulatory fallout, the exposure of witness identities creates a direct public safety crisis active criminal proceedings could be compromised, and individuals who cooperated with law enforcement are now potentially at risk. [Read more]
2. Mcgraw Hill – Education / Publishing
McGraw Hill confirmed this week that an unauthorized party accessed its internal systems. The educational publishing giant serves millions of students and educators through digital learning platforms, which means the breach likely touched a significant volume of personally identifiable information academic records, payment data, and institutional login credentials among them. The full scope of the compromise had not been determined by week’s end. McGraw Hill engaged external forensic investigators immediately and began its notification process, but the incident is a sharp reminder that ed-tech platforms are storing data at a scale that makes them attractive targets.[Read more]
3. Kelp Dao – Decentralized Finance / Cryptocurrency
Attackers drained approximately $290 million from the Kelp DAO decentralized finance protocol this week in what is shaping up to be one of the largest DeFi heists of 2026. Rather than attacking a traditional application layer, the hackers exploited a logic vulnerability buried inside Kelp DAO’s smart contracts the kind of flaw that requires deep protocol knowledge to find and weaponize. Kelp DAO suspended all protocol operations as soon as the theft was detected. On-chain forensics teams are tracing the stolen funds, but realistic recovery prospects are slim. In DeFi exploits, attackers routinely launder assets through cross-chain bridges and cryptocurrency mixers within minutes of theft.[Read more]
4. npm Supply Chain Attack – Open Source / Developer Ecosystem
On April 22, a malicious npm package appeared in the public registry and spent only a few hours live but that was enough. Anyone who installed it during that window handed over their GitHub tokens, SSH keys, environment variables, cloud credentials, and even their shell history. The package encrypted everything it harvested and shipped it off to attacker-controlled servers. In some cases, stolen tokens were immediately used to pivot into connected repositories and cloud environments, amplifying the damage far beyond the initial installation.
The package was detected and removed quickly, but the brief exposure window was sufficient to compromise an unknown number of developer environments. This is a textbook typosquatting or dependency confusion attack and it keeps working because developers move fast and trust their package managers.[Read more]
5. Trizetto Provider Solutions – Health Technology
Health technology company TriZetto Provider Solutions disclosed a breach affecting approximately 3.4 million individuals. TriZetto sits at the center of the healthcare payment ecosystem, processing insurance claims and provider data for carriers and hospitals across the country. That position makes it an exceptionally high-value target. Protected health information, financial records, and provider credentials are all in play. The disclosure fits a disturbing pattern: healthcare and health-adjacent technology companies have been disproportionately targeted throughout 2026, and the trend shows no sign of reversing.[Read more]
ANALYST INSIGHT: Three of this week’s five major incidents TriZetto, McGraw Hill, and the LAPD involved organizations whose core function is aggregating sensitive data on behalf of others. Attackers know exactly where the densest concentrations of valuable data sit. Meanwhile, the npm supply chain attack signals that adversaries are increasingly moving upstream to compromise developer tools rather than finished products, because one poisoned package can reach thousands of environments through a single install command.
New Vulnerabilities & Patches
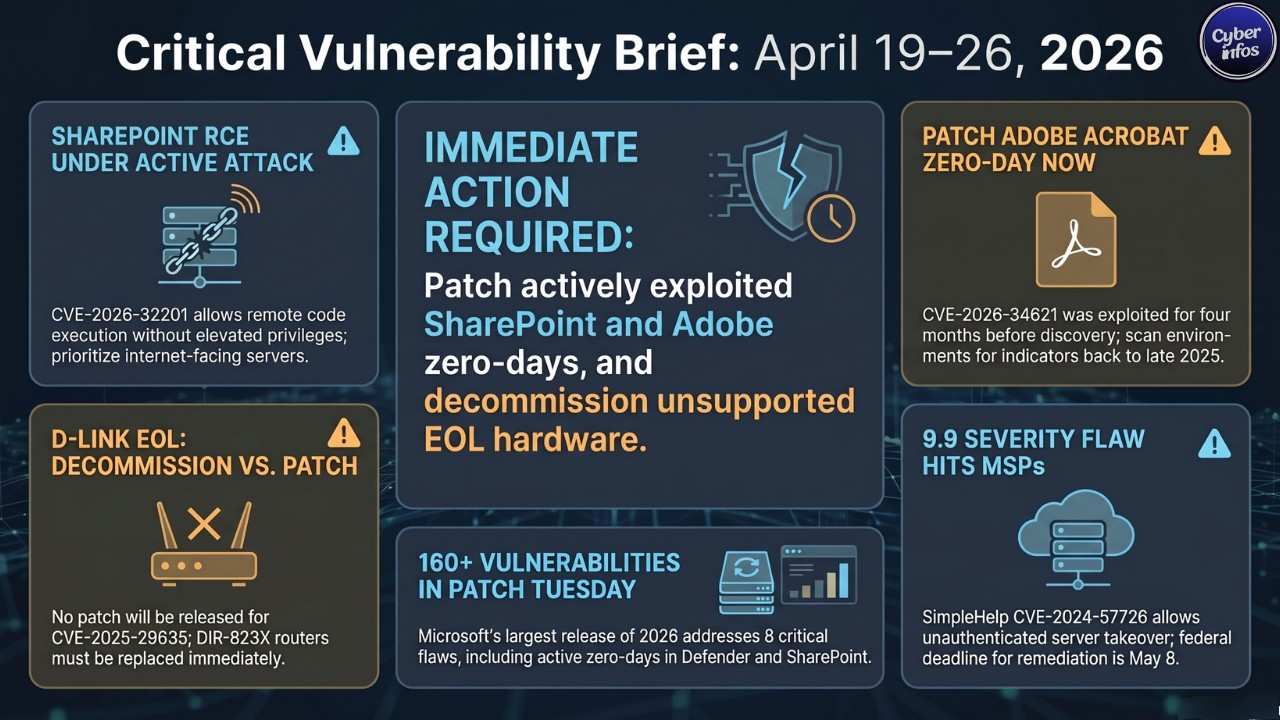
[CVE] CVE-2026-32201 | Microsoft | SharePoint Server | CVSS: Critical | Exploited: Yes
Attackers were already exploiting this remote code execution vulnerability in Microsoft SharePoint before Microsoft had a patch ready. The flaw allows an attacker to execute arbitrary code on a target server without needing elevated victim privileges a low-friction, high-damage capability. CISA confirmed active exploitation and added the CVE to its KEV catalog. SharePoint environments exposed to the internet should be treated as actively under threat until patched.
[PATCH] Apply Microsoft’s April 2026 Patch Tuesday update without delay. Prioritize any SharePoint infrastructure with external network exposure.
[CVE] CVE-2026-33825 | Microsoft | Microsoft Defender | CVSS: 7.8 | Exploited: Yes
This elevation of privilege flaw in Microsoft Defender lets a low-privilege local attacker escalate all the way to SYSTEM-level access. The vulnerability stems from insufficient access control granularity (CWE-1220). What makes it especially dangerous is the combination of no required user interaction and low attack complexity automated exploitation at scale is entirely feasible. Exploitation in the wild was confirmed starting April 16.
[PATCH] Covered in the April 2026 Patch Tuesday rollup. Ensure Defender definitions are current and the full OS patch bundle is applied.
[CVE] CVE-2026-34621 | Adobe | Acrobat and Reader | CVSS: Critical | Exploited: Yes
This is the vulnerability that should worry every organization that handles PDF documents. A prototype pollution zero-day in Adobe Acrobat and Reader had been quietly exploited in the wild for at least four months before Adobe pushed an emergency out-of-band patch. Security researcher Haifei Li called it “a highly sophisticated, fingerprinting-style PDF exploit,” meaning attackers were using it selectively against high-value targets to fly under the radar for as long as possible. CISA responded by adding it to the KEV catalog immediately.
[PATCH] Apply Adobe’s emergency patch right now. Then go back and scan PDF processing environments for indicators of compromise stretching back to late 2025.
[CVE] CVE-2024-57726 | SimpleHelp | Remote Support Platform | CVSS: 9.9 | Exploited: Yes
[CVE] CVE-2024-57728 | SimpleHelp | Remote Support Platform | CVSS: High | Exploited: Yes
SimpleHelp is deeply embedded in managed service provider environments, which is exactly why these two vulnerabilities a missing authorization flaw and a path traversal flaw are so alarming. CVE-2024-57726’s CVSS score of 9.9 makes it the highest-severity newly catalogued vulnerability this week. CISA added both to the KEV catalog on April 24, with a hard May 8 federal remediation deadline. The missing authorization flaw alone could allow an unauthenticated attacker to take over a SimpleHelp server and, by extension, every client endpoint it manages.
[PATCH] MSPs must treat this as a Priority 1 patch. Audit every SimpleHelp deployment in your environment before May 8.
[CVE] CVE-2024-7399 | Samsung | MagicINFO 9 Server | CVSS: 8.8 | Exploited: Yes
A path traversal vulnerability in Samsung’s MagicINFO 9 digital signage management platform lets attackers write arbitrary files with system-level authority. MagicINFO servers are deployed across retail stores, hotels, hospitals, and enterprise campuses environments that rarely apply patches promptly. CISA confirmed active exploitation and added this to the April 24 KEV update.
[PATCH] Apply Samsung’s available patch immediately. Where possible, isolate MagicINFO servers so they cannot be reached directly from the internet.
[CVE] CVE-2025-29635 | D-Link | DIR-823X Router Series | CVSS: 7.5 | Exploited: Yes
A command injection vulnerability in D-Link’s DIR-823X router series allows an authenticated attacker to execute arbitrary commands remotely via a simple POST request. The brutal reality here is that D-Link has classified this device series as end-of-life which means no patch is coming, ever.
[PATCH] There is no patch. Decommission any DIR-823X units in your network immediately and replace them with supported hardware.
Microsoft April 2026 Patch Tuesday – Overview
Microsoft’s April 2026 Patch Tuesday is the largest monthly release of the year so far, addressing between 163 and 168 CVEs across Windows, Microsoft Office, Word, SharePoint, and Defender. The release included 8 Critical-rated flaws, one actively exploited zero-day (CVE-2026-32201), and one publicly disclosed zero-day (CVE-2026-33825). Critical Office and Word remote code execution flaws CVE-2026-32190, CVE-2026-33114, and CVE-2026-33115 carry CVSS scores of 8.4 and require no authentication, meaning they can be triggered simply by getting a target to open a specially crafted file. Security teams should not wait on these.
PRIORITY ACTION : Patch CVE-2026-32201 (SharePoint RCE) and CVE-2026-34621 (Adobe Acrobat zero-day) first. Both were exploited in the wild before patches were available, and both represent attack vectors document handling and server-side code execution that ransomware operators and nation-state actors rely on heavily during initial access phases.
Ransomware Activity
Storm-1175 And Medusa Ransomware – The Sub-24-hour Threat
Microsoft Threat Intelligence dropped a detailed profile of Storm-1175 this week, and the findings are alarming for any organization still measuring its patch cycle in weeks rather than hours. This China-linked ransomware-as-a-service operator routinely exploits zero-day vulnerabilities up to one week before they become public knowledge meaning defenders are already behind before the race even starts. Once Storm-1175 has initial access, the group moves from entry to full encryption in under 24 hours. There is no leisurely dwell time, no prolonged reconnaissance phase. The clock starts ticking the moment they get a foothold. Microsoft confirmed that Storm-1175 has been delivering Medusa ransomware payloads and was directly linked to weaponizing CVE-2023-21529 to achieve this.
Gentlemen Ransomware – Going After The Hypervisor
A newer group called Gentlemen ransomware made headlines this week by specifically targeting hypervisors. The strategic logic is straightforward and devastating: compromise one ESXi server and you can encrypt dozens of virtual machines simultaneously. For a hospital running virtualized clinical systems or a manufacturer running virtualized production controls, that means total operational shutdown from a single point of entry. Hypervisor targeting reflects a broader 2026 ransomware trend attackers are abandoning endpoint-by-endpoint approaches and going straight for the infrastructure that everything else depends on.
Where Ransomware Stands In 2026
The numbers tell an uncomfortable story. As of early March 2026, ransomware groups had already claimed 1,745 victims year-to-date a 31.7% increase over the same period in 2025. Qilin remained one of the most relentlessly active groups. No major ransomware-specific law enforcement arrests were confirmed during the April 19–26 window, though Operation PowerOFF’s dismantling of DDoS-for-hire infrastructure demonstrated that international enforcement coordination remains active and capable of striking criminal services infrastructure at scale.
Threat Intelligence
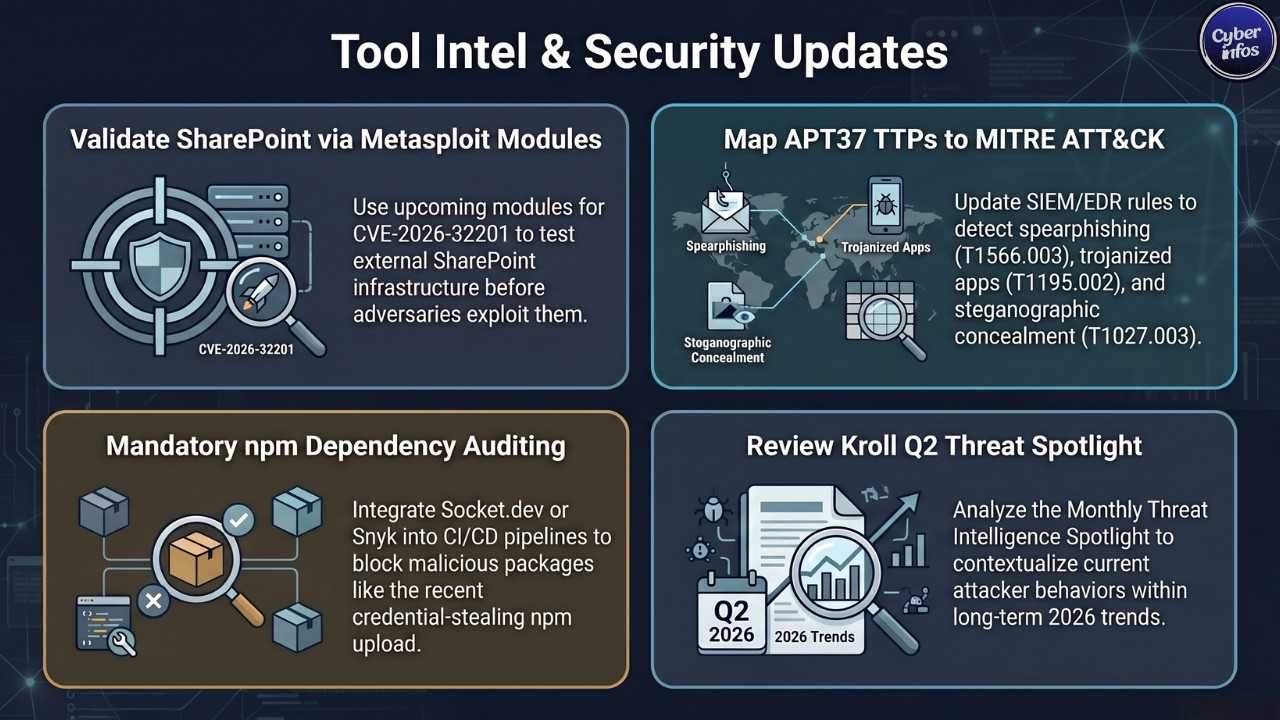
APT 37 (Scarcruft) – North Korea – Facebook And Telegram Weaponized
North Korea’s APT37, also known as ScarCruft, ran one of the most patient and methodical social engineering campaigns seen this week. The group created fake Facebook profiles “richardmichael0828” and “johnsonsophia0414” with listed locations of Pyongyang and Pyongsong. These accounts befriended targets, built rapport over time, and then steered conversations toward military weapons technology before pivoting to Telegram. Once on Telegram, targets were sent a trojanized version of the Wondershare PDF viewer installer a legitimate, trusted application that secretly installed the RokRAT remote access trojan. The malware itself was hidden inside a JPG image file using steganography, a technique designed specifically to slip past perimeter security tools that scan files by type rather than content.
- [TTP] Spearphishing via Social Networks (ATT&CK ID: T1566.003) – APT37 built fake social personas to initiate trusted relationships before delivering malware.
- [TTP] Supply Chain via Trojanized Application (ATT&CK ID: T1195.002) – The group modified a legitimate Wondershare PDF installer to carry RokRAT as a hidden payload.
- [TTP] Steganographic Payload Concealment (ATT&CK ID: T1027.003) – RokRAT was embedded inside a JPG image file, bypassing signature-based detection.
- [IOC] Domain |
cloudapi[.]stream| Malicious Chrome extension C2 infrastructure - [IOC] Facebook Account |
richardmichael0828| APT37 social engineering persona - [IOC] Facebook Account |
johnsonsophia0414| APT37 social engineering persona
108 Malicious Chrome Extensions – ONE Unified Command Center
Researchers uncovered a coordinated campaign this week deploying 108 malicious Google Chrome extensions all of them funneling stolen data back to a single command-and-control server at cloudapi[.]stream. The extensions were disguised as productivity tools, games, and browser utilities to attract organic installs. Once active, they harvested cookies, session tokens, and user identity data. The sheer number of extensions under unified infrastructure suggests a well-funded, operationally sophisticated threat actor who invested significant effort into building a sustained presence inside the Chrome Web Store.
[TTP] Browser Extension as Attack Vector (ATT&CK ID: T1176) – Adversaries published fake extensions to compromise browser sessions at scale.
Purerawt Malware – Hiding In Plain Sight
The PureRAT malware family resurfaced this week in a campaign that, like the APT37 operation, used steganography to conceal payloads inside image files. Once installed, PureRAT hands attackers a full suite of capabilities keylogging, screen capture, credential harvesting, and lateral movement support. Security tools that rely on file type scanning rather than behavioral analysis will miss this entirely.
Industry News
CISA Kev Updates – April 21 And April 24, 2026
CISA issued two significant KEV catalog updates in rapid succession this week. On April 21, the agency added eight actively exploited vulnerabilities affecting products from Cisco Catalyst, Samsung, Juniper ScreenOS, Jenkins, GNU Bash, and Smartbedded Meteobridge, including CVE-2023-27351 and CVE-2024-27199. Three days later, on April 24, CISA added four more: the two SimpleHelp flaws, Samsung MagicINFO 9, and the end-of-life D-Link DIR-823X router. Federal agencies were given until May 8, 2026 to remediate all four. For private-sector organizations that treat the KEV catalog as a patch prioritization guide which every security team should this week delivered an unusually heavy workload in a very short timeframe.
ServiceNow Acquires Armis For $7.75 Billion
ServiceNow announced this week that it is acquiring Armis, the asset intelligence and cybersecurity platform, in a deal worth $7.75 billion. This is one of the largest cybersecurity acquisitions of 2026 and a clear signal of where the enterprise security market is heading: toward unified platforms that combine AI-driven operations with comprehensive device visibility. For security teams already running both ServiceNow and Armis, the consolidation could simplify workflows significantly. For everyone else, it marks another step in a vendor consolidation trend that is reshaping the security tools market.
Operation Poweroff 53 Ddos-for-hire Sites Taken Down
The full impact of Operation PowerOFF a coordinated action involving 21 countries and backed by Europol continued to register this week. Authorities seized 53 DDoS-for-hire domains, arrested four suspects, executed 25 search warrants, and sent warning notifications to more than 75,000 individuals identified as criminal platform users. Seized databases held data on over 3 million criminal accounts. This is among the most sweeping anti-DDoS enforcement actions in years and a significant disruption to the booter-as-a-service ecosystem that enables low-skill actors to launch large-scale attacks for a few dollars.
Lovable AI Platform – API Vulnerability Disclosed
A serious API vulnerability in the Lovable AI website builder was disclosed this week, with researchers confirming that source code and user credentials were exposed through the flaw. Lovable sits in the fast-growing category of AI-powered application builders tools that let non-developers spin up working web applications in minutes. This disclosure highlights an uncomfortable truth about that sector: security controls have not kept pace with feature development. If your organization is using AI builder platforms in any production capacity, now is the time to audit their API exposure surfaces.
Tool Updates
Metasploit Framework
No major new Metasploit version was released specifically during the April 19–26 window. However, security teams should check Rapid7’s module release log closely over the coming days. New Metasploit modules targeting the SharePoint RCE (CVE-2026-32201) and the Office/Word remote code execution flaws from Patch Tuesday typically appear within days of public disclosure sometimes within hours. Any organization running penetration testing programs should validate their SharePoint environments before adversaries do.
Mitre Att&ck Framework
No formal ATT&CK framework version update was published this week. That said, the APT37 RokRAT campaign documented this week offers security teams a real-world opportunity to validate their detection coverage against three specific techniques: T1566.003 (spearphishing via social networks), T1195.002 (supply chain compromise via trojanized application), and T1027.003 (steganographic payload concealment). If your SIEM or EDR platform does not have detection rules covering these techniques, this week’s APT37 activity gives you the evidence to justify building them.
Kroll Threat Intelligence Spotlight
Kroll released its Monthly Threat Intelligence Spotlight Report this week, offering structured analysis of Q2 2026 threat trends. The report is paired with Kroll’s 2025 Cyber Threat Landscape retrospective and is recommended reading for threat intelligence analysts trying to contextualize this week’s activity within longer-term attacker behavioral patterns.
Open-source Security Tooling – npm Ecosystem Advisory
Following the April 22 malicious npm package incident, security teams running JavaScript or Node.js development pipelines should implement standing dependency auditing as a non-negotiable pipeline control. Tools including npm audit, Socket.dev, and Snyk can catch malicious or suspicious packages before they reach developer machines. Package provenance verification should be mandatory in all CI/CD workflows, not an optional step.
Looking Ahead
Three developments demand close attention in the coming week.
First, two unpatched Microsoft Defender zero-days internally tracked as RedSun (privilege escalation) and UnDefend (a denial-of-service flaw that blocks Defender from updating its own threat definitions) remained without available patches as of this report, with confirmed exploitation in the wild since April 16. Storm-1175 and affiliated RaaS operators are expected to incorporate these flaws heavily into ongoing campaigns. Every day without a patch is a day of active risk for every affected Windows environment.
Second, the Secure Boot certificate expiry deadline is now exactly 60 days away. Microsoft began rolling out the targeted certificate updates that address the upcoming expiry of the original 2011 Secure Boot certificates — set to expire June 26, 2026. Organizations that have not started their certificate migration planning could face boot failures on patched systems when the deadline hits. This is not a theoretical future problem; it is a 60-day countdown.
Third, Operation PowerOFF’s disruption of 53 DDoS-for-hire platforms will push displaced threat actors toward surviving infrastructure. Expect a short-term surge in DDoS activity as groups test and validate replacement platforms, particularly targeting financial services, gaming, and government sectors.
UPCOMING EVENTS: RSA Conference 2026 is on the near horizon. Expect a surge in vulnerability disclosures and research publications in the run-up researchers routinely time major findings to coincide with the industry’s highest-profile gathering.
[WATCH] : The two unpatched Microsoft Defender zero-days RedSun and UnDefend are the most dangerous unresolved situation entering the coming week. Exploitation has been active for over ten days. Storm-1175 has already proven it can move from initial access to full ransomware deployment in under 24 hours. For any organization running unpatched Windows endpoints with these flaws present, the question is not whether an attacker can exploit them it is whether your team will see it coming before the encryption starts.

