In 20 hours, attackers turned a newly disclosed flaw into a working exploit. That wasn’t the exception this week it was the pattern.
This cybersecurity weekly report tracks how multiple incidents from Stryker’s identity-driven wipe to Trivy’s CI/CD supply chain compromise exposed the same underlying failure: defenders are losing control of trust layers they rely on every day. You’ve patched systems, hardened endpoints, and locked down access. It still wasn’t enough. Because the attack surface shifted.
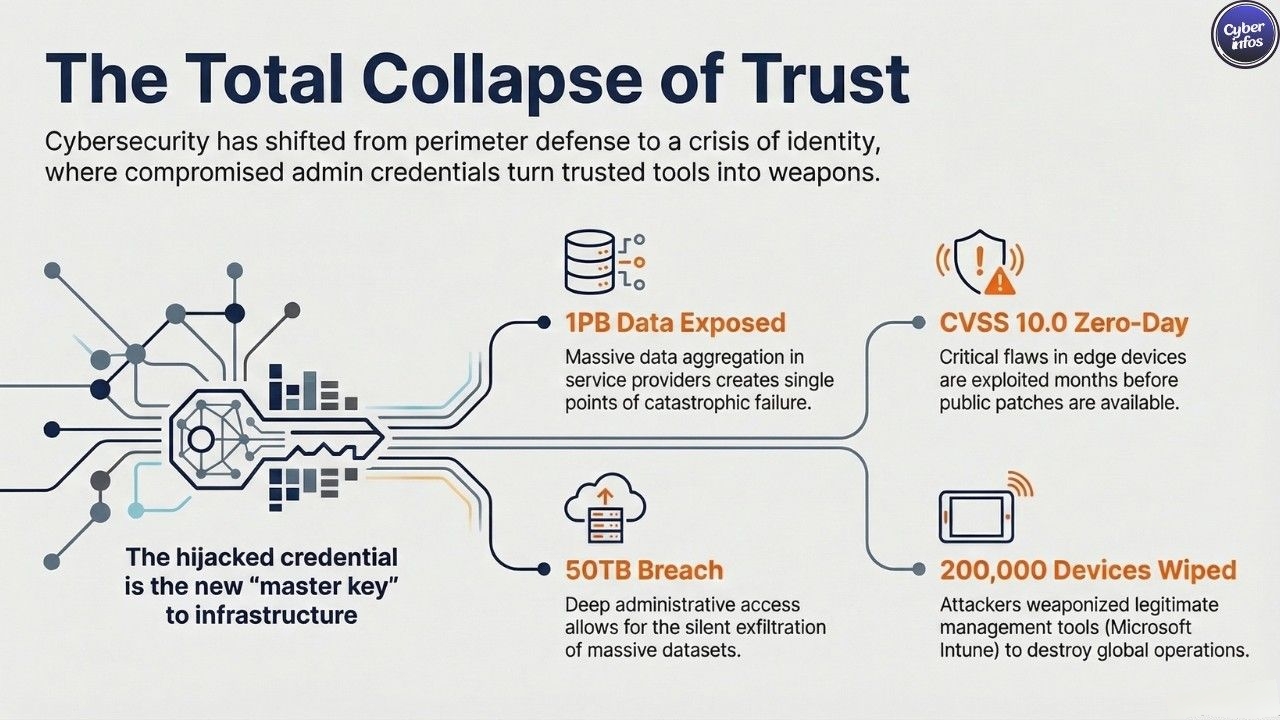
A single compromised admin credential, a poisoned version tag, or an exposed edge device now leads directly to operational disruption across healthcare, finance, and critical infrastructure where downtime translates into immediate financial and reputational damage. This week alone saw 1PB of data exposed and a CVSS 10.0 zero-day exploited before disclosure.
This report breaks down the real attack paths, the vulnerabilities already under active exploitation, and the tactical shifts redefining ransomware trends and supply chain attacks, so you can see where defenses are actually failing, and what needs to change next.
Major Incidents of this Cybersecurity Weekly Report
Stryker Corporation – Healthcare / Medical Technology
Week two, and Stryker still wasn’t stable. The company, a major supplier of surgical equipment, orthopedic implants, and neurotechnology, disclosed a cyberattack on March 11 that continued to disrupt operations globally.
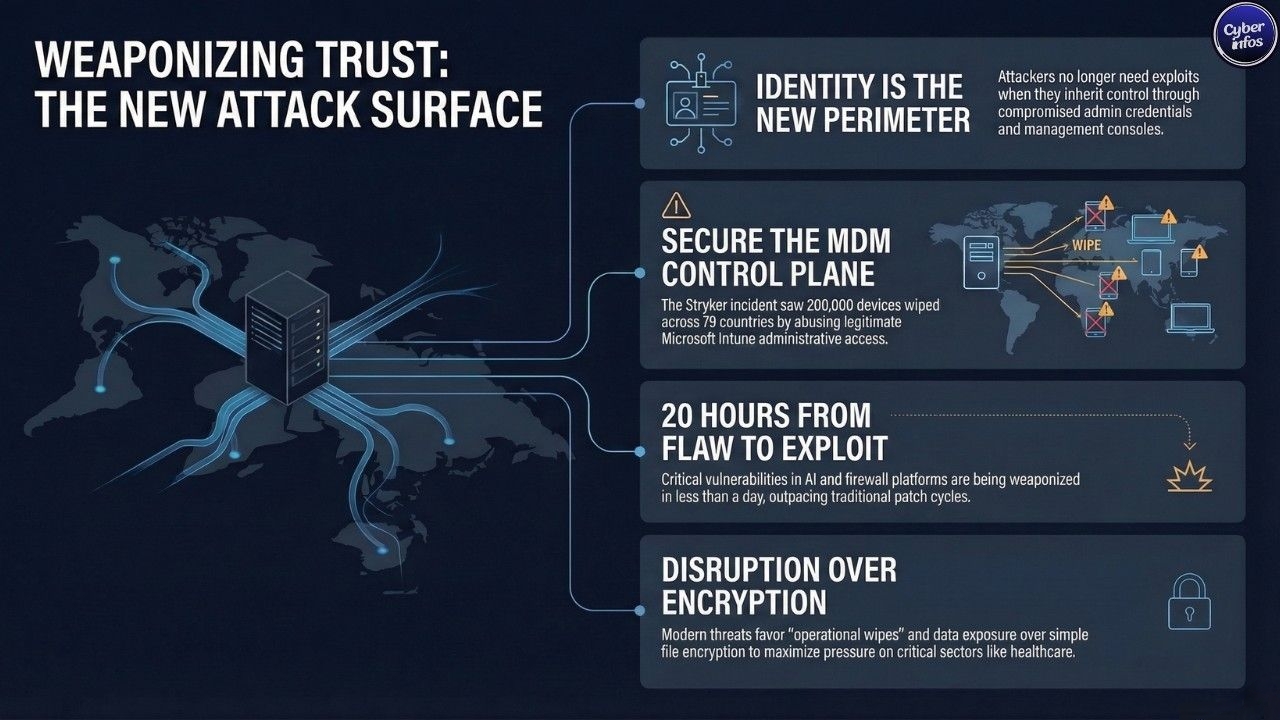
Handala also known as Void Manticore and Storm-0842, with links to Iran’s Ministry of Intelligence and Security claimed it wiped over 200,000 devices across 79 countries and exfiltrated 50TB of data. That scale sounds extreme. Even partially true, it suggests deep administrative access.
Stryker said the incident was limited to its Microsoft Windows environment, with no malware or ransomware found. That detail stood out. Researchers at Palo Alto Networks and Optiv believe attackers likely misused Microsoft Intune admin credentials, possibly sourced from infostealer logs, to remotely wipe devices using legitimate tools.
Operations took a hit. Ordering, manufacturing, and shipping systems struggled through March 22, while CISA and the FBI engaged directly. One credential was enough. Now the question is how many others are exposed.
Trivy-Open Source Scanner – Developer Security / CI/CD Supply Chain
Another breach, same weak point. Aqua Security’s Trivy open-source scanner was hit again, this time through its CI/CD integration layer.
Attackers force-pushed 75 of 76 version tags in the aquasecurity/trivy-action GitHub repository, which powers Trivy scans inside GitHub Actions pipelines. That move replaced trusted version references with malicious code. Quietly.
Each poisoned tag executed inside GitHub Actions runners, allowing attackers to extract API keys, tokens, and other credentials exposed during builds. No exploit required. Just automation doing its job.
Socket researcher Philipp Burckhardt linked the activity to a persistent attacker abusing version tags as a covert infostealer delivery channel embedded directly into developer workflows.
The exposure comes down to one habit. Teams that pinned Trivy to version tags instead of immutable commit hashes may have unknowingly executed attacker-controlled code.
Aqua Security acknowledged the issue and urged immediate audits of pipeline configurations. One shortcut caused this. Now every CI/CD pipeline using mutable tags needs a second look.
Telus Digital – Business Process Outsourcing / Technology Services
The numbers alone tell the story. TELUS Digital, a Canada-based BPO serving sectors from banking to healthcare, confirmed on March 11 that the ShinyHunterz ransomware group had breached its systems.
What surfaced was staggering. Around 1 petabyte of customer data including source code, FBI background checks, financial records, voice recordings, and Salesforce data was exposed, tying multiple industries to a single incident. That kind of concentration changes the stakes.
ShinyHunterz didn’t pick randomly. BPO providers like TELUS Digital aggregate sensitive data from dozens of companies, which means one intrusion can ripple outward fast, affecting organizations that never directly interacted with the attacker.
Recovery stretched through March 16–22, with teams still working to determine the full scope. That delay matters.
Berkaida – Financial Services / Commercial Real Estate
It showed up quietly. On March 20, 2026, ShinyHunters added Berkadia a commercial real estate finance firm handling mortgage banking, investment sales, and loan servicing to its growing list of victims.
There’s very little confirmed. No disclosed ransom demand, no verified data volume, and no public statement from Berkadia at the time of writing just a listing from a group known for turning stolen data into leverage. That silence stands out.
ShinyHunters typically operates on exposure, not encryption alone, using stolen datasets to pressure victims and extract payment. If Berkadia follows that pattern, the real issue isn’t system downtime it’s what data may already be in чуж hands and how it might be used.
Analyst Insight
The pattern is getting harder to dismiss. This week’s incidents all trace back to one entry point identity.
At Stryker, attackers likely used infostealer-derived credentials tied to Microsoft Intune. The Trivy breach flipped CI/CD tokens into an access mechanism, quietly embedding malicious code into trusted pipelines. TELUS Digital follows the same arc, where credential abuse appears to have enabled large-scale data access.
Different targets. Same failure point. This isn’t about firewalls or exposed services. It’s what happens after login when attacker-controlled credentials are accepted as legitimate inside admin consoles and orchestration systems.
That’s where things break. Platforms like Intune, WSUS, and CI/CD tooling assume trusted operators. Once those credentials are compromised, attackers don’t need exploits they inherit control.
That changes the risk model. Admin credential hygiene rotation, isolation, monitoring is no longer optional. It’s operational. Because when identity is compromised, the perimeter doesn’t matter anymore.
New Vulnerabilities & Patches
[CVE] CVE-2026-20131 | Cisco | Secure Firewall Management Center (FMC) / Security Cloud Control | CVSS: 10.0 | Exploited: Yes
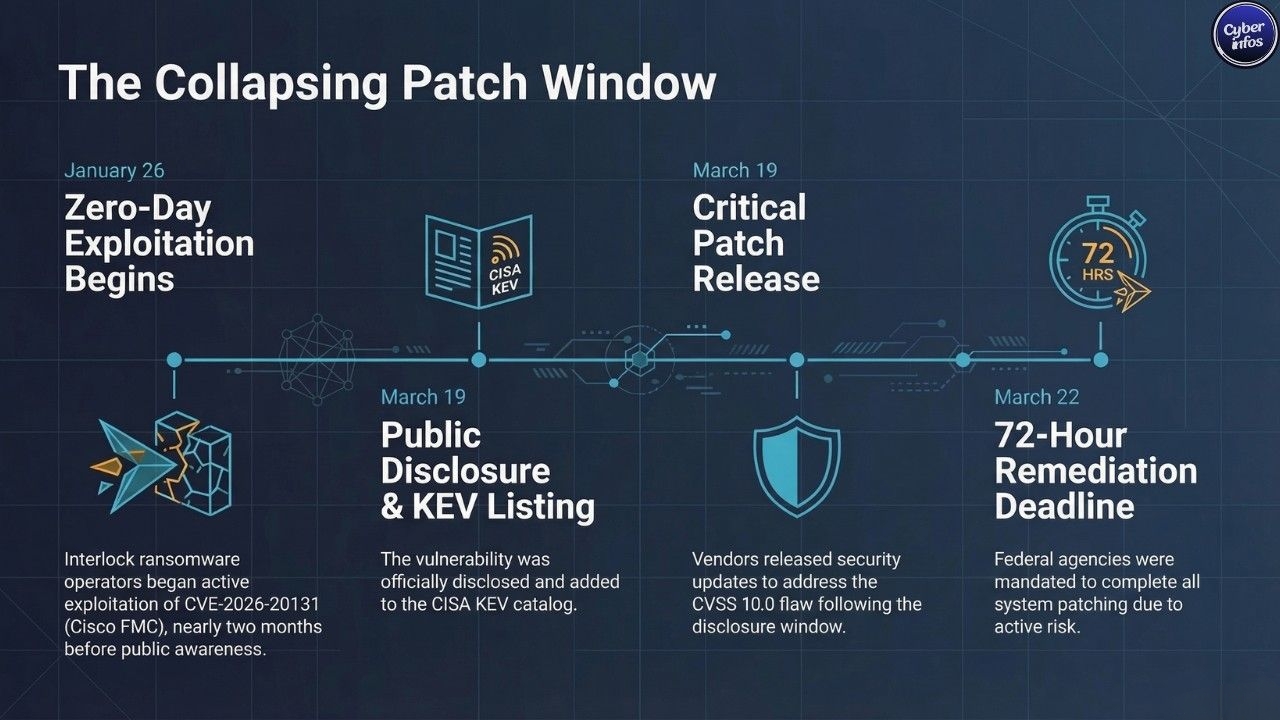 This one’s already been in play. Cisco FMC’s web interface improperly deserializes untrusted Java byte streams, allowing an unauthenticated remote attacker to execute arbitrary code as root no login, no user interaction, just direct access if the interface is reachable. That’s as bad as it gets.
This one’s already been in play. Cisco FMC’s web interface improperly deserializes untrusted Java byte streams, allowing an unauthenticated remote attacker to execute arbitrary code as root no login, no user interaction, just direct access if the interface is reachable. That’s as bad as it gets.
Amazon Threat Intelligence tracked Interlock ransomware operators exploiting this as a zero-day starting January 26, 2026, well before public disclosure. CISA added it to the KEV catalog on March 19, with federal remediation required by March 22. Patches are out, but any internet-exposed FMC instance remains a high-risk entry point.
[CVE] CVE-2026-33017 | Langflow | Langflow AI Platform | CVSS: 9.3 | Exploited: Yes
The flaw is almost blunt in its design. The /api/v1/build_public_tmp/{flow_id}/flow endpoint accepts attacker-controlled Python code and passes it straight into exec() no sandbox, no filtering, no guardrails. One request is enough.
Sysdig observed exploitation attempts within 20 hours of disclosure, even before a public proof-of-concept circulated. Attackers quickly moved to extract API keys for OpenAI, Anthropic, AWS, and connected databases — exactly where the value sits in AI pipelines.
Patch to version 1.9.0 or later immediately, lock down the exposed endpoint, and disable auto-login in production.
[CVE] CVE-2026-21992 | Oracle | Identity Manager / Web Services Manager | CVSS: 9.8 | Exploited: No (not yet confirmed)
Oracle’s out-of-cycle alert covers two Fusion Middleware issues, both remotely exploitable without authentication. CVE-2026-21992 allows full compromise of Oracle Identity Manager and Web Services Manager over HTTP.
No confirmed exploitation yet. That window won’t stay open long. Identity infrastructure is a high-value target, and flaws like this tend to move quickly once patch details circulate. Oracle is pushing for immediate updates.
[CVE] CVE-2026-21385 | Qualcomm / Google | Android (Qualcomm GPU components) | CVSS: Critical | Exploited: Yes
This zero-day was already active before Google’s March 2026 Android update part of a massive 129-CVE release, the largest in Android’s history.
It’s hardware-level exposure. The issue sits in Qualcomm GPU drivers, affecting most flagship Android devices. Until the March 5 security patch is applied, those devices remain exposed to in-the-wild exploitation.
Patch Tuesday – Microsoft, March 2026
Eighty-four CVEs this month. Eight critical. Among them, CVE-2026-26144 stands out an Excel information disclosure flaw that enables Copilot Agent data exfiltration without user interaction. Office bugs CVE-2026-26110 and CVE-2026-26113 allow remote code execution via the Preview Pane, while CVE-2026-26114 targets SharePoint.
No active exploitation reported at release. Still, these are the kinds of bugs that age badly if left unpatched. Microsoft also expanded hotpatching for Azure VM images, allowing updates without reboot useful, if actually used.
Atlassian – March 17, 2026
Atlassian’s monthly bulletin spans multiple products, including Confluence, Jira, and Bitbucket. Routine on paper.In practice, these platforms sit at the center of development and collaboration workflows, which makes delayed patching a recurring and avoidable risk.
Ransomware Activity
Interlock – Edge Device Exploitation at Scale
This is where things escalated. Interlock ransomware operators emerged as the most operationally significant threat this week, not because of volume, but because of how they got in. They didn’t wait for disclosure.
Amazon Threat Intelligence confirmed the group had been exploiting CVE-2026-20131 in Cisco FMC as a zero-day since January 26, 2026, quietly establishing access across education, engineering, construction, manufacturing, healthcare, and government environments sectors where downtime isn’t tolerated and pressure to pay builds fast.
That access wasn’t accidental. Using a CVSS 10.0 flaw months before a patch existed points to something deeper either access to pre-disclosure vulnerability intelligence or a supply chain of exploits that’s no longer limited to state-backed actors. That line is starting to blur.
ShinyHunters / ShinyHunterz – Multi-Sector Data Extortion
The activity didn’t slow elsewhere. ShinyHunters and its closely aligned variants, including ShinyHunterz, continued expanding a data-extortion-first model that favors exposure over encryption.
TELUS Digital and Berkadia both surfaced as victims this week.
No ransom demands were disclosed, which fits the pattern. These operations increasingly rely on controlled leaks, selective disclosure, and reputational pressure rather than immediate system disruption a quieter approach, but often just as effective. It’s less noise. More leverage.
Notable Leak Site Listings – March 20, 2026
The volume stayed steady. Multiple ransomware groups added fresh victims to leak sites, cutting across sectors and regions:
- Qilin: Accolend (lending); Enviaseo (government, Colombia)
- Akira: Angus-Young Group; Career Adventures
- DragonForce: HMS Group (engineering services, Australia); JustMercedes (automotive)
- INC_RANSOM: Namibia Airports Company
- Nitrogen: Enensys Technologies (broadcast technology, France)
That’s the point. The spread across industries and geographies reinforces a reality most organizations already know but rarely act on targeting is opportunistic, and exposure often comes down to who’s reachable, not who’s strategic.
DragonForce’s activity in Australian infrastructure adds another layer, especially given already elevated threat conditions in the region.
Tactical Shifts
The playbook is tightening. Double extortion still dominates, but the entry points are shifting away from phishing and toward infrastructure-level access MDM platforms, edge devices, and management interfaces that offer immediate control once breached.
Faster in. Faster impact. That compression matters. When attackers land directly inside administrative systems, the gap between initial access and operational disruption shrinks to hours, not days.
And by then, response teams are already behind. And in this sector, that matters.
Commercial real estate finance involves sensitive deal structures, borrower financials, and institutional investment data the kind of information that doesn’t need to be massive in volume to be damaging.
Threat Intelligence
Handala / Void Manticore (Iran-MOIS) – Critical Infrastructure, Healthcare, Western Corporates
Attribution firmed up this week. Handala also tracked as Storm-0842, Dune, Red Sandstorm, and Banished Kitten continues to operate as a “faketivist” front for Iran’s Ministry of Intelligence and Security, with confirmation from Check Point and IBM X-Force backing that assessment.
The shift in technique stands out. Push Security’s analysis shows the group likely moved away from its usual playbook VPN brute-force and wiper deployment and instead leaned on aged infostealer credentials to gain access. That’s a quieter entry point, and one that slips past controls tuned for noisier behavior.
Less effort. More access.
[TTP] Valid Accounts – Infostealer Credentials (T1078)
[TTP] Remote Services – Intune MDM Abuse (T1021)
[TTP] Data Destruction – Mass Device Reset (T1485)
Operation GhostMail – Russian State-Sponsored, Ukraine-Focused
This one relied on trust. Operation GhostMail targeted Ukraine’s State Hydrographic Service using CVE-2025-66376 in Zimbra, injecting obfuscated JavaScript into HTML emails sent from a compromised institutional account.
No obvious red flags. Victims who opened those emails exposed credentials, session tokens, 2FA backup codes, browser passwords, and months of mailbox data all quietly exfiltrated over DNS and HTTPS channels.
The campaign dates back to January 22, 2026, and has since pushed CISA to add the vulnerability to KEV.
[TTP] Spearphishing via trusted sender (T1566.001)
[TTP] Session/token harvesting (T1539)
Speagle Malware – Cyber Espionage / Financial Sector
This one hides in plain sight. Speagle, a newly observed infostealer, hijacks Cobra DocGuard infrastructure a legitimate document security platform to exfiltrate sensitive data while blending in with normal client-server traffic.
Detection becomes guesswork. Symantec and Carbon Black note the technique mirrors earlier abuse of the same platform in 2022, suggesting attackers are revisiting trusted software channels because they still work. And for defenders, that’s the problem.
Industry News
CISA Kev Catalog – Multiple Additions, March 16–20, 2026
Seven vulnerabilities were added in just days, including Cisco FMC’s CVSS 10.0 flaw, Apple WebKit-related issues, Chromium V8 bugs, Zimbra, and SharePoint deserialization RCE. Deadlines were tight.
Federal agencies had until March 22 for Cisco FMC and March 23 for SharePoint timelines that leave little room for delay, especially when exploitation is already confirmed.
CISA also pushed guidance around endpoint and MDM hardening following the Stryker incident.
XBow – $120 Million Series C Funding
Money is flowing toward automation. Xbow raised $120 million this week, betting that AI-driven penetration testing can keep pace with attackers who are already automating their own workflows.
That shift is telling. CEO Oege de Moor framed it plainly manual testing cycles can’t keep up with how fast attack surfaces are expanding.
Apple – WebKit Vulnerability Patched (March 2026)
Apple pushed fixes for a WebKit flaw enabling same-origin policy bypass across iOS and macOS. It sounds niche.
In practice, these bugs often sit early in exploit chains, giving attackers a foothold inside the browser before escalating further. CISA also flagged a related Apple buffer overflow in KEV this week.
FDA – GE Healthcare Centricity Medical Imaging Recall
This one crosses into patient safety. The FDA issued a recall for GE Healthcare Centricity imaging systems due to a vulnerability that could allow data manipulation or disrupt system availability. Not theoretical.
It lines up with broader concerns about connected medical devices and recent policy moves pushing for audits of foreign-manufactured systems in critical environments.
Tool Updates
TRIVY – Supply Chain Security Warning
After the March 20 compromise of Trivy’s GitHub Actions repositories, the guidance is direct: pin to commit hashes, audit pipeline activity, and rotate any exposed secrets.
Assume exposure. Version tags can’t be trusted if they can be rewritten and in this case, they were.
Microsoft – Azure VM Hotpatching (Generally Available)
Microsoft expanded hotpatching for Azure VMs, allowing security updates without rebooting supported Windows Server systems. Useful, if adopted.
It removes one of the most common excuses for delayed patching in production environments.
Nuclei Templates – CVE-2026-33017
Templates for the Langflow RCE appeared within hours of disclosure. No surprise there.
Even without official inclusion, community tooling is already scanning for exposed instances which means unpatched systems are likely being probed right now.
Atlassian – March Security Bulletin
Atlassian updated fixes across Confluence, Jira, and Bitbucket. Routine update.
But these platforms sit at the center of development workflows, which makes delayed patching a recurring and preventable risk.

