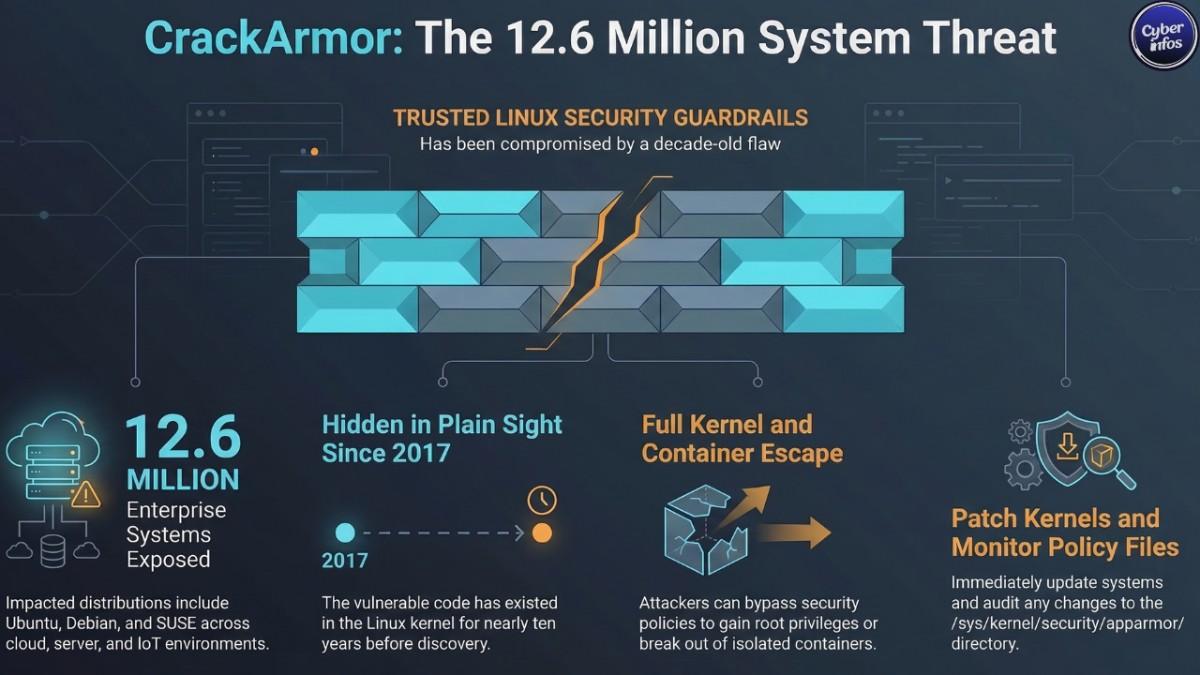
A newly disclosed CrackArmor AppArmor vulnerability is putting more than 12.6 million enterprise Linux systems at risk of Linux privilege escalation, container escape, and even full kernel-level compromise.
The issue surfaced during a deep technical review by researchers at the Qualys Threat Research Unit (TRU), who were examining how AppArmor operates inside the Linux kernel. What they uncovered wasn’t a single bug but a chain of weaknesses that allow unprivileged local users to escalate privileges to root by abusing how AppArmor processes certain security policy operations. And here’s the unsettling part.
According to the researchers, the vulnerable code dates back to Linux kernel version 4.11 released in 2017. That means the flaw may have quietly existed inside production environments for nearly a decade before anyone spotted it. Think about what that implies for organizations running long-lived infrastructure.
Because AppArmor is enabled by default in major Linux distributions including Ubuntu, Debian, and SUSE, the potential exposure spans enterprise servers, container environments, cloud workloads, and even embedded IoT deployments.
Security professionals already see the pattern here. Once reliable exploit techniques surface publicly, attackers rarely waste time. Privilege escalation bugs with this kind of reach tend to move from research papers to attack playbooks very quickly.
What Is the CrackArmor AppArmor Vulnerability?
The CrackArmor AppArmor vulnerability refers to a group of security flaws found within the AppArmor security module used across many Linux systems.
AppArmor functions as a mandatory access control (MAC) framework, enforcing strict rules about what applications and processes are allowed to access on a system. Instead of letting software interact freely with files and system resources, AppArmor applies security profiles that define exactly what each program can and cannot do.
In theory, this creates a strong containment boundary. Even if an application becomes compromised, the attacker should remain boxed inside the permissions defined by the AppArmor profile. But that’s where the trouble begins.
Researchers uncovered nine vulnerabilities inside the kernel-level implementation of AppArmor. Importantly, these issues stem from implementation mistakes rather than design flaws. The security model itself still holds up.
The code enforcing it, however, contains exploitable mistakes within the Linux kernel vulnerability chain affecting AppArmor.
Those weaknesses open the door for attackers to:
- Escalate privileges from a normal user to root
- Bypass AppArmor security policies
- Escape container environments
- Cause kernel crashes and denial-of-service attacks
- Potentially bypass kernel memory protections
Researchers collectively named this vulnerability chain “CrackArmor.”
The uncomfortable truth is that security mechanisms are only as strong as their implementation. And in this case, the guardrails themselves contain cracks.
How the CrackArmor AppArmor Vulnerability Attack Works
The attack begins with local access to a Linux system.
That might sound restrictive, but in real enterprise environments it’s surprisingly common.
Shared development servers, CI/CD build machines, container orchestration nodes, and internal testing environments often host multiple users simultaneously. If an attacker gains even limited access to one of these systems, the attack surface suddenly becomes very real.
At the center of the exploit lies a confused deputy vulnerability, a classic security flaw where an attacker tricks a privileged process into performing actions on their behalf.
Rather than directly modifying AppArmor policies which would normally require elevated privileges the attacker manipulates trusted programs such as sudo or other system services that legitimately interact with AppArmor.
Here’s where the mechanics come into play.
AppArmor policy operations rely on control files located within the Linux security filesystem:
/sys/kernel/security/apparmor/.load
/sys/kernel/security/apparmor/.replace
/sys/kernel/security/apparmor/.remove
These files are supposed to be accessed only by privileged system components responsible for loading and managing security policies.
But the vulnerability allows attackers to indirectly inject malicious policy data into these files by abusing trusted programs.
In practical terms, the attacker convinces a privileged tool to write policy data on their behalf effectively bypassing the normal permission checks.
Once those malicious policies load into the system, the attacker can weaken or completely remove the restrictions that AppArmor normally enforces.
And at that point, the security barrier protecting the system begins to collapse.
Kernel Exploitation and Linux Privilege Escalation
One of the most dangerous pieces of the CrackArmor vulnerability chain involves a use-after-free memory bug inside the Linux kernel.
Use-after-free vulnerabilities are a long-standing favorite among kernel exploit developers. The concept is simple but powerful: a program continues to reference memory that has already been released. That memory can then be reclaimed and manipulated.
In the CrackArmor case, the bug affects memory structures associated with AppArmor policy data structures.
The attack sequence unfolds roughly like this:
- The kernel frees memory associated with an AppArmor profile.
- The attacker rapidly reallocates that same memory region.
- Controlled data is written into the reclaimed memory.
- The kernel interprets the attacker-controlled data as legitimate internal structures.
From there, the attacker can manipulate kernel memory mappings and potentially overwrite critical system files.
The researchers demonstrated a striking example.
By exploiting the vulnerability, an attacker could overwrite /etc/passwd, modify the root account credentials, and immediately gain full administrative access to the system. Game over.
Once root access is obtained, the attacker effectively controls the entire machine files, processes, networking, everything.
This form of attack is a classic kernel privilege escalation scenario that security teams actively monitor for in enterprise Linux environments.
Which Linux Systems Are Affected by CrackArmor?
The vulnerability primarily impacts Linux systems where AppArmor is enabled by default.
Affected distributions include:
- Ubuntu
- Debian
- SUSE Linux Enterprise
These platforms rely heavily on AppArmor to enforce application isolation and system security policies.
Telemetry from Qualys asset monitoring systems suggests that more than 12.6 million enterprise Linux instances currently run with AppArmor enabled.
That’s a massive footprint.
The most exposed environments include:
- Enterprise Linux servers
- Kubernetes clusters
- Containerized workloads
- Cloud infrastructure
- DevOps build systems
- IoT deployments
Multi-user environments face the greatest risk.
Systems where developers, automation pipelines, or container workloads share access provide the foothold attackers need.
And once that foothold exists, privilege escalation can quickly follow.
Attackers may also leverage the weakness as a container escape vulnerability, potentially allowing compromised workloads to break out of container boundaries.
Why the CrackArmor AppArmor Vulnerability Matters
The CrackArmor discovery exposes a reality many security teams would rather not think about: even the defenses we trust most can contain hidden weaknesses.
For years, AppArmor has been viewed as a dependable tool for process isolation and application security across Linux environments.
It’s often baked directly into enterprise hardening guides and compliance frameworks. Which makes this discovery particularly uncomfortable. When vulnerabilities appear inside security frameworks themselves, the consequences ripple outward.
The protection layer becomes the attack surface. We’ve seen similar situations before.
The Dirty COW and Dirty Pipe vulnerabilities both allowed attackers to escalate privileges through subtle Linux kernel flaws. In both cases, the bugs lingered quietly for years before researchers uncovered them.
What’s striking about CrackArmor is its potential impact on containerized environments.
Many Kubernetes deployments rely on AppArmor policies to enforce container security policies and runtime isolation between workloads.
If those policies can be manipulated or disabled, attackers may be able to break out of container boundaries and reach the host system.
From there, lateral movement across infrastructure becomes possible.
Data theft, persistent malware, supply chain compromise the attack possibilities expand quickly.
How to Mitigate the CrackArmor Linux Kernel Vulnerability
1. Apply Security Updates
Linux vendors are already working on patches that address the vulnerabilities. Organizations should install the latest kernel and security updates provided by their distribution maintainers.
Kernel vulnerabilities rarely age well.
The longer systems remain unpatched, the more likely attackers will develop reliable exploits.
2. Monitor AppArmor Policy Changes
Administrators should monitor activity involving the AppArmor security directory:
/sys/kernel/security/apparmor/Unexpected changes to policy files such as .load, .replace, or .remove may indicate exploit attempts or malicious activity.
Security monitoring tools should flag unusual write operations within this directory.
Because under normal conditions, those changes should be rare.
3. Limit Local Access
Since the exploit requires local system access, reducing unnecessary user accounts significantly lowers the risk.
Shared infrastructure should enforce strict authentication controls, role separation, and monitoring.
Implementing least-privilege access policies ensures users only have the permissions absolutely required for their roles. Not more.
4. Audit Container Security Policies
Organizations running Kubernetes or container platforms should review the AppArmor profiles applied to their workloads.
Runtime monitoring tools can help identify suspicious behavior inside containers — especially actions that attempt to modify system-level security policies.
Container escapes rarely start loudly. They usually begin quietly.
5. Track Security Advisories
Security teams should closely monitor announcements from Linux distribution maintainers as CVE identifiers and patches are finalized.
Once proof-of-concept exploit code becomes public, the threat landscape can change quickly.
History suggests attackers move fast when Linux privilege escalation vulnerabilities emerge.
Timeline of the CrackArmor Discovery
- 2017 — Vulnerable code introduced in Linux kernel version 4.11
- 2017–2025 — Vulnerabilities remain undiscovered in production systems
- Early 2026 — Researchers at Qualys TRU identify multiple AppArmor flaws
- March 12, 2026 — Public disclosure of the CrackArmor vulnerabilities
- March 2026 — Linux vendors begin releasing patches and advisories
Conclusion
The CrackArmor AppArmor vulnerability stands out as one of the most consequential Linux security discoveries of 2026 so far.
With more than 12.6 million Linux systems potentially affected, the findings reinforce a core reality of cybersecurity: even mature, widely trusted security frameworks can hide critical flaws.
Organizations running Linux systems with AppArmor enabled should prioritize kernel updates, closely monitor security logs, and reevaluate access controls across shared infrastructure. Because once working exploit code enters the wild, attackers tend to move quickly.
And the real question isn’t whether someone will try to exploit the CrackArmor AppArmor vulnerability. It’s how many organizations will still be unpatched when they do.