Buying a cyber liability policy can feel like securing a reliable safety net, but it’s far from a guaranteed escape from financial fallout. Many business owners learn what cyber insurance doesn’t cover only after they submit a claim—when the denial hits. If you assume your policy automatically protects you from every type of digital threat, you’re likely exposing your company to risks that could cost millions. This guide breaks down the most overlooked exclusions and shows you exactly how to close the dangerous gaps in your coverage.
The Reality of Cyber Liability Insurance
The cyber insurance market is tightening quickly. With ransomware attacks growing more advanced and costly, insurers are narrowing what they’re willing to pay for. Policies now include more restrictive language designed to limit payouts.
If you want real protection, you must look past the premium and understand the fine print. Knowing how cyber insurance exclusions work is essential for managing risk. A typical policy will cover data breach response, legal fees, and notifications. However, the edge cases—the ones that often carry the steepest financial consequences—are the ones insurers frequently refuse to cover.
Top 7 Things That Cyber Insurance Doesn’t Cover
It’s crucial to understand the difference between a “cyber event” and a “covered loss.” Below are the most common—and most expensive—gaps found in standard cyber policies.
1. Social Engineering and Voluntary Transfers
This is easily one of the biggest and most painful surprises for businesses. While standard cyber policies cover hacking, meaning someone forces their way into your systems, the rules change when an employee is manipulated into sending money. If a staff member responds to a convincing phishing email and willingly wires funds to a scammer, the insurer may decline the claim.Because the employee technically authorized the transfer, many insurers categorize it as crime or fraud—not a cyber breach.
2. Intellectual Property (IP) Theft
If a hacker steals your customer database, your cyber insurance will typically cover notification costs and potential legal claims. But if they steal intellectual property—such as proprietary code, designs, or trade secrets—the financial loss tied to the value of that IP isn’t covered.
What cyber insurance doesn’t cover includes the long-term revenue you might lose once a competitor or attacker has access to your proprietary knowledge.
3. Prior Acts (The Retroactive Date)
Cyber policies are written on a “claims-made” basis. This means the policy must be active both when the incident occurred and when you file the claim. If a breach happened several years ago but is only discovered now—and your policy began after that breach—you’re not covered.
This limitation is tied to the “Retroactive Date,” an exclusion many businesses don’t realize applies until it’s too late.
4. Bodily Injury and Property Damage
Cyber-attacks can absolutely create physical consequences—like a hacked HVAC system overheating servers or a system outage that disrupts hospital operations. Standard cyber insurance, however, doesn’t cover physical harm.
If a cyber incident leads to injuries or property destruction, those costs typically fall under General Liability (CGL) coverage, not a cyber policy.
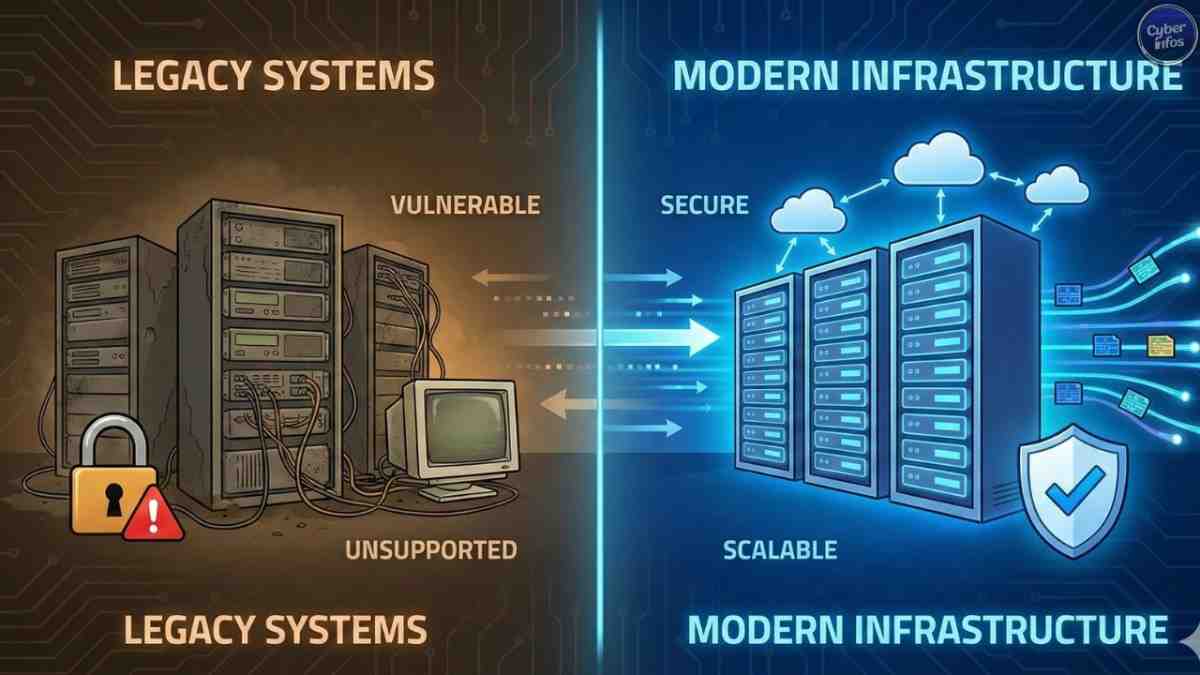
5. Failure to Maintain Security Standards
This is essentially a “negligence” exclusion. When you apply for cyber insurance, you agree to maintain certain security controls—such as Multi-Factor Authentication (MFA).
If a breach occurs and investigators find that your firewall was disabled or critical patches were ignored for months, the insurer can deny the claim. Their argument: you didn’t uphold the minimum security standards outlined in the contract.
6. Insider Threats and Intentional Acts
Cyber insurance is built to cover mistakes and external threats—not intentional sabotage. It generally excludes malicious acts committed by senior leaders or company directors. If a high-ranking executive deliberately leaks data or damages the network, the exclusion clause is triggered.
7. The Cost of Improvements (Betterment)
After a cyber-attack, it’s natural to want stronger, updated systems. The problem is that most policies only cover restoring your systems to how they were before the incident.
They won’t pay for upgrades, new hardware, or advanced security tools meant to improve your posture going forward. Those “betterments” must be self-funded.
Comparison: What IS Covered vs. What IS NOT
To make these gaps clearer, here’s a simple breakdown of standard coverage compared to common exclusions.
| Coverage Type | Typically Covered | Typically EXCLUDED (The Gaps) |
|---|---|---|
| Data Breach | Legal fees, notification letters, credit monitoring. | Loss of IP value, unencrypted portable device theft. |
| Financial Fraud | Hacking entry (Brute force attacks). | Social engineering (Voluntary wire transfers). |
| Ransomware | Ransom payment (sometimes), data recovery costs. | Payments made without insurer approval; government fines. |
| Hardware | Bricking (sometimes covered by endorsement). | Physical damage (fire, short circuits) caused by hacks. |
| Downtime | Business interruption income loss. | Future lost profits after the system is restored. |
How to Fix the Gaps and Secure Your Business
Understanding what cyber insurance doesn’t cover is only the first step. The next is closing those gaps through endorsements and disciplined security practices.
Buy Social Engineering Endorsements
Your base policy isn’t enough. Ask your broker specifically for a Social Engineering Fraud endorsement. This adds a dedicated sub-limit—typically $100,000 or $250,000—to cover losses where employees are deceived into sending money.
Align Your CGL and Cyber Policies
If a cyber-attack leads to bodily harm or property damage, you’ll need your General Liability policy to respond. Make sure it doesn’t include a “Cyber Exclusion.” Another option is a “contingent bodily injury” rider on your cyber policy to bridge digital and physical risks.
Adhere Strictly to Compliance
To avoid triggering the negligence exclusion:
- Implement Multi-Factor Authentication (MFA) everywhere.
- Maintain offline, immutable backups.
- Follow consistent patch management procedures.
- Document your security practices so you can prove compliance if needed.
Check Your “Retroactive Date”
When changing insurers, never allow your coverage to lapse. Ensure the new policy honors the original Retroactive Date so you remain protected against breaches that may have occurred long before you discovered them.

FAQ: Common Questions on Cyber Insurance Exclusions
1. Does cyber insurance cover ransomware payments?
It depends on the policy. Many do cover ransom payments, but only if the insurer approves the payment and it’s legal. What cyber insurance doesn’t cover are payments made without approval or those involving sanctioned entities.
2. Is theft of cryptocurrency covered by cyber insurance?
In most cases, no. Standard cyber policies treat cryptocurrency like cash. Unless you have a crime policy or a digital asset endorsement, crypto losses are excluded.
3. Does cyber insurance cover human error?
Sometimes. Accidental data deletion is typically covered. But falling for a phishing scam—social engineering—usually requires a specific rider before it’s covered.
4. What cyber insurance doesn’t cover regarding reputation?
Some policies may pay for a PR firm during a crisis, but they rarely cover long-term brand damage or future revenue loss tied to reputation decline.
5. Are government fines covered?
Coverage varies by region. In some jurisdictions, insuring government fines—such as GDPR penalties—is prohibited. Always review local laws and policy wording.
6. Does cyber insurance cover unencrypted laptops?
If an employee loses a laptop with sensitive data and the device wasn’t encrypted, the insurer may deny the claim for failing to meet security standards.
7. Why is “acts of war” an important exclusion?
Most policies exclude acts of war. Recently, insurers have attempted to classify certain state-sponsored cyber-attacks as acts of war to avoid paying claims. Look for policies that offer a “cyber-terrorism” exception.
Final thoughts
Cyber liability insurance is an essential part of modern risk management, but it’s not all-encompassing. The real danger comes from assuming you’re protected across the board and learning what cyber insurance doesn’t cover only after suffering a major loss.
To safeguard your organization, look beyond the basic quote. Study the exclusions carefully, secure the right endorsements—especially for social engineering—and maintain strong cybersecurity hygiene. Understanding the fine print allows you to transform potentially devastating exposures into manageable risks.
Primary Keyword:
What cyber insurance doesn’t cover
Secondary & LSI Keywords Used:
Cyber insurance exclusions
Cyber liability policy
Social engineering fraud endorsement
Ransomware payment coverage
Business interruption
Retroactive date exclusion
General Liability (CGL)
Intellectual Property theft
Cyber insurance gaps