Thirty-two years. That’s how long a remotely exploitable flaw sat in production code without anyone catching it.
The vulnerability now tracked as CVE-2026-32746 exposes a telnet buffer overflow buried deep inside GNU inetutils telnetd quietly inherited across systems you probably still trust. You’ve audited legacy services before, flagged Telnet as “low priority,” and moved on. That assumption is exactly what this bug exploits.
On affected systems, a single unauthenticated request can corrupt memory and potentially lead to pre-auth RCE, especially in environments still running legacy telnet daemon implementations tied to industrial or embedded infrastructure.
This breakdown walks through how the flaw actually works, why it has survived since 1994, and what detection and mitigation look like in real-world networks still carrying Telnet security risks.
What Is the CVE-2026-32746 Vulnerability in GNU inetutils telnetd?
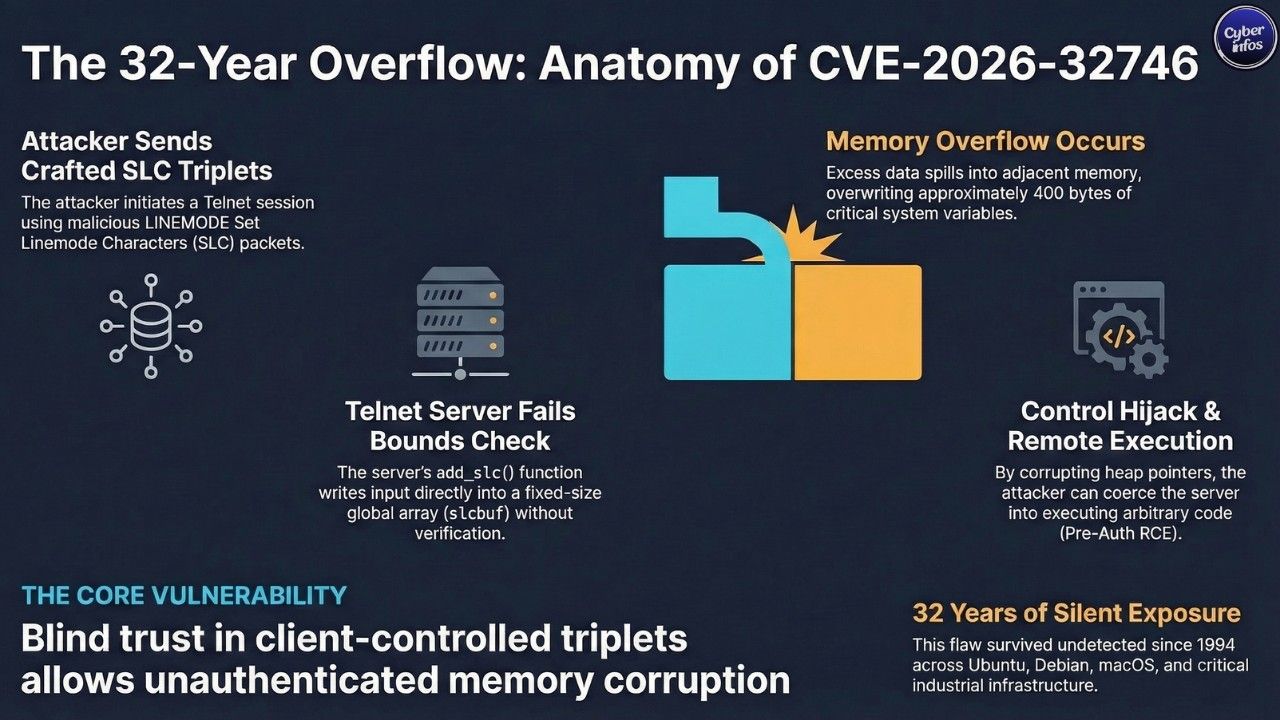
CVE-2026-32746 is a BSS-based buffer overflow vulnerability inside the LINEMODE SLC (Set Linemode Characters) negotiation handler in GNU inetutils telnetd. The mechanics are simple. A Telnet client sends a crafted sequence of Set Linemode Characters triplets, and the server dutifully writes them into a fixed-size global array no bounds checking, no resistance, just blind trust in client input. That trust breaks things.
An attacker can overwrite roughly 400 bytes of adjacent memory variables without authentication, opening the door to a BSS buffer overflow exploit that doesn’t require credentials, user interaction, or even subtlety.
The vulnerable logic lives in the add_slc() function, which accepts client-controlled triplets and writes directly into the global slcbuf array. The eventual fix? A single bounds check. It’s the kind of patch that makes you wonder how many similar landmines are still sitting untouched.
- Severity: High (CVSS score pending final NVD rating)
- Authentication Required: None, this is a pre-auth vulnerability.
- Attack Vector: Network
One missed check. Thirty-two years of exposure.
A Déjà Vu From 2005: Telnet buffer overflow vulnerability history
This isn’t new territory just the other half of it.
Back in 2005, a nearly identical flaw was identified on the Telnet client side and assigned CVE-2005-0469. That issue lived in the slc_add_reply function, which also lacked a bounds check. The patch was nearly identical to what’s now being applied to the server-side code.
The bigger issue? Nobody mirrored that scrutiny onto the server implementation for two decades. It’s not an exotic failure it’s a missed mirror check, and it lingered. History didn’t repeat itself exactly. It didn’t need to.
Which systems are affected by the CVE-2026-32746 telnet daemon vulnerability?
The reach here is broad. Uncomfortably broad. Because vendors historically reused or forked the same GNU inetutils telnetd code, this telnet daemon vulnerability propagates across multiple operating systems and embedded environments:
- inetutils-telnetd (official GNU package)
- Ubuntu (all supported releases)
- Debian (all releases except sid/forky)
- FreeBSD 13 and 15 Port
- NetBSD 10.1
- Citrix NetScaler
- Apple Mac Tahoe
- TrueNAS Core
- uCLinux
- libmtev
- DragonFly BSD
- Haiku
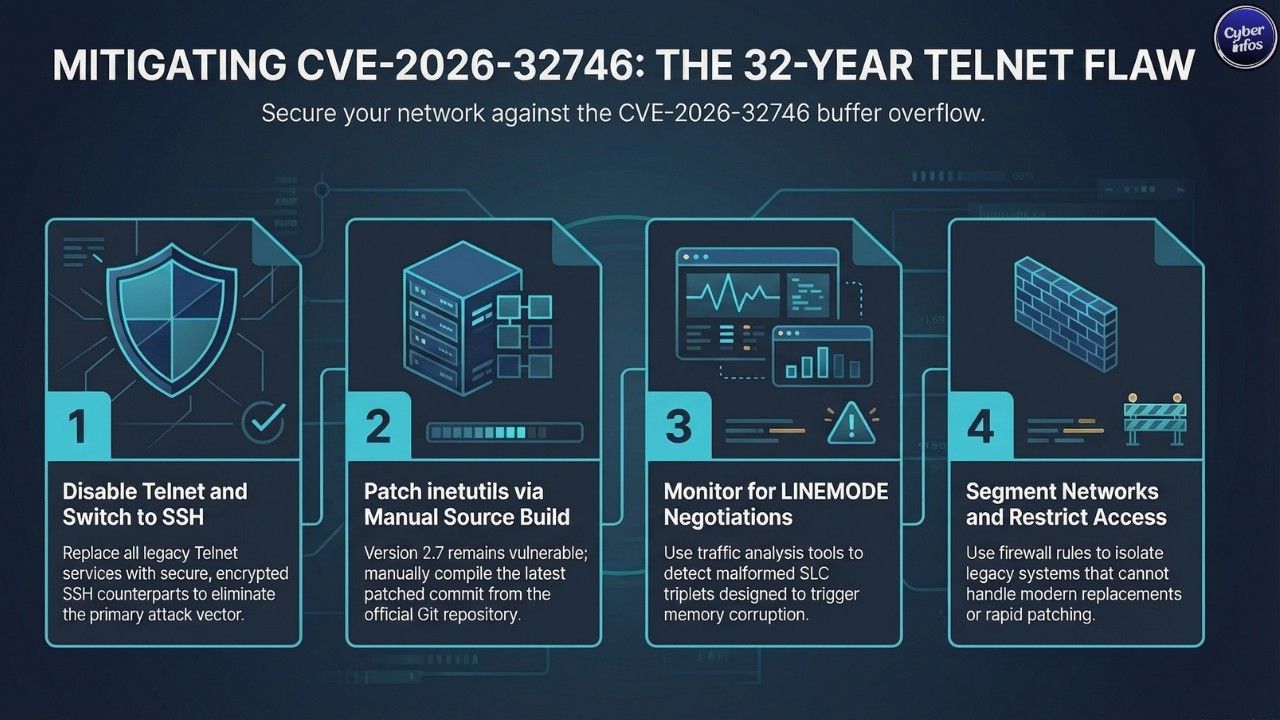
WatchTower researchers confirmed that, at publication time, no official patched release was available. The latest version inetutils 2.7 remains vulnerable, leaving users to manually pull a patched commit from the Git repository and compile it themselves.
That’s not a workflow most production teams love.
How Does the Attack Work in This Telnet Buffer Overflow CVE-2026-32746?
Buffer Overflow Entry Point in GNU inetutils telnetd
Telnet sessions begin with feature negotiation. It’s old protocol behavior but still active. One of those features LINEMODE allows the client to define how special characters map to control codes, sent as three-byte triplets.
Here’s where things go sideways.
A vulnerable server stores these triplets in a global buffer, slcbuf, sized at just 0x6C bytes.
There’s no enforcement. Send enough triplets, and the buffer spills over into adjacent memory, overwriting whatever sits next to it predictable, controllable, and dangerous.
It’s textbook overflow. Just hiding in legacy code.
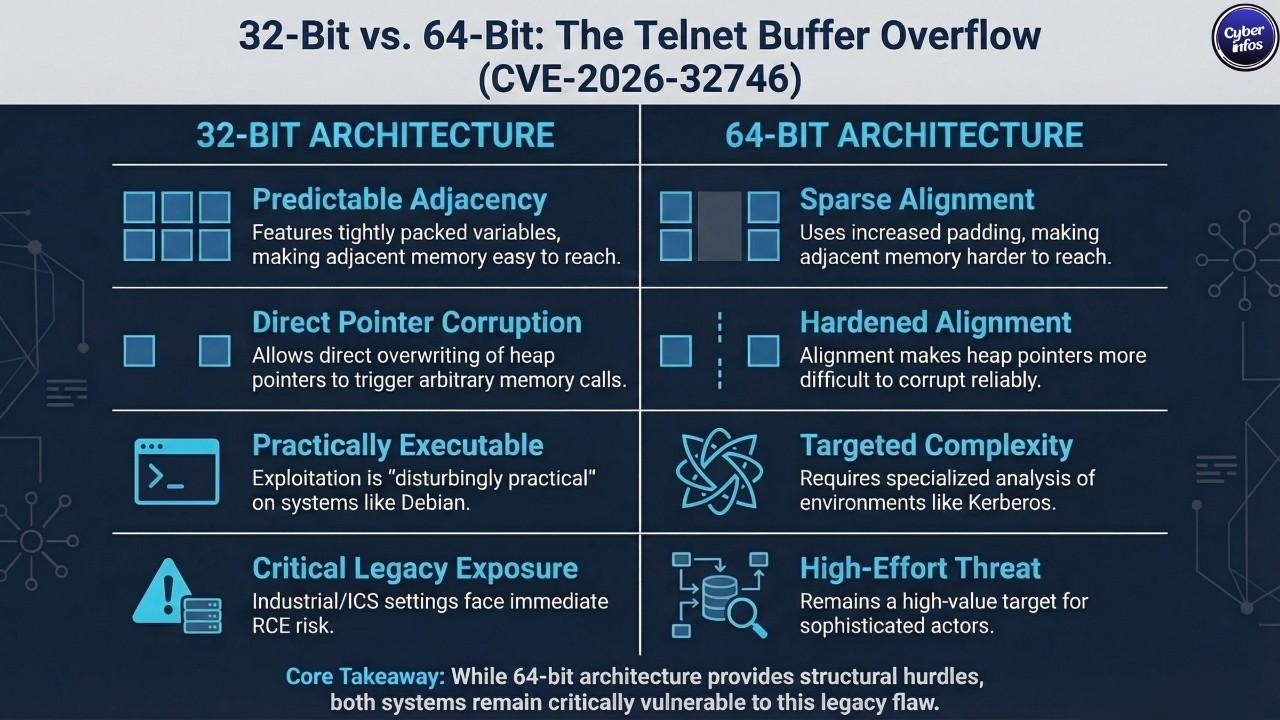
Exploitation on 32-bit vs. 64-bit in pre-auth RCE telnet 2026 scenarios
On 32-bit Debian systems, exploitation is disturbingly practical. Researchers observed that the adjacent variable def_slcbuf a heap pointer sits within the overwrite range. Corrupt that pointer, and the attacker can coerce the server into calling free() on an arbitrary memory location.
That’s not theoretical. That’s what primitive attackers actively look for.
From there, Remote Code Execution (RCE) becomes achievable under the right conditions, turning this into a credible pre-auth RCE telnet 2026 scenario.
On 64-bit x86 systems, the situation changes. Pointer alignment and memory layout make exploitation harder, but not impossible particularly in specialized deployments like Kerberos-backed Telnet environments, where assumptions about safety don’t always hold up under targeted analysis.
Harder doesn’t mean safe. It just means slower.
Why Is Telnet Still in Use despite Telnet Security Risks in 2026?
Because ripping it out isn’t trivial. Telnet persists in CNC machines, industrial control systems, legacy networking gear, and embedded environments that simply can’t handle modern replacements like SSH.
Replacing these systems isn’t just a software upgrade it’s operational downtime, capital expense, and sometimes full infrastructure redesign.
So they stay. Quietly. And that’s exactly where CVE-2026-32746 becomes dangerous the systems still running Telnet are often the least visible, least monitored, and least likely to receive rapid patches. Legacy doesn’t mean rare. It means neglected.
Can This Be Detected in the GNU inetutils telnetd Vulnerability CVE-2026-32746?
Yes, but detection comes with nuance.
WatchTower released a Detection Artifact Generator, a Python-based tool designed to probe Telnet servers for LINEMODE behavior. It sends carefully crafted SLC triplets that slightly exceed expected limits, then inspects how the server responds.
The distinction is subtle. A patched server discards the excess quietly. A vulnerable server echoes it back, effectively confirming that the overflow condition was accepted.
There’s also a safer mode. The tool can check for LINEMODE support without triggering overflow conditions, which matters when dealing with fragile industrial systems that don’t tolerate unexpected input well.
Because sometimes detection itself can cause downtime.
What Should You Do Right Now about the CVE-2026-32746 Telnet Buffer Overflow?
- Audit your environment – Identify any internal or externally exposed systems running a Telnet daemon.
- Disable Telnet where possible – replace with SSH wherever feasible.
- Patch from source – Build inetutils from a patched Git commit (not the 2.7 release)
- Monitor for LINEMODE negotiations – use detection tools proactively.
- Check vendor advisories – Watch Citrix, Apple, and FreeBSD updates.
- Apply network segmentation – Restrict access via firewall rules
None of these steps are novel. The problem is execution.
The Bigger Picture of CVE-2026-32746 and Legacy Telnet Vulnerabilities
A vulnerability introduced in 1994 remained undetected for 32 years.
That’s the headline but it’s not the real story.
CVE-2026-32746 exposes something less comfortable: widely reused legacy code can carry silent flaws across decades, surviving audits not because it’s secure, but because nobody looked closely enough. The client-side bug fixed in 2005 should have triggered a server-side review. It didn’t. And here we are.
The immediate threat isn’t mass exploitation tomorrow. Reliable exploitation still demands careful tailoring to specific systems, memory layouts, and configurations.
But for well-resourced attackers especially those targeting industrial environments or aging enterprise infrastructure this is exactly the kind of foothold worth investing in.
So the question isn’t whether Telnet is outdated. That’s already settled.
The real question is how many other 30-year-old assumptions are still running in production and who’s quietly counting on them?
📢 Stay Updated
Stay updated on the latest cybersecurity vulnerabilities and data breaches at CyberInfos your trusted source for real-time threat intelligence.

