In under 10 minutes, a leaked API key can be abused in the wild.
Teams already run scanners, enforce policies, and review code yet exposed credentials still slip through pipelines and land in production. Betterleaks secrets scanner targets the exact detection gaps that older tools consistently miss, especially in CI logs, encoded data, and large Git histories. The problem isn’t visibility. It’s accuracy and signal quality.
One exposed token is enough to trigger cloud abuse, lateral movement, and real financial damage often before anyone notices. According to IBM, breaches involving credentials cost over $4 million on average, and most start with something as simple as a leaked key in a repository.
This breakdown shows how the Betterleaks secrets scanner improves detection, where it outperforms legacy tools, and how to integrate it into your pipelines without adding noise so your secrets scanning actually works when it matters.
Why Secrets Scanning Matters
Developers continue to hard-code API keys, tokens, passwords, and private keys into repositories. These secrets rarely stay private once committed. Threat actors run automated scanners that continuously monitor public repositories and ingest newly exposed credentials within minutes. Attackers move faster than defenders.
Effective API key leak detection is no longer optional in modern pipelines.
According to Verizon, credential abuse remains one of the most common initial access vectors in breaches. IBM reports the average breach cost exceeds $4 million, with compromised credentials playing a major role in escalation and lateral movement.
From a SOC analyst perspective, exposed AWS access keys often lead directly to abuse mapped under MITRE ATT&CK T1078 (Valid Accounts). I have worked on incidents where attackers provisioned compute resources for crypto mining within hours of discovery. The logs existed. Nobody was watching them.
What threat intelligence consistently shows is that attackers prioritize speed. They do not need zero-days when valid credentials provide direct access to production systems. And that is exactly what attackers count on.
What Betterleaks Is
Betterleaks secrets scanner is a Go-based command-line tool designed to detect exposed secrets across Git repositories, local directories, files, and stdin streams. It builds on lessons learned from Gitleaks but introduces stronger filtering, improved validation, and faster scanning. It keeps the workflow familiar.
Unlike older scanners that rely heavily on entropy, the Betterleaks secrets scanner combines pattern matching with contextual validation. This improves API key leak detection while reducing both missed detections and false positives, which are the two problems that cause teams to ignore alerts. Detection quality is the difference.
Origin and Relationship to Gitleaks
Gitleaks became widely adopted across security teams, developers, and red teamers. It set the baseline for open-source secrets scanning. After losing full administrative control over that project, Zach Rice launched Betterleaks as a new initiative with fewer constraints and faster iteration.
This was about ownership and direction. The Betterleaks secrets scanner maintains compatibility with Gitleaks CLI commands and configuration formats. Most teams can migrate without rewriting pipelines, which lowers friction and speeds up adoption. It is an evolution, not a replacement.
Core Features
Multi-source scanning
The Betterleaks secrets scanner supports scanning across:
- Git repositories including commit history, branches, and tags
- Local directories and files
- Standard input streams
- Combined and piped workflows
This expands coverage significantly and strengthens CI/CD secrets scanning across environments.
In practice what I see is secrets leaking through CI/CD logs, temporary export files, and debug outputs more often than source code itself. Attackers monitor these areas because defenders rarely scan them consistently. Coverage gaps create exposure.
Rule-defined validation using CEL
Betterleaks uses Common Expression Language (CEL) for validation logic. This allows rules to evaluate context such as file paths, metadata, and match groups before flagging a finding.
Instead of relying on static regex patterns, the Betterleaks secrets scanner enables dynamic evaluation aligned with real-world API key leak detection scenarios. False positives drop quickly.
Token Efficiency Scanning
Betterleaks introduces Token Efficiency Scanning using BPE tokenization. This approach improves API key leak detection by distinguishing structured secrets from natural language. Entropy alone is not enough.
Betterleaks achieves approximately 98.6% recall on the CredData dataset, compared to around 70.4% for entropy-based methods. Detection improved. Noise reduced.
Automatic detection of encoded secrets
The Betterleaks secrets scanner detects doubly and triply encoded secrets automatically. Developers often encode values using base64 or similar methods, either intentionally or as part of tooling workflows.
This directly improves CI/CD secrets scanning, where encoded credentials frequently appear in logs and artifacts.
Pure Go implementation and performance
The Betterleaks secrets scanner is written entirely in Go without CGO dependencies. It supports parallel scanning, especially for Git repositories with large histories.
Faster scans improve adoption in CI/CD secrets scanning workflows where performance impacts enforcement.
Expanded rule sets and community contribution
Betterleaks includes expanded provider rules and supports community contributions through GitHub. Security teams can extend detection logic based on real-world findings.
This strengthens long-term credential leak prevention strategies.
Installation and Setup
Betterleaks is available through GitHub and package managers like Homebrew. Users can install it by downloading binaries, using package managers, or building from source.
Setup is straightforward. Running the betterleaks command without arguments confirms installation of the Betterleaks secrets scanner.
Configuration Model
Betterleaks loads configuration in the following order:
- Explicit –config flag
- Environment variables such as BETTERLEAKS_CONFIG
- Local configuration files like .betterleaks.toml
- Built-in default configuration
This allows flexible deployment of the Betterleaks secrets scanner across environments.
Precision matters here.
CLI Commands and Basic Usage
Scan a directory or file
betterleaks dir --path .
Scan a Git repository
betterleaks git --repo-url https://github.com/example/project.git
Scan from stdin
cat suspect-file.txt | betterleaks stdin
These workflows support automation and improve CI/CD secrets scanning coverage.
Integration with CI/CD Pipelines
The Betterleaks secrets scanner integrates directly into CI/CD workflows. Teams can scan pull requests, block merges, and enforce policies automatically.
This is where CI/CD secrets scanning becomes enforcement, not just visibility. Common integrations include GitHub Actions, GitLab CI, CircleCI, and Jenkins.
Comparison: Betterleaks vs. Gitleaks
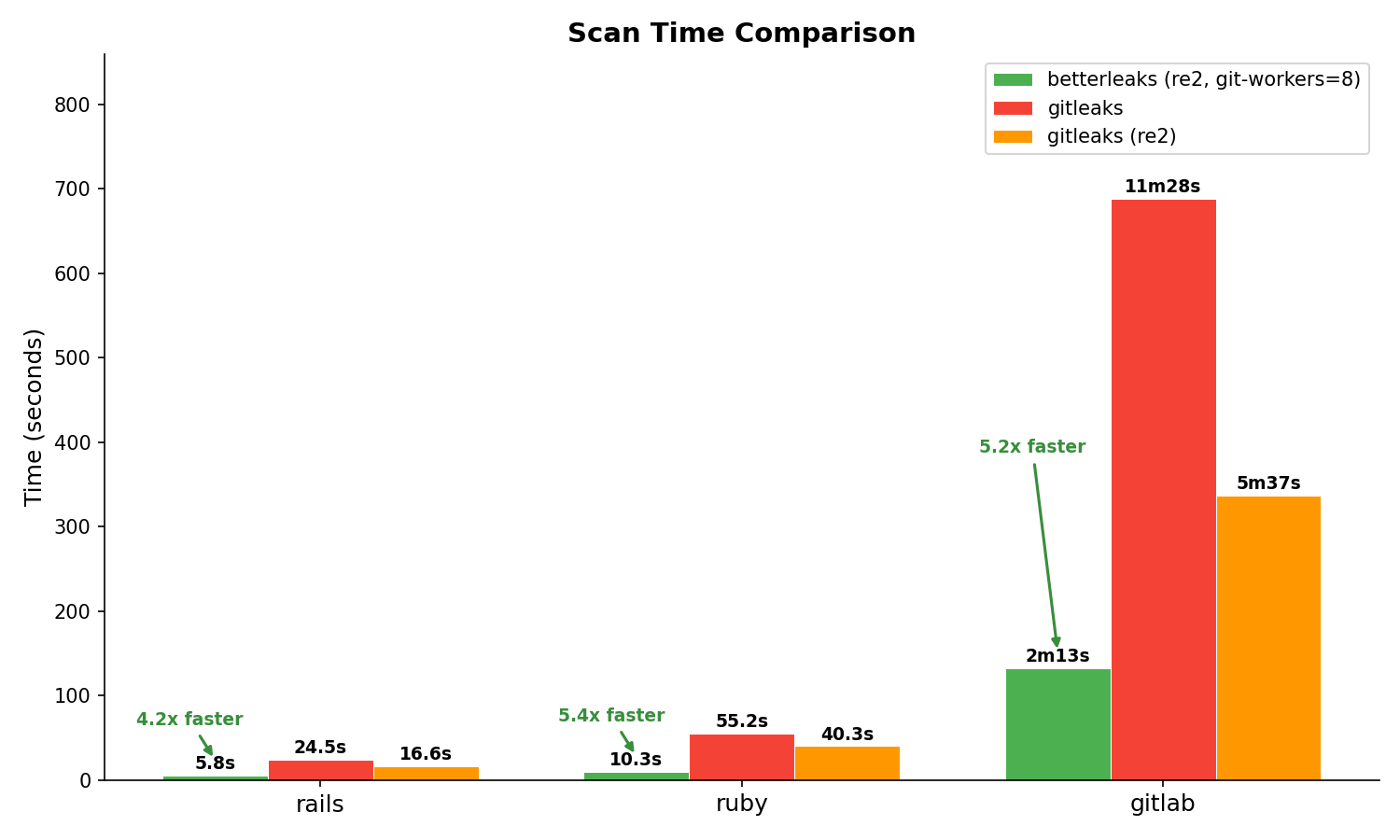
Betterleaks focuses on detection accuracy and performance improvements rather than workflow changes. In Betterleaks vs Gitleaks comparisons, the key difference is detection quality, not usability.
| Aspect | Gitleaks | Betterleaks |
|---|---|---|
| Origin & maintainer | Created by Zach Rice | New project by Zach Rice with Aikido sponsorship |
| License | MIT | MIT |
| Input sources | Git repos and files | Git, directories, files, stdin |
| Detection filtering | Entropy + regex | Token efficiency + CEL |
| Encoded secrets | Limited detection | Detects multi-encoded secrets |
| Performance | Variable | Faster with parallel scanning |
| Configuration | TOML rules | Extended TOML + CEL |
| Roadmap | Stable | Active development |
Practical Use Cases
The Betterleaks secrets scanner fits into several real-world scenarios:
- Scanning repositories before open-sourcing projects
- Preventing commits with secrets via pre-commit hooks
- Running scheduled scans across internal repositories
- Supporting bug bounty reconnaissance workflows
- Enabling AI-driven security analysis pipelines
Each supports stronger credential leak prevention.
Best Practices for Using Betterleaks
- Start with default rules and refine within two weeks
- Integrate into CI/CD pipelines immediately
- Define clear ownership for secret remediation
- Rotate credentials within hours of detection
- Combine with SAST and runtime monitoring
One question matters: who fixes the leak once it is found?
Final Thoughts
The Betterleaks secrets scanner improves API key leak detection, reduces false positives using CEL-based validation, and strengthens CI/CD secrets scanning with faster performance.
These improvements directly support modern credential leak prevention strategies and address long-standing gaps in entropy-based detection models.
Expect wider adoption over the next 6–12 months as organizations replace legacy scanners and integrate automated revocation workflows.
Secrets do not stay hidden. The Betterleaks secrets scanner finds them before attackers do.

