Artificial intelligence is rapidly reshaping the cybersecurity landscape, and one of the most compelling shifts right now is AI-assisted penetration testing with Kali Linux. For years, penetration testing has been a hands-on craftequal parts technical skill, patience, and deep familiarity with a growing arsenal of security tools.
Traditionally, penetration testers lived in the terminal. Every reconnaissance scan, enumeration attempt, or exploitation step required carefully typed commands, precise flags, and an understanding of what the tool would actually do once executed. One wrong parameter could waste hours or worse, disrupt a production system. Now something interesting is happening.
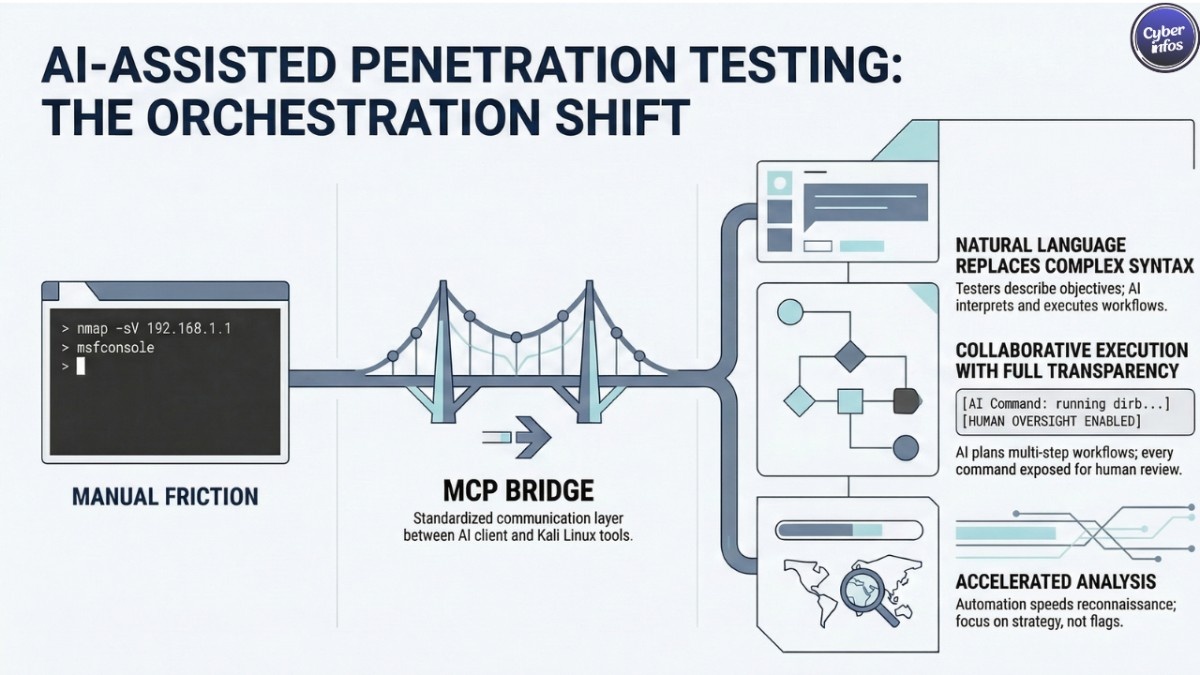
Recent integrations between Kali Linux, Claude AI, and the Model Context Protocol (MCP) are starting to change how security professionals approach offensive security work. Instead of manually chaining together tools, testers can interact with an AI system using natural language prompts while the AI plans and executes commands directly inside a Kali Linux environment.
Think about what that means in practice. A tester describes the objective, the AI assembles the workflow, and the tools begin running.
The result is a workflow that dramatically reduces friction. Experienced professionals can move faster, while newcomers learning ethical hacking get guidance that used to come only from mentors or years of trial and error.
In this article, we explore how AI-assisted penetration testing with Kali Linux works, how the Kali Linux Claude AI integration operates through the Model Context Protocol pentesting architecture, and why AI penetration testing automation is quickly becoming one of the most talked-about developments in modern cybersecurity operations. And frankly, it’s not hard to see why.
The Evolution of Penetration Testing
Penetration testing has always been equal parts science and craft.
Security professionals rely on specialized tools and controlled attack techniques to identify weaknesses before malicious actors find them. Platforms like Kali Linux have long served as the central operating system for these activities, offering hundreds of tools for reconnaissance, vulnerability scanning, exploitation, and post-exploitation analysis.
But here’s the part most people outside the field underestimate: the workflow is complicated.
A typical engagement can involve dozens of commands across multiple tools. Each command requires flags, parameters, and careful interpretation of output. Tools like Nmap, Gobuster, and Metasploit are powerful—but they assume the user knows exactly what they’re doing. For beginners, the learning curve can feel brutal.
Memorizing command syntax alone takes time. Understanding when and why to run those commands takes even longer. And while documentation exists, most real progress still comes from experience.
This is where AI-assisted penetration testing with Kali Linux begins to reshape the process.
By introducing artificial intelligence into penetration testing workflows, security professionals can automate repetitive or procedural tasks while still maintaining control over the environment. The AI acts less like an autopilot and more like an intelligent assistant sitting next to the tester.
What’s striking here is the shift in how instructions are delivered.
Instead of typing multiple commands manually, testers can describe objectives in natural language. The AI interprets the request, selects appropriate tools, executes commands, and then summarizes the results.
That’s the core idea behind AI penetration testing automation. And for many security teams, it represents a meaningful productivity shift.
Understanding the Kali Linux Claude AI Integration
A key innovation making this workflow possible is the Kali Linux Claude AI integration.
At its core, this integration allows the Claude AI model to communicate directly with a Kali Linux system and control penetration testing tools running inside it. The AI becomes an orchestration layer one that understands both human instructions and technical tooling.
So instead of manually typing commands into the terminal, a tester might simply enter a prompt like:
“Scan the target website and identify open ports and directories.”
The AI interprets the objective, determines which tools are appropriate, builds the required commands, and executes them inside the Kali Linux environment.
This is where AI-assisted penetration testing with Kali Linux becomes genuinely powerful.
Rather than forcing users to memorize complex command syntax, the AI generates commands automatically while still displaying them. That transparency matters. Testers can see exactly what is being executed, review the logic, and learn from the workflow.
In other words, the system doesn’t hide the technical layer it exposes it.
And that’s an important distinction. Fully opaque automation tends to make security professionals uneasy, for obvious reasons.
The Kali Linux Claude AI integration instead creates a collaborative model. Human expertise guides the testing strategy, while the AI handles the procedural mechanics.
Think of it less as replacing the tester and more as giving them a very fast research assistant.
What Is the Model Context Protocol (MCP)?
At the center of this entire system sits the Model Context Protocol pentesting framework, usually referred to simply as MCP.
The Model Context Protocol is an open standard designed to allow AI models to interact with external tools, applications, and data sources through a structured interface. Instead of writing custom integrations for every individual tool, MCP creates a standardized communication layer.
That may sound abstract at first. But the practical implications are significant.
Within a penetration testing environment, MCP allows an AI model to communicate directly with Kali Linux tools. The protocol effectively turns those tools into callable services the AI can access when planning a task.
The Model Context Protocol pentesting architecture typically operates using a client-server design.
- The AI model acts as the client.
- The MCP server runs on the Kali Linux system.
- Security tools are exposed through the MCP server.
When the AI receives a user prompt, it converts that request into structured instructions and sends them to the MCP server. The server executes the required commands on the Kali machine, collects the results, and sends them back to the AI for interpretation.
This design enables AI-assisted penetration testing with Kali Linux while still maintaining visibility into every command being executed.
And that’s not just a technical detail it’s a trust requirement. Security professionals need to know exactly what their systems are doing.
Architecture of AI-Assisted Pentesting
The architecture behind AI-assisted penetration testing with Kali Linux typically revolves around three primary layers.
Each layer plays a distinct role in turning a natural language prompt into an actual penetration testing workflow.
User Interface Layer
This is where the human interaction happens.
The tester communicates with the system through an AI interface such as Claude Desktop or a similar application. Instead of writing commands, the tester describes objectives, targets, or investigative questions.
For example:
“Identify subdomains and enumerate exposed services.”
The interface forwards this request to the AI model.
Simple enough.
AI Intelligence Layer
The second layer is where AI penetration testing automation actually takes place.
The AI analyzes the prompt, evaluates the context of the engagement, and determines which tools should be used. It then constructs a testing plan sometimes a surprisingly detailed one including which commands to run and in what order.
Here’s where it gets interesting. The AI is not simply executing single commands. It can plan multi-step workflows that include scanning, enumeration, and follow-up analysis. That kind of orchestration normally requires a human operator.
Execution Layer
The final layer is the Kali Linux environment itself.
Through the Kali Linux Claude AI integration, the AI communicates with the MCP server running on the Kali system. The MCP server executes commands, gathers output from the tools, and sends structured responses back to the AI. The workflow becomes a continuous loop:
Prompt → AI planning → Tool execution → Result analysis → Follow-up actions.
And when it works well, the process feels almost conversational.
Key Tools Used in AI-Assisted Pentesting
One reason AI-assisted penetration testing with Kali Linux works so effectively is the enormous ecosystem of security tools already available within Kali Linux.
These tools have been refined for years by security professionals, researchers, and open-source contributors. The difference now is orchestration.
Through the Model Context Protocol pentesting system, the AI can coordinate multiple tools automatically, selecting them based on the objective described in the prompt. Some of the most commonly used tools include the following.
Nmap
Nmap remains one of the most widely used network scanning tools in cybersecurity.
It identifies open ports, detects running services, and gathers information about network hosts. In traditional workflows, penetration testers manually design Nmap scans depending on the situation.
In AI penetration testing automation, the AI can launch scans automatically, adjust parameters, and interpret the results. But that’s not the whole story. The AI can also decide what to do next based on what Nmap discovers.
Gobuster and Dirb
Gobuster and Dirb are widely used for directory and file discovery on web servers.
These tools brute-force potential directories to uncover hidden resources admin panels, backup files, exposed APIs that might not appear in normal navigation.
Through AI-assisted penetration testing with Kali Linux, the AI can run these enumeration tools and immediately analyze the results to determine whether additional investigation is necessary. Sometimes that means pivoting to other tools. Sometimes it means digging deeper.
Nikto
Nikto is a classic web server vulnerability scanner that looks for outdated software versions, insecure configurations, and known vulnerabilities.
Within AI penetration testing automation, Nikto scans can be triggered automatically once the AI detects a web server during reconnaissance. It’s a logical next step in the workflow.
Hydra and John the Ripper
Hydra and John the Ripper are widely used for credential testing and password cracking.
When appropriate and authorized the AI can initiate these tools to test password strength or identify weak authentication mechanisms. And yes, these tools still require careful oversight.
Metasploit Framework
The Metasploit Framework remains one of the most powerful exploitation platforms available to security professionals.
Using AI-assisted penetration testing with Kali Linux, the AI can analyze vulnerabilities discovered during scanning and recommend potential Metasploit modules for testing.
That said, exploitation is where human judgment becomes especially important. Automation can suggest paths forward. Deciding whether to take them is another matter entirely.
Benefits of AI-Assisted Penetration Testing
The growing adoption of AI-assisted penetration testing with Kali Linux brings several meaningful advantages for cybersecurity professionals. And some of them go beyond simple convenience.
Lower Barrier to Entry
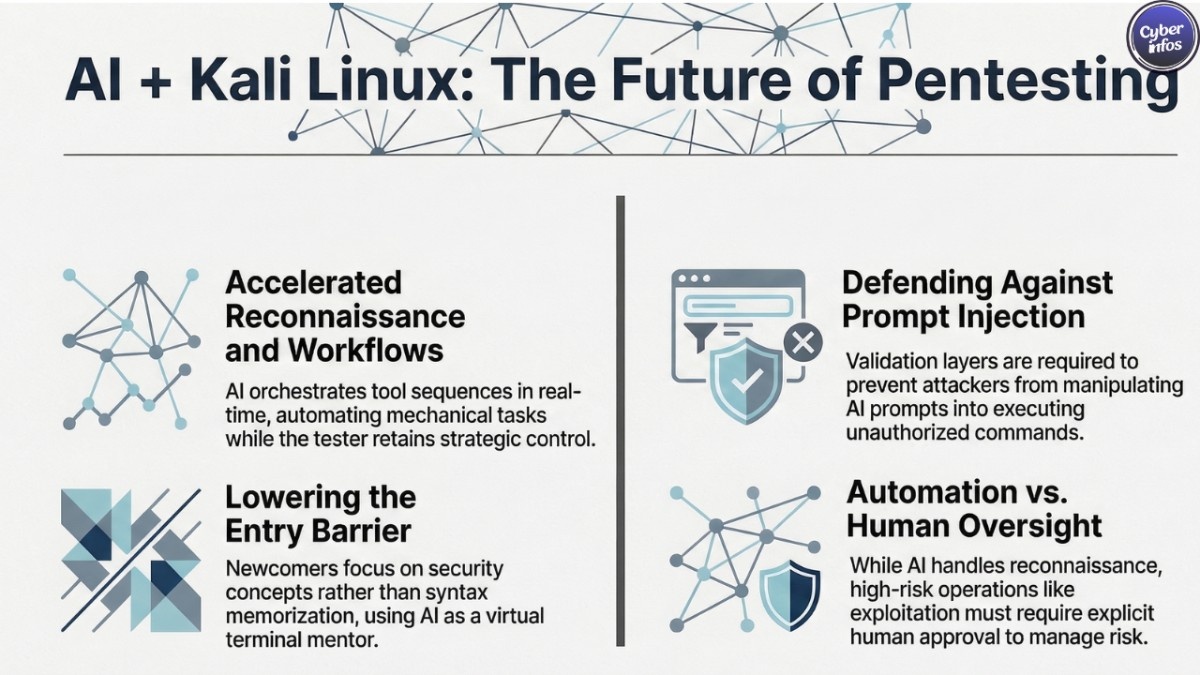
One of the most immediate benefits is accessibility.
For newcomers entering the cybersecurity field, penetration testing can feel overwhelming. The sheer number of tools and the syntax required to use them creates a steep entry barrier.
Through AI penetration testing automation, users can focus more on understanding security concepts rather than memorizing commands. That’s a big shift for training and education.
Faster Testing Workflows
Automation dramatically speeds up reconnaissance and enumeration stages of penetration testing.
Instead of manually launching each tool, the AI can orchestrate entire workflows, running tools sequentially while analyzing results in real time. The tester remains in control, but the mechanical work moves faster. Much faster.
Improved Learning Experience
There’s also a learning advantage. Because the AI explains the commands it runs, users gain visibility into how professional penetration testing workflows operate. Over time, that exposure builds deeper understanding.
In many ways, the Kali Linux Claude AI integration acts like a virtual mentor sitting beside the terminal. And not a bad one, either.
Consistency and Accuracy
Automation can also reduce simple human mistakes. Commands are generated with correct syntax, scans run with consistent parameters, and results are structured for easier analysis.
That consistency can be particularly useful during large engagements where dozens of hosts must be tested.
Security Considerations
Despite the clear advantages, AI-assisted penetration testing with Kali Linux introduces its own set of security concerns.
And security professionals are right to think carefully about them. Allowing an AI system to execute commands inside a penetration testing environment requires strong safeguards and oversight.
Prompt Injection Attacks
Prompt injection is one of the most discussed risks when deploying AI systems connected to tools.
Attackers may attempt to manipulate AI prompts or inject malicious instructions that cause the AI to execute unintended commands.
The Model Context Protocol pentesting architecture must include validation layers and strict command controls to reduce this risk. Otherwise the automation becomes a liability.
Tool Permissions
Not every tool should be accessible to the AI at all times.
Security teams should carefully define which tools the AI can access and under what circumstances. Overly broad permissions could allow unintended actions or data exposure. Least privilege still matters even when AI is involved.
Human Oversight
Even with AI penetration testing automation, high-risk operations should require explicit human approval.
Exploitation, privilege escalation, and lateral movement are powerful techniques. They shouldn’t run automatically without operator review. That’s the uncomfortable truth about automation: speed increases risk if oversight disappears.
Logging and Auditing
Comprehensive logging is essential. All prompts, executed commands, and outputs should be recorded. This ensures traceability during engagements and provides an audit trail if something goes wrong.
And in professional penetration testing, documentation is almost as important as the test itself.
The Future of AI in Ethical Hacking
The rise of AI-assisted penetration testing with Kali Linux signals a broader shift happening across the cybersecurity industry.
AI systems are becoming increasingly capable of orchestrating complex workflows, identifying vulnerabilities, and assisting security teams in real time. And we’re only at the early stages.
As the Kali Linux Claude AI integration continues to evolve, more advanced capabilities will likely emerge. These could include automated vulnerability prioritization, intelligent attack path mapping, and AI-driven remediation guidance.
Meanwhile, the Model Context Protocol pentesting framework is positioned to become a widely adopted standard for connecting AI systems with security tools.
That standardization matters. It means new tools can plug into the ecosystem without reinventing integration layers.
For security professionals, students, and red team operators, the combination of AI systems and traditional penetration testing tools represents a powerful productivity platform.
But let’s be realistic. AI will not replace human expertise in cybersecurity. What it will do very effectively is amplify it.
Final Thoughts
The integration of artificial intelligence into penetration testing marks a significant milestone for cybersecurity operations.
Through AI-assisted penetration testing with Kali Linux, security professionals can use AI to automate repetitive tasks, interpret complex outputs, and streamline workflows that once required dozens of manual commands.
The Kali Linux Claude AI integration, powered by the Model Context Protocol pentesting architecture, creates a bridge between natural language interaction and powerful security tooling. Testers can describe objectives conversationally while still maintaining full visibility into the commands being executed behind the scenes. And that’s the key balance: automation with transparency.
As AI penetration testing automation continues to mature, it will play an increasingly central role in how security teams operate. For aspiring ethical hackers and experienced professionals alike, understanding how to combine AI capabilities with traditional penetration testing tools will quickly become a core skill.
Because the real shift isn’t the tools themselves. It’s the speed at which attackers and defenders can now move. And in cybersecurity, speed changes everything.

