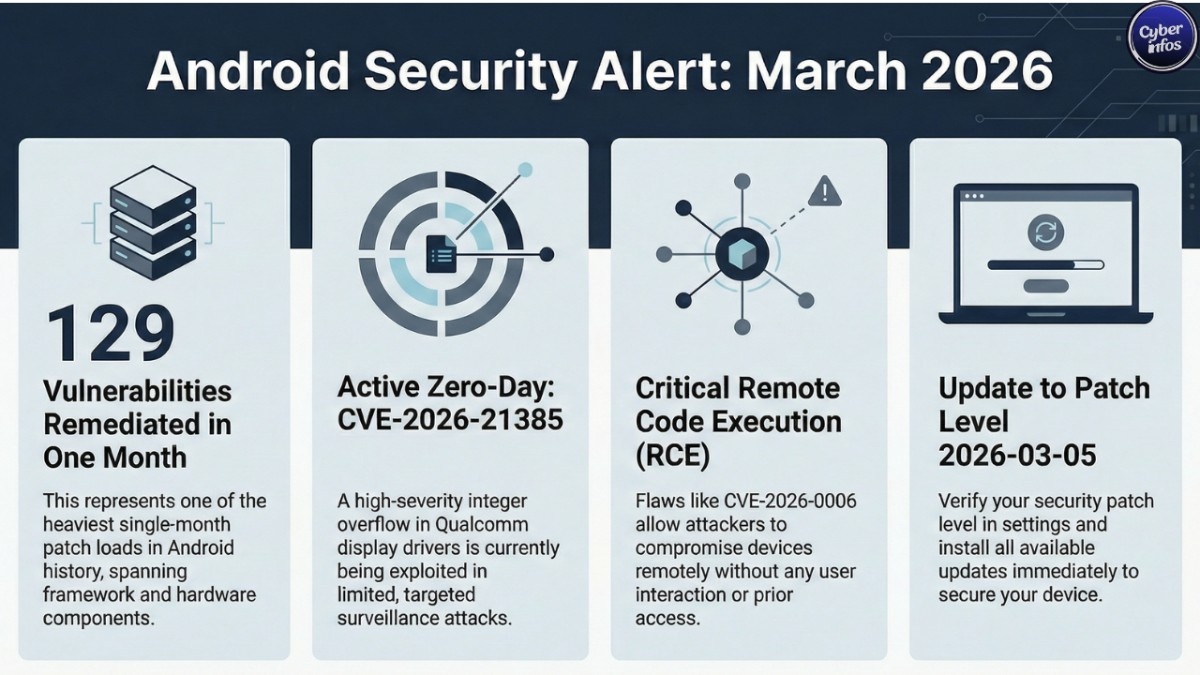
Google has released the March 2026 Android Security Update, and this one isn’t minor housekeeping. The company patched 129 vulnerabilities across the Android ecosystem one of the heaviest single-month patch loads we’ve seen in recent years.
The headline issue is an actively exploited zero-day, CVE-2026-21385, affecting Qualcomm display components. According to Google’s March 2026 Android Security Bulletin and Qualcomm advisories, the flaw has already been used in limited, targeted attacks in the wild. That last part matters.
This update goes well beyond routine fixes. It addresses critical Remote Code Execution (RCE), Elevation of Privilege (EoP), and kernel-level vulnerabilities that, under the right conditions, could allow attackers to compromise devices without any user interaction at all.
In this report, we break down what happened, how the zero-day works, who is at risk, and what you should do immediately to secure your device.
What Happened: March 2026 Android Security Update Breakdown
Google detailed the vulnerabilities in its official March 2026 bulletin published via the Android Open Source Project (AOSP). The update is divided into two patch levels:
- 2026-03-01 — Core Android framework and system fixes
- 2026-03-05 — Kernel and third-party hardware component fixes
The most serious issue, CVE-2026-21385, is a high-severity zero-day in a Qualcomm display driver component. Google confirmed it is being “actively exploited in limited, targeted attacks.” That phrasing is deliberate. It typically signals activity tied to surveillance operations or carefully selected targets not mass malware campaigns.
Key Vulnerabilities Patched
| CVE ID | Component | Type | Severity |
|---|---|---|---|
| CVE-2026-21385 | Qualcomm Display | Memory Corruption (Zero-Day) | High |
| CVE-2026-0006 | System | Remote Code Execution | Critical |
| CVE-2026-0047 | Framework | Elevation of Privilege | Critical |
| CVE-2025-48631 | System | Denial of Service | Critical |
| CVE-2024-43859 | Kernel (F2FS) | Elevation of Privilege | Critical |
| CVE-2026-0037 | Kernel (pKVM) | Elevation of Privilege | Critical |
Among the platform flaws, CVE-2026-0006 stands out. It’s a critical Remote Code Execution vulnerability in the System component that requires no additional execution privileges. In practical terms, an attacker could potentially trigger code execution remotely without needing prior access.
That’s the kind of bug security teams lose sleep over.
Google also patched critical Framework-level EoP flaw CVE-2026-0047, which could allow malicious apps to escalate privileges beyond what users intended. Think about what that means: an app that looks harmless on install quietly acquiring deeper system access behind the scenes.
According to Google’s bulletin and vendor coordination notes, source code patches will be pushed to AOSP within 48 hours a relatively fast turnaround given the scope.
How the Attack Works
The actively exploited CVE-2026-21385 originates from an integer overflow or wraparound bug in a Qualcomm display driver. Integer overflows sound abstract. They’re not.
When a numeric value exceeds the maximum size allocated for it, memory calculations break. The system may allocate less memory than necessary, creating an opening for attackers to overwrite adjacent memory regions. That overwrite can corrupt data structures or redirect execution flow.
Picture a warehouse inventory system miscalculating storage capacity. Boxes get stacked where they don’t belong. Soon, items are spilling into neighboring shelves and now inventory records are compromised.
In this case, the overflow occurs during memory alignment operations inside the display component. Successful exploitation can trigger memory corruption, system instability, and in worst-case scenarios, full device compromise.
And because this flaw lives in hardware-level drivers, it sits beneath many app-layer protections. Security apps won’t necessarily see it. Standard sandboxing won’t stop it. That’s what makes hardware-adjacent vulnerabilities so attractive to sophisticated threat actors (and so frustrating for defenders).
Who Is at Risk?
Devices running Android versions that include vulnerable Qualcomm display components are most exposed.
Specifically:
- Smartphones powered by affected Qualcomm chipsets
- Devices not yet updated to the 2026-03-05 patch level
- Enterprise devices lacking mobile device management (MDM) enforcement
- Users in regions where targeted exploitation campaigns are underway
Google describes exploitation as “limited and targeted.” Historically, that language has preceded broader weaponization once technical details become public. That’s the uncomfortable pattern we’ve seen before.
Zero-days in mobile hardware drivers are rarely the work of casual attackers. They tend to surface in espionage campaigns or high-value targeting operations where stealth and persistence matter more than scale.
If your device hasn’t been patched, you’re effectively trusting that you’re not interesting enough to be targeted. That’s not a strategy.
Expert Analysis: Why This Matters
The sheer volume of this Android Security Update reflects a deeper issue: the Android attack surface keeps expanding.
Hardware-level vulnerabilities especially in GPU drivers, modem firmware, and hypervisor components are becoming increasingly attractive targets. Similar exploitation chains have appeared in past Qualcomm driver flaws and kernel privilege escalation cases documented by security researchers and tracked in the National Vulnerability Database.
What makes CVE-2026-21385 particularly concerning is its position inside the display stack. Display drivers operate close to GPU memory and shared system buffers. Compromise here can become a stepping stone toward broader system control or persistence mechanisms that are difficult to detect. And then there’s the supply-chain angle.
The 66 vendor-specific fixes included in the 2026-03-05 patch level underscore how fragmented Android security has become. The operating system is only part of the equation. Chipset vendors, modem firmware providers, hypervisor developers all contribute components that can quietly expand the attack surface.
From my perspective, this patch volume reflects two realities at once: stronger security auditing and a growing backlog of deep infrastructure weaknesses. Both can be true.
Organizations managing Android fleets shouldn’t treat this as just another monthly update. This is a high-priority remediation cycle.
What You Should Do Right Now
- Check Your Patch Level
Go to Settings → Security → Security Update. Confirm your device shows 2026-03-05. - Install Updates Immediately
If the update is available, install it. Especially if your device runs a Qualcomm chipset. - Enable Google Play Protect
Devices with Google Mobile Services benefit from real-time malware scanning through Google Play Protect. - Restrict App Installations
Avoid sideloading applications from unknown or untrusted sources. Many privilege escalation chains begin with a seemingly benign third-party app. - Enterprise Users: Enforce MDM Compliance
IT administrators should verify patch compliance across fleets and restrict access for outdated devices. - Monitor for OEM Updates
Some manufacturers roll out patches in stages. Check vendor security bulletins regularly until your device reflects the latest patch level.
For official technical details and mitigation guidance, refer to the Android Security Bulletin published via AOSP.
Timeline of Events
- March 3, 2026 → Google publishes March 2026 Android Security Bulletin
- March 3, 2026 → Confirmation of limited zero-day exploitation (CVE-2026-21385)
- Within 48 hours → AOSP source patches scheduled for release
- Ongoing → OEM rollout to supported devices
Final Thoughts
The March 2026 Android Security Update ranks among the most consequential updates in recent memory, addressing 129 vulnerabilities including an actively exploited zero-day in Qualcomm display drivers. Patch adoption will determine how this story ends.
Attackers are already exploiting at least one flaw. The rest are now publicly documented. The window between disclosure and weaponization is shrinking every year.
The question isn’t whether mobile devices are high-value targets. They already are. The real question is whether users and enterprises will patch before opportunistic attackers scale what is currently described as “limited.” History suggests hesitation is expensive.
Stay updated with the latest cybersecurity news at CyberInfos.in

