In cybersecurity, time is everything. The faster you can identify vulnerabilities, the safer your systems remain. Yet, traditional penetration testing has always been time-consuming and repetitive. That’s exactly the gap Pentest Copilot aims to close — by bringing artificial intelligence into the ethical hacker’s workflow in a way that feels both natural and genuinely helpful.
A Smarter, Simpler Approach to Pentesting
What makes Pentest Copilot stand out is its smart integration of large language models like GPT-4 Turbo, which provide real-time, context-aware assistance throughout the testing process. Whether you’re mapping a target system, running reconnaissance, or cleaning up digital footprints after a job, the AI assistant stays with you at every stage.
But it doesn’t take over the work. It simply helps you move faster by suggesting the next logical step, generating commands, and even summarizing what’s already been done. In other words, it takes care of the busywork so you can focus on strategy and analysis — the parts of hacking that actually require human intuition.
Security professionals who have tested Pentest Copilot say it’s more than just a productivity tool. In internal trials, it improved task completion rates by nearly 230% over traditional setups. That efficiency boost comes from a clever mix of chain-of-thought reasoning and retrieval-augmented generation, which helps the AI understand not just what you’re doing, but why.
At its core, Pentest Copilot uses an agentic architecture — essentially, a setup that allows it to directly execute commands inside a penetration testing environment. It ships with a Kali Linux container, preloaded with the tools most pentesters already use, and can be accessed right from your browser. You can connect through a terminal, SSH, or even noVNC, depending on your workflow.
For those who often juggle multiple projects, the tool’s workspace management system is a blessing. It lets you create and handle separate pentesting sessions, each isolated and customizable. There’s even VPN integration, allowing secure remote access to testing environments, which is ideal for distributed security teams or consultants working across networks.
Customization is another strength. Through its settings, users can select or swap out specific tools and scripts, building a setup that mirrors their preferred workflow. Unlike more rigid AI pentesting systems, Pentest Copilot adapts to you — not the other way around.
Key Features at a Glance
- AI-Guided Assistance: Get contextual suggestions for reconnaissance, exploitation, and post-exploitation tasks.
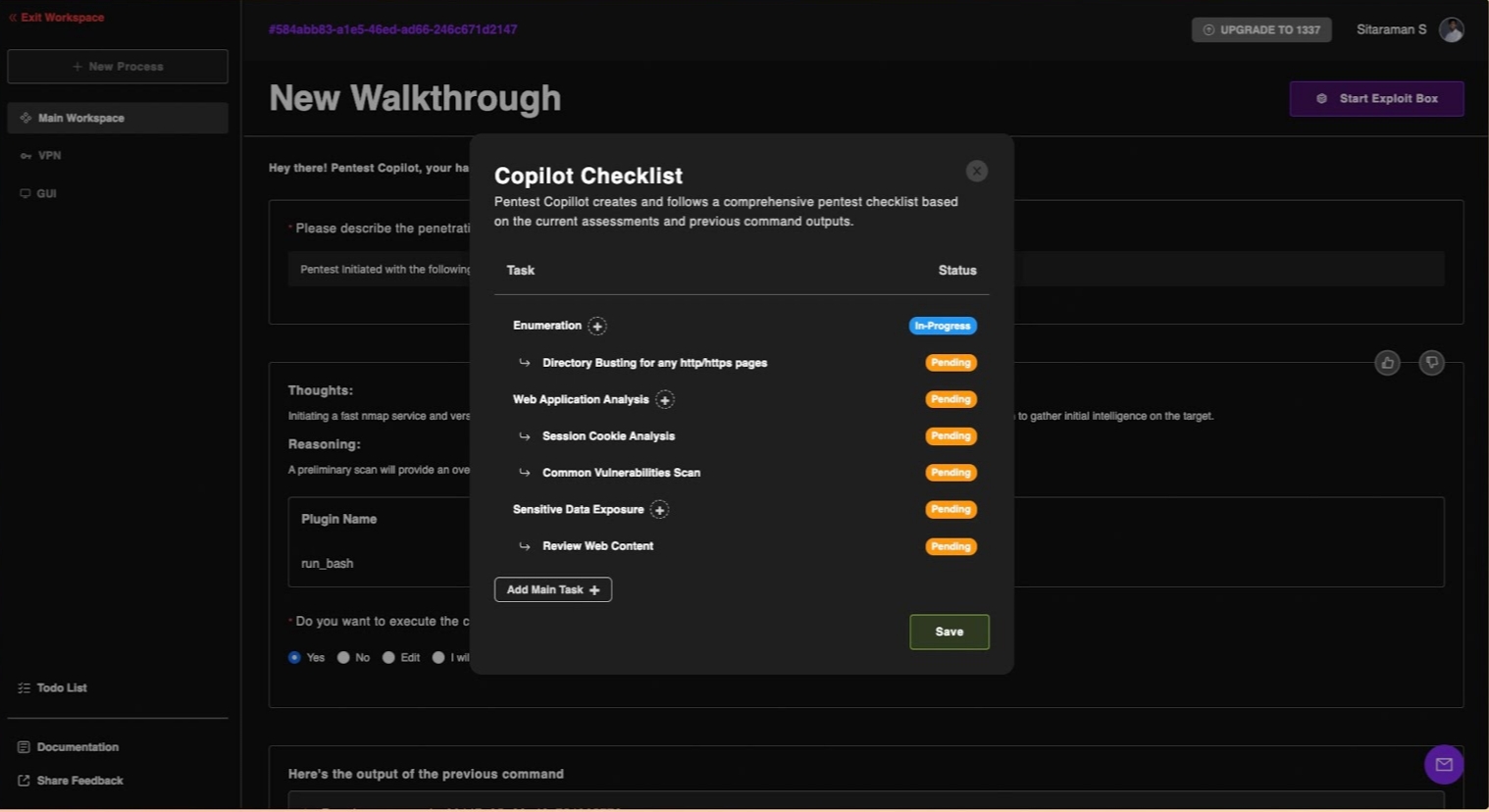
- Todo List Management: Keep track of attack vectors and next steps with automatically generated to-do lists.
- Exploit Box: Work inside a Kali container that’s ready to go, complete with all essential tools.
- Integrated Terminal: Execute commands and monitor results directly from your browser workspace.
- Custom Tool Selection: Configure your environment based on preferred toolchains and testing methods.
- VPN and Workspace Support: Manage multiple isolated sessions securely, without juggling separate setups.
Each of these features is built with one purpose: to let pentesters focus on what really matters — finding and fixing vulnerabilities.
How It Performs in Real-World Scenarios
In hands-on testing, Pentest Copilot has proven to be more than theory. During live demos — including a boot-to-root challenge on TryHackMe’s RootMe lab — it handled complex tasks with surprising agility. The AI generated useful command sequences, summarized findings, and even helped update checklists on the fly. Testers reported a nearly 50% drop in response times, which, in cybersecurity, can mean the difference between prevention and disaster.
Compared with older tools like PentestGPT, Pentest Copilot offers tighter integration between the testing environment and the AI engine. It’s also better at managing multiple steps in sequence, thanks to improved orchestration logic and efficient file handling. The result is a smoother, more intuitive pentesting experience.
The system also connects with external resources like ExploitDB and aligns its findings with the MITRE ATT&CK framework, ensuring every vulnerability is properly categorized and actionable.
Getting Started is Straightforward
Installing Pentest Copilot is refreshingly simple. Once you clone its GitHub repository, deployment is handled through Docker Compose, and the setup script walks you through environment configuration, including your API keys. After that, the service runs locally on your browser with no extra fuss.
You’ll need at least 8 GB of RAM to run the integrated Kali container smoothly — understandable given how resource-intensive some tools can be. Within minutes, you’re ready to start exploring or performing a full penetration test with AI assistance built right in.
Why It Matters
As of late 2025, Pentest Copilot is quickly gaining traction within the cybersecurity community. Its open-source foundation means it’s continuously evolving, with new updates and community-driven enhancements arriving regularly.
More importantly, it represents something bigger — a shift toward AI-augmented security testing, where human expertise and machine intelligence work together, not against each other. The goal isn’t to automate hackers out of a job; it’s to free them from the tedious, repetitive parts of pentesting so they can focus on creativity, logic, and defense.
If cybersecurity is an arms race, tools like Pentest Copilot are helping the good guys move faster. And that’s something every security team can get behind.
Final thoughts
The rise of Pentest Copilot marks a turning point in how ethical hackers approach their craft. By combining the precision of AI with the intuition of human expertise, it bridges the gap between automation and creativity. What once took hours can now be done in minutes — not by replacing professionals, but by amplifying their capabilities.
As cyber threats continue to evolve, tools like Pentest Copilot prove that innovation in security isn’t just about new exploits or defenses — it’s about working smarter. For ethical hackers, security analysts, and enterprises alike, this AI-powered copilot represents the next logical step toward faster, more intelligent, and more adaptive cybersecurity testing.

